The distribution layer in a three‑tier network acts as the “middle man” between access and core switches, aggregating links from multiple access‑layer devices and enforcing security, routing, and QoS policies before traffic reaches the core. It improves performance and stability by filtering unnecessary broadcast traffic, applying ACLs, and controlling routing decisions so that only necessary data reaches the high‑speed backbone. This layer is essential for scalable, secure, and policy‑driven enterprise networks and data‑center designs supplied by professional IT‑equipment vendors such as WECENT.
Check: How Do Core, Distribution, and Access Switches Build Scalable 3-Tier Network Architectures?
What Is the Distribution Layer in a Network?
The distribution layer is the middle tier of a hierarchical network that connects the access layer to the core. It aggregates links from many access switches, performs routing and policy enforcement, and filters traffic so that only necessary data reaches the core. This layer is key for scalability, security, and maintaining consistent service quality across enterprise networks, data centers, and campus environments.
In a three‑tier architecture (access–distribution–core), the distribution layer provides routing between VLANs, aggregates traffic from multiple access switches, and applies security and QoS rules. Modern enterprise networks often use high‑performance Layer 3 switches at this tier, including devices from Cisco, HPE Aruba, and Huawei, which support advanced routing, redundancy, and policy‑management features. Professional IT‑equipment suppliers like WECENT help organizations select and integrate matching distribution‑layer hardware that aligns with core and access infrastructure, ensuring long‑term reliability and support.
How Does the Distribution Layer Aggregate Links?
The distribution layer aggregates links by collecting multiple physical uplinks from access switches and presenting them as fewer, higher‑capacity logical uplinks to the core. This aggregation reduces the number of active paths at the core, simplifies routing, and keeps the backbone lean and performant. By consolidating traffic, the distribution layer improves scalability and reduces the risk of cabling and configuration complexity.
Common link‑aggregation techniques at the distribution layer include port channels or LACP to combine multiple Ethernet links into a single logical channel, stacking switches into a single logical unit, and multi‑chassis link aggregation (MLAG) for active‑active redundancy. These methods increase bandwidth, provide failover if a link fails, and eliminate loops while maintaining a clean topology. Authorized IT‑equipment suppliers such as WECENT can help design and provision the right distribution‑layer switches, transceivers, and cabling that match core and access hardware, ensuring consistent performance and compatibility.
How Does the Distribution Layer Enforce Network Policies?
The distribution layer enforces network policies by applying rules for routing, filtering, and quality of service before traffic enters the core. This layer becomes the policy boundary where security, access control, and traffic treatment are implemented consistently across the organization. By centralizing policy enforcement, the distribution layer reduces the risk of configuration drift and unsecured traffic reaching critical systems.
Policy‑enforcement mechanisms include access control lists (ACLs) that permit or deny traffic based on IP, MAC, port, or protocol; quality of service (QoS) that prioritizes latency‑sensitive applications; and VLAN routing that defines which segments can communicate. Distribution‑layer switches also commonly support advanced security features such as DHCP snooping, ARP inspection, and IP‑source‑guard to prevent spoofing attacks. Working with an authorized IT‑equipment supplier like WECENT ensures that distribution‑layer hardware is compliant, original, and properly configured to align with enterprise‑wide security and policy frameworks.
Why Is the Distribution Layer Called the “Middle Man”?
The distribution layer is called the “middle man” because it sits between the access layer and the core, mediating traffic flow and decision‑making. It filters and routes traffic from many end‑user devices at the access layer and passes only what is needed onward to the high‑speed core, protecting the core from unnecessary load and maintaining performance. This intermediate role is critical for maintaining stability as networks grow.
Architecturally, the “middle man” function reduces core complexity by offloading VLAN routing, ACL checks, and policy evaluation from the core. It also improves scalability and security, allowing organizations to add new access‑layer segments without redesigning the entire network. In large data centers and campus networks, this role supports modern workloads such as virtualization, AI, and cloud‑ready infrastructures. Professional IT‑solution providers like WECENT help enterprises select distribution‑layer hardware that pairs effectively with core and access infrastructure, ensuring that the “middle man” operates efficiently and securely.
