Unmanaged switches seem harmless: plug them in, connect devices, and the network “just works.” The real problem is that their simplicity hides serious risks. When one fails, you cannot see what is happening inside the switch, so troubleshooting slows down, security gaps widen, and the hidden cost of downtime rises quickly.
Check: Why Do Managed Network Switches Enterprise Outperform Unmanaged Ones?
What Is an Unmanaged Switch and Why Is It Risky?
An unmanaged switch is a basic Ethernet device that links servers, workstations, and printers without any configuration interface. It learns MAC addresses and forwards traffic automatically but offers no VLANs, QoS, or monitoring features. That lack of control is the main risk: administrators cannot segment traffic, enforce policies, or inspect the data path.
In an enterprise setting, this turns every port failure or loop into a guessing‑game incident. You see symptoms like “device offline” or “slow network,” but the switch itself cannot report why. The low sticker price also tempts teams to overload these units in core or aggregation roles, where a single failure can cascade across the entire LAN.
How Do Unmanaged Switch Failures Impact Network Visibility?
Unmanaged switches deliver almost no visibility into their internal state. They typically show only basic LED indicators—link or no link—while the rich data that managed switches expose (error counters, discards, throughput, and broadcast levels) remains hidden. When a unit degrades, flickers, or drops ports intermittently, operators must rely on indirect evidence instead of real metrics.
This forces IT to test cables, NICs, and upstream devices one by one, which dramatically increases the time to isolate the culprit. Without performance history, teams also miss early‑warning signs such as rising error rates, MAC‑table overflows, or port congestion. As a result, what could be a minor degradation becomes a prolonged outage simply because the switch cannot “tell” what is wrong.
Why “Plug and Play” Creates Hidden Security Vulnerabilities?
The “plug and play” model assumes that anyone can connect anything to any open port, and that assumption is its core security flaw. Unmanaged switches provide no port security, MAC filtering, or 802.1X authentication, so rogue devices such as unauthorized laptops, wireless access points, or infected IoT gear can join the network with minimal friction.
Because these switches also lack VLANs and segmentation, attackers can flood broadcasts, trigger MAC‑table floods, or even position themselves between devices to snoop or tamper with traffic. In regulated environments such as finance, healthcare, or data centers, that unmanaged corner can undermine the entire security posture and compromise compliance even if the rest of the network is tightly controlled.
How Do Unmanaged Switches Increase Downtime Costs?
Unmanaged‑switch failures dramatically increase downtime costs because there is no remote way to confirm whether the root cause is a faulty port, bad cable, or a marginal switch. Teams must physically inspect, swap, or reboot hardware until the symptom disappears, which often requires multiple site visits and repeated service calls. This indirect, trial‑and‑error approach elongates the mean time to repair and multiplies user disruption.
Beyond the obvious loss of revenue, prolonged downtime brings hidden expenses: overtime, support backlog, data‑entry rework, SLA penalties, and damage to customer trust. In critical environments, even tens of minutes of disruption can translate into significant financial impact once all follow‑on costs and remediation efforts are factored in.
How Can You Troubleshoot Unmanaged Switch Failures Without Visibility?
Troubleshooting an unmanaged switch is largely indirect and empirical. A proven method begins by isolating the switch: move suspected devices directly to a known‑good managed switch or router and test connectivity. If the problem disappears, the original unmanaged unit is likely faulty, overloaded, or mislooped.
The next step is divide‑and‑conquer: test one port at a time, validate cables with a cable tester, and watch for LED‑status anomalies. If the switch overheats, emits unusual noises, or exhibits intermittent link drops across multiple ports, replacement is usually more cost‑effective than further diagnosis. Good network design—such as avoiding cascaded unmanaged units and limiting one unmanaged switch per rack—helps contain the blast radius and speeds up fault isolation.
Why Is Lack of Monitoring the Hidden Cost of Unmanaged Gear?
Enterprises rely on tools such as SNMP, syslog, NetFlow, and NPM platforms to monitor health, detect anomalies, and plan capacity. Unmanaged switches cannot provide these metrics, so operations teams lose visibility into port errors, discards, bandwidth utilization, and loop detection. This blind spot turns what should be an early warning into a full‑blown incident.
Over time, the lack of monitoring pushes organizations into a reactive support model. Instead of proactive alerts and trend‑driven maintenance, IT depends on user tickets and manual checks. Mean time to detect and mean time to resolve grow, and the hidden cost of downtime overtakes the small price difference between managed and unmanaged units. Visibility becomes the real cost‑saver, not the cheapest hardware.
Unmanaged vs Managed Switch Impact at a Glance
When Should You Replace Unmanaged Switches with Managed Units?