How Does the Distribution Layer Improve Network Performance?
The distribution layer improves performance by limiting unnecessary traffic, optimizing routing, and prioritizing critical applications before they reach the core. It prevents the core from being flooded with broadcast, multicast, and control‑plane traffic, which would otherwise degrade speed and stability. By cleaning and shaping traffic early, the distribution layer helps maintain a responsive and predictable backbone.
Performance gains come from traffic filtering that blocks broadcast storms and unnecessary inter‑VLAN flows, efficient routing protocols that maintain fast convergence, and QoS that assigns bandwidth and priority to critical applications. Link‑aggregation techniques such as LACP, stacking, and MLAG increase bandwidth and provide failover paths without loops. For organizations running latency‑sensitive workloads such as AI inference, real‑time analytics, or cloud‑based services, pairing modern distribution‑layer switches with high‑performance servers and GPUs from WECENT ensures that the entire data path delivers consistent, low‑latency performance at scale.
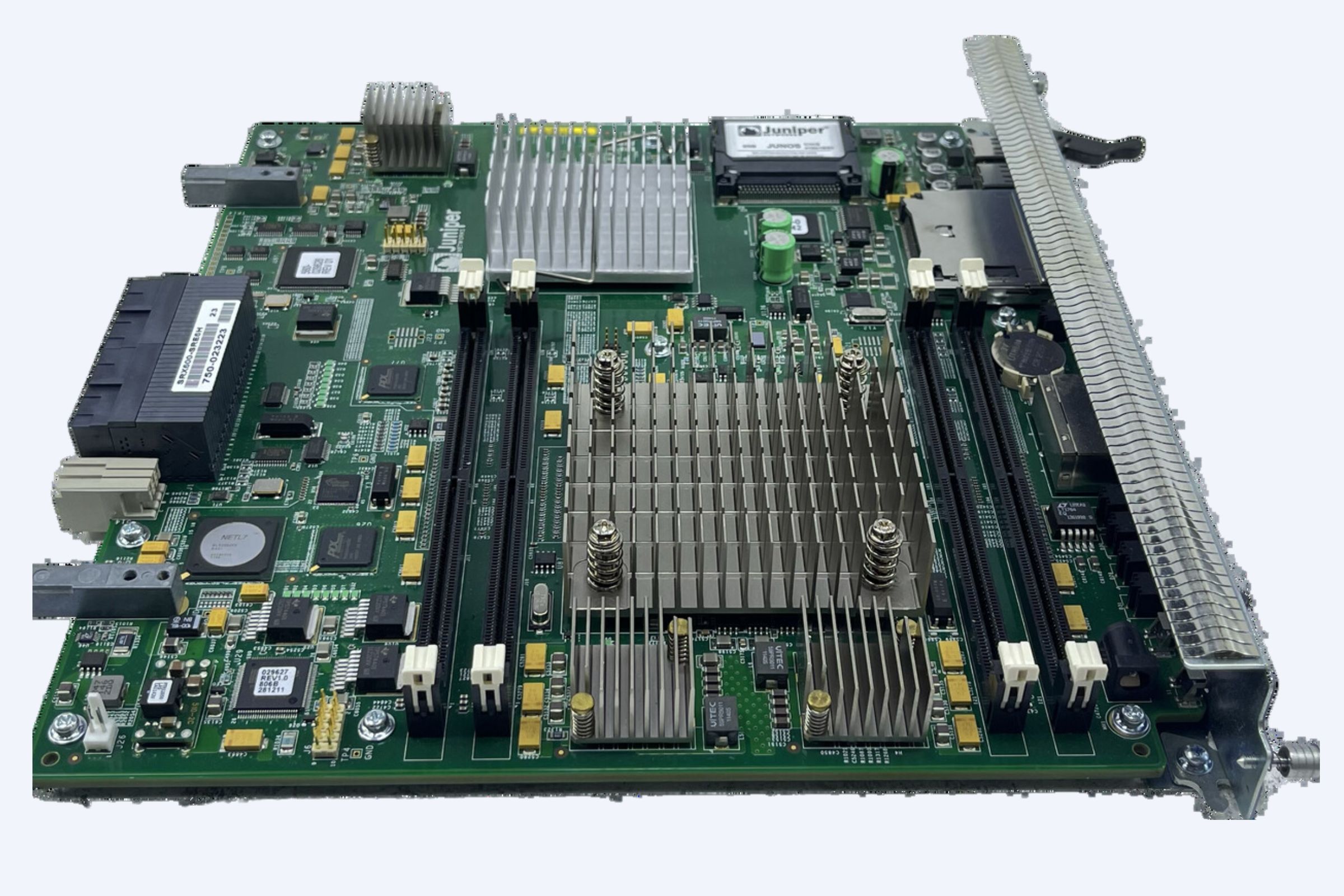
What Hardware Is Typically Used at the Distribution Layer?
Distribution‑layer hardware is usually high‑performance, chassis‑ or modular‑based Layer 3 switches capable of handling large routing tables, many VLANs, and advanced security policies. These switches must be robust enough to aggregate multiple access‑layer links while still meeting the performance and availability requirements of the core. They form the workhorse of the campus or data‑center network.
Typical hardware choices include enterprise‑class Layer 3 switches such as Cisco Catalyst 9000/6500‑series, HPE Aruba CX/6300, and Huawei CE/CX series, as well as chassis‑based systems with multiple line‑card slots for adding ports, optics, or specialized modules. Stacking and virtual‑switching technologies allow multiple physical units to behave as a single logical switch, simplifying management and enhancing redundancy. An IT‑equipment supplier and authorized agent like WECENT can help organizations select matching distribution‑layer switches, fiber‑optic transceivers, and power‑backup options that align with existing Cisco, HPE, Dell, or Huawei infrastructure, ensuring long‑term reliability and support.
How Does Distribution‑Layer Policy Management Scale Across Enterprises?
Distribution‑layer policy management scales across enterprises by centralizing control points that can be replicated across multiple sites and branches. Rather than implementing rules on every access switch, organizations define policies at the distribution layer and propagate them consistently through automation and configuration templates. This approach reduces configuration errors and simplifies auditing.
Scaling strategies include hierarchical policy design using templates for VLANs, ACLs, and QoS that can be reused across different campuses, as well as network automation tools that deploy and verify configuration changes across distribution switches. Role‑based and identity‑aware policies allow dynamic VLAN assignment and security enforcement, even as networks grow. For large‑scale rollouts, IT‑solution providers like WECENT can supply OEM‑ready or customized configurations that align with an organization’s automation framework, ensuring that distribution‑layer switches in different locations behave consistently and comply with corporate security standards.
How Does the Distribution Layer Fit into Three‑Tier Network Design?
The distribution layer anchors the classic three‑tier network design (access–distribution–core), acting as the tier that connects end‑user devices at the access layer to the backbone of the core. It provides structured, policy‑driven routing and segmentation between the two, ensuring that the core remains fast and the edge remains flexible. This separation allows organizations to scale each tier independently.
Within three‑tier design, the access layer connects user devices, printers, and endpoints using Layer 2 switches; the distribution layer aggregates access links, routes between VLANs, and enforces security and QoS policies; and the core layer provides high‑speed, low‑latency backbone connectivity between distribution nodes and external networks. This modular structure supports growth, such as adding more access switches for new users or expanding core capacity for cloud or AI workloads. WECENT’s expertise in enterprise‑server and networking solutions helps customers match distribution‑layer hardware with core and access‑layer gear, ensuring a cohesive architecture that evolves alongside business needs.