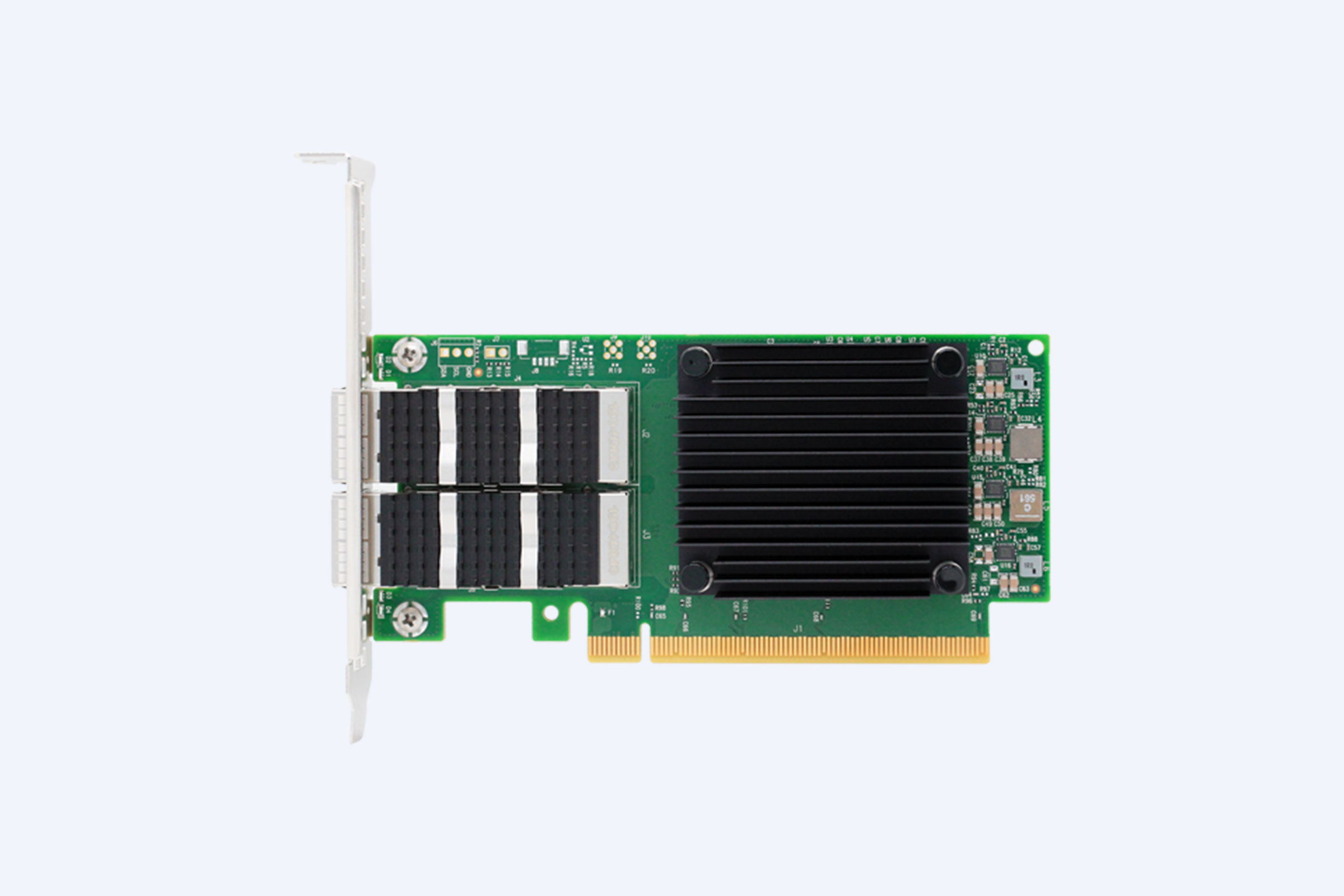
Replace unmanaged switches whenever visibility, security, or resilience matter. Typical triggers include frequent unexplained slowdowns, repeated unplanned outages, or the introduction of critical workloads such as VoIP, video conferencing, SCADA, or cloud‑connected applications. Managed switches support VLANs, QoS, port mirroring, and SNMP, turning opaque segments into predictable, observable links.
Organizations that standardize managed or lightly‑managed switches in core and distribution layers also gain centralized configurations, remote firmware updates, and consistent port‑level policies. For high‑availability or regulated environments, these capabilities are not optional extras but operational necessities that justify the modest upfront premium over unmanaged units.
How Can IT Solution Providers Reduce Risk from Unmanaged Gear?
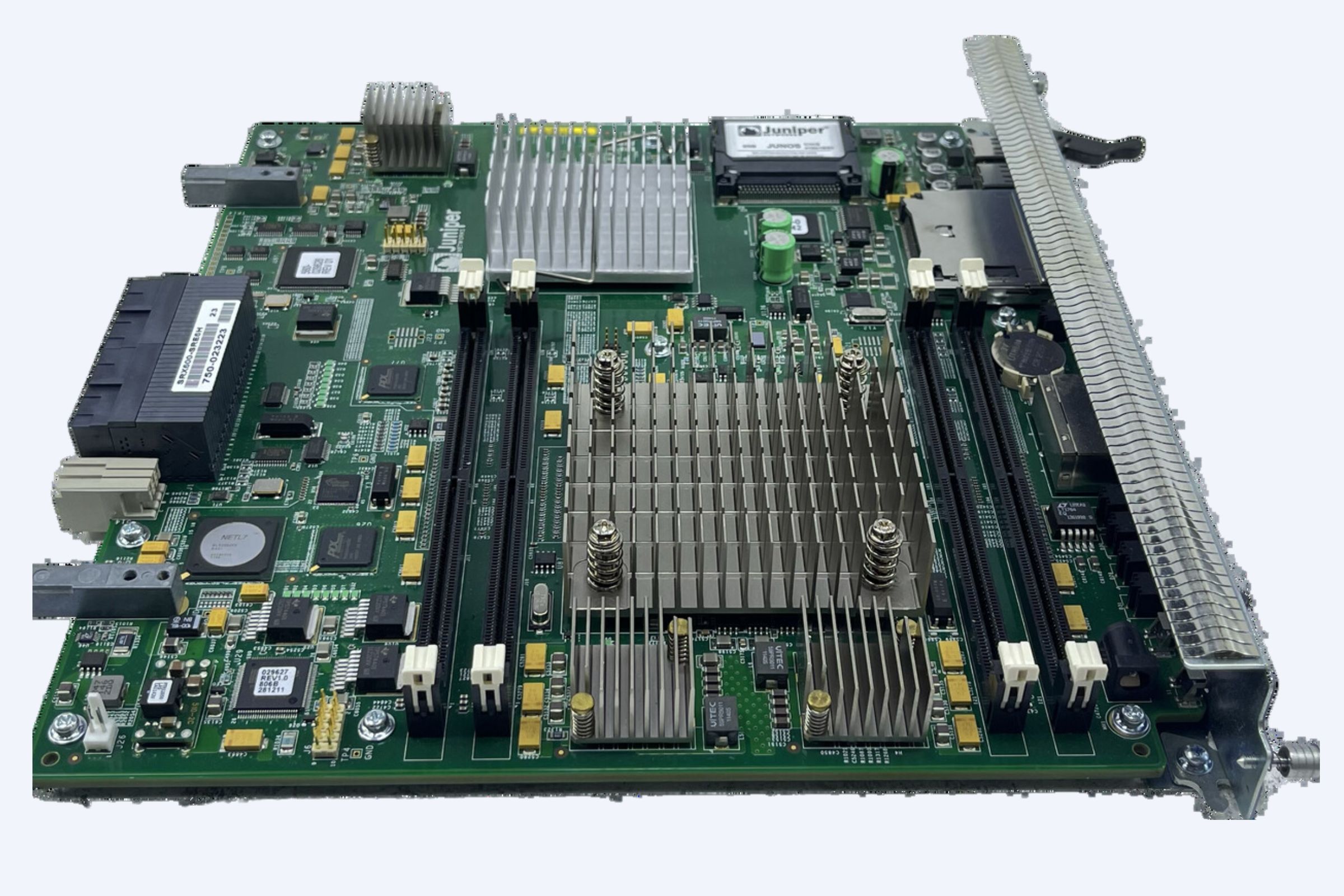
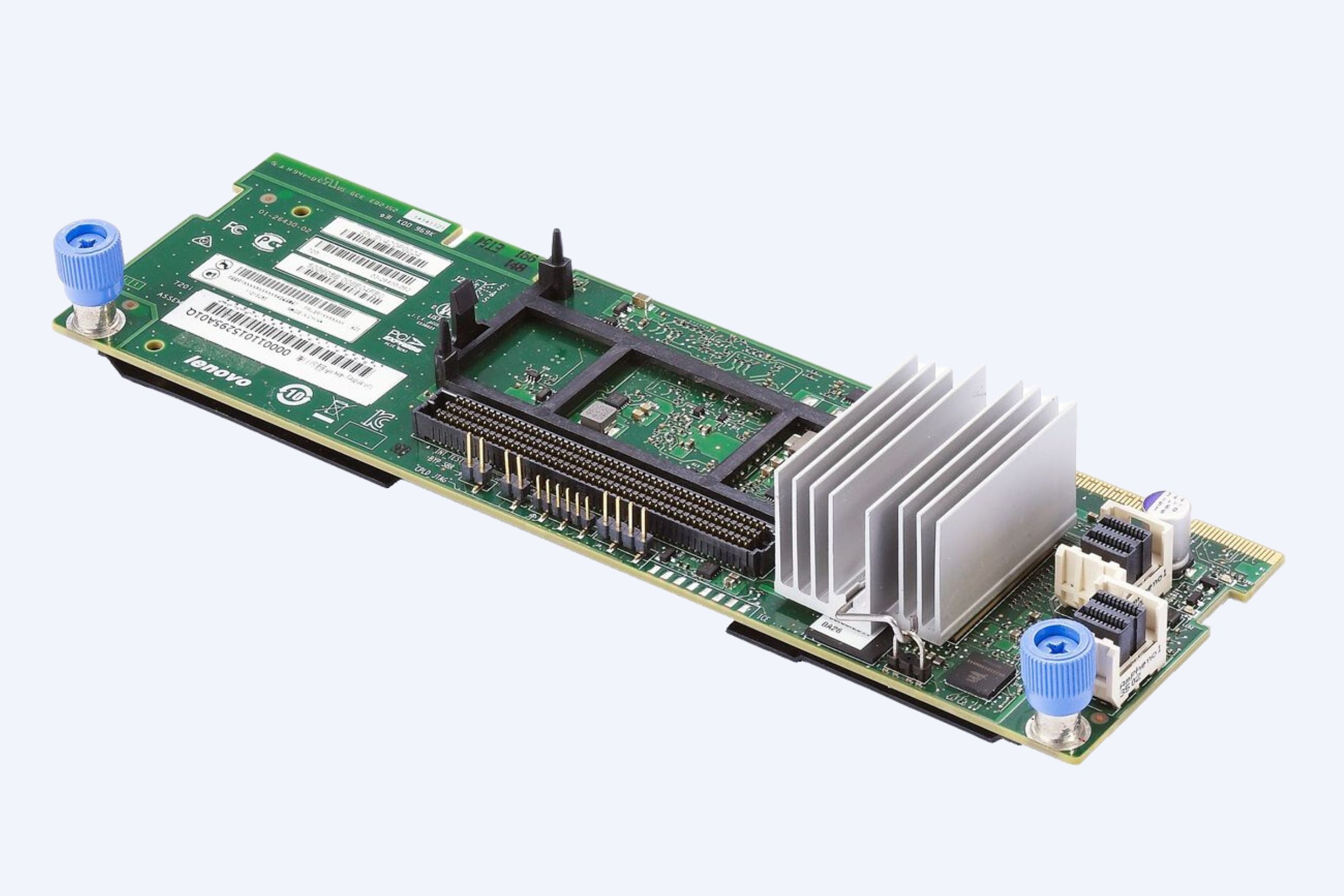
Professional IT solution providers and system integrators can reduce unmanaged‑switch risk by limiting their use to low‑criticality edge segments and deploying managed switches wherever business‑critical traffic flows. They also document network topologies, enforce vendor and model standards, and align switches with enterprise‑grade hardware from families such as Cisco, HPE, and H3C.
WECENT, as an authorized IT equipment supplier and agent for Dell, Huawei, HP, Lenovo, Cisco, and H3C, offers tailored switch portfolios that match different risk profiles and budgets. By pairing managed switches with professional design and deployment guidance, WECENT helps enterprises avoid the false economy of cheap unmanaged gear and build observable, secure networks from the rack outward.
WECENT Expert Views
“In many organizations, unmanaged switches are treated as disposable consumer hardware, but when they sit in the data path of business‑critical traffic, they become single points of failure. The true cost of unplanned downtime usually far exceeds the price difference between an unmanaged and a managed switch. At WECENT, we help clients design hybrid infrastructures that use managed switches where visibility and security matter most, while still delivering cost‑effective solutions through OEM and customized hardware. Seeing the network is not a luxury—it is a business‑continuity requirement.”
How Does Unmanaged Switch Risk Affect Virtualization and Cloud Environments?
In virtualization and cloud‑style infrastructures, unmanaged switches magnify risk because storage‑area traffic, live‑migration data, and hypervisor control planes all share the same LAN. Without monitoring, a single overloaded unmanaged switch can silently introduce latency, packet loss, or jitter, appearing as “VMs are slow” or “storage is lagging” instead of a clear network fault.
Performance troubleshooting becomes extremely difficult. Administrators chase CPU, memory, and storage issues while the real problem is an invisible switch handling 100‑port‑of‑Gigabit‑Ethernet traffic with no visibility or QoS. In hybrid‑cloud scenarios, the same unmanaged links can destabilize SD‑WAN, VPNs, or SaaS‑connectivity paths, leading to spotty application performance and persistent user complaints.
How Can Switch Visibility Improve Mean‑Time‑to‑Repair?
A managed switch exposes error counters, interface states, and traffic‑mirror ports that feed into monitoring and analytics tools. When a port error counter spikes, an SNMP trap or NMS dashboard can alert the operations team before users notice performance degradation. This converts random ticket‑based repair into a data‑driven incident‑response workflow.
Features such as port mirroring also enable deep packet inspection from a single analysis port, letting engineers capture and decode traffic without taking services offline. In environments supplied and supported by providers such as WECENT, this visibility translates into faster SLA‑compliant resolutions, reduced penalty exposure, and more predictable uptime for downtime‑sensitive workloads.
How Does Unmanaged Gear Impact Enterprise IT Equipment Strategy?
Unmanaged switches encourage a fragmented, ad‑hoc IT equipment strategy. Because each model behaves differently and lacks remote management, firms often end up with mixed vendors, unknown firmware versions, and inconsistent cabling. This complicates upgrades, audits, and compliance checks and makes disaster‑recovery documentation unreliable.
Enterprise‑class IT equipment suppliers like WECENT help clients avoid this by recommending standardized, managed switch families that align with broader server, storage, and GPU strategies. This approach ensures that networking remains a visible, integral part of the IT stack instead of a low‑budget, dark corner that unpredictably amplifies risk during incidents.
Which Alternatives Should You Consider Instead of Unmanaged Switching?
Instead of relying on unmanaged switches for critical segments, enterprises should consider managed switches, lightly‑managed industrial switches, or purpose‑built edge switches that balance cost and functionality. For example, “light‑managed” switches from Cisco or H3C provide basic SNMP, VLANs, and QoS without the full complexity of enterprise‑grade CLI‑driven platforms.
WECENT supports this evolution by offering managed and industrial‑grade switches from leading brands, along with consultation on topology design, PoE requirements, and rack‑level cabling. By transitioning core and distribution layers to managed gear, organizations regain visibility, improve security, and reduce the hidden cost of unplanned switch failures across their data centers, branches, and cloud‑connected environments.
Key Takeaways and Actionable Advice
Unmanaged switches may seem convenient and low‑cost, but they create hidden security gaps, reduce visibility, and increase downtime expenses. To minimize risk, standardize managed switches in core, distribution, and any business‑critical edge segments. Reserve unmanaged units only for non‑production, low‑risk areas and avoid cascading them behind each other.
Work with an authorized IT equipment supplier such as WECENT to design and deploy a switch portfolio that aligns with your server, storage, and GPU roadmap. WECENT offers Dell, Huawei, HP, Lenovo, Cisco, and H3C hardware, OEM‑style customization, and full support, helping enterprises modernize their network infrastructure without sacrificing reliability or visibility.
Frequently Asked Questions
Can my organization still use any unmanaged switches at all?
Yes, but only in low‑criticality, non‑business‑critical segments such as temporary workstations, lab corners, or small office extensions. Unmanaged units should never sit in the data path of production servers, storage, VoIP, or cloud connectivity.
What are the first signs an unmanaged switch is failing?
Common signs include intermittent link drops on multiple ports, random device disconnections, constant renegotiation between devices and switch ports, overheating cases, and noticeable performance drops that vanish when bypassing the switch.
Why should I buy switches from an authorized IT equipment supplier like WECENT?
Authorized suppliers guarantee genuine hardware, manufacturer warranties, and access to firmware and support baselines. WECENT also provides OEM‑style and custom solutions, helping enterprises align switches with existing server, storage, and GPU stacks for a cohesive, visible infrastructure.
How quickly can downtime from an unmanaged switch become expensive?
Even a few minutes of downtime can be costly: when combined with IT labor, overtime, SLA penalties, lost transactions, and support backlog, total downtime cost can dwarf the price difference between an unmanaged and a managed switch.
Can managed switches help during network‑upgrade projects?
Yes. Managed switches simplify upgrades with remote configuration, VLAN preservation, and consistent port‑level policies. They also integrate with network‑monitoring platforms, making cut‑over planning and post‑upgrade validation far more predictable than with unmanaged gear.