What Are the Security Functions of the Distribution Layer?
The distribution layer is a critical security enforcement point, acting as the first line of defense between the edge of the network and the core. It applies security policies such as access control, segmentation, and traffic inspection, helping to contain threats before they spread to sensitive systems. By centralizing these functions, the distribution layer improves visibility and consistency.
Security functions include VLAN segregation and ACL enforcement to prevent unauthorized communication between different departments or user groups, control‑plane protection that limits and filters control‑traffic such as ARP and STP, and integration with security appliances such as firewalls and intrusion‑detection systems. Distribution‑layer switches also collect traffic statistics and logs for investigation and compliance reporting. Using devices that support advanced security features from vendors such as Cisco, HPE Aruba, or Huawei allows organizations to build a zero‑trust‑ready network. Authorized IT‑equipment suppliers like WECENT help procure compliant hardware and guide integration with existing security ecosystems, ensuring policies are consistently enforced across all layers.
How Do You Choose the Right Distribution‑Layer Switch?
Choosing the right distribution‑layer switch depends on capacity, performance, scalability, and integration with existing access and core infrastructure. Organizations must balance port density, Layer 3 capabilities, security features, and manageability to match their workload and growth requirements. A well‑chosen switch can support years of expansion without requiring a redesign.
Key selection criteria include port density and types to ensure enough downlinks for access‑layer switches and uplinks to the core, support for stacking or multi‑chassis technologies that allow active‑active redundancy, and advanced features such as ACLs, QoS, routing protocols, multicast, and security functions. It is also important to align with existing vendor ecosystems and long‑term support models. For organizations planning large‑scale deployments, an IT‑equipment supplier and authorized agent such as WECENT can provide tailored recommendations, competitive pricing, and OEM‑ready configurations that ensure seamless integration with core and access layers.
The table below summarizes typical criteria for selecting a distribution‑layer switch:
How Can You Optimize Distribution‑Layer Design for AI and Cloud Workloads?
For AI and cloud‑ready infrastructure, the distribution layer must be optimized for high bandwidth, low latency, and programmable policy enforcement. This requires switches capable of handling large east‑west traffic flows between servers, GPUs, and storage while still maintaining security and segmentation. Optimized design ensures that compute‑intensive workloads perform reliably.
Optimization guidelines include using high‑speed uplinks such as 25/40/100 GbE to support traffic from multiple GPU‑equipped servers and storage arrays, enabling full Layer 3 capabilities such as advanced routing, ECMP, and VXLAN or EVPN for overlay networks common in cloud and containerized environments, and integrating with orchestration platforms so that network policies align with virtualized workloads and microservices. Partnering with an IT‑equipment supplier such as WECENT enables organizations to match distribution‑layer switches with high‑performance Dell EMC, HPE, Cisco, and NVIDIA GPU hardware, ensuring that the entire infrastructure is ready for AI training clusters, inference farms, and cloud‑native platforms.
WECENT Expert Views
“From a large‑scale infrastructure perspective, the distribution layer is not just about routing traffic—it’s about intelligent policy enforcement that aligns with business risk and workload requirements,” says a senior network architect at WECENT. “When we design three‑tier architectures for our clients, we ensure that distribution‑layer switches are chosen to match both the core and access layers, with enough headroom for future AI, cloud, and virtualization workloads. By integrating these switches with enterprise‑grade servers, GPUs, and storage from Dell, HPE, and Cisco, we help organizations build a resilient, policy‑driven backbone that can scale securely and cost‑effectively.”
Key Takeaways and Actionable Advice
The distribution layer is the intelligence hub of a hierarchical network, responsible for aggregating access‑layer links, routing traffic, and enforcing security and performance policies before data reaches the core. It improves scalability, reduces core complexity, and provides a consistent point for policy management across large enterprises and data centers. To maximize its value, organizations should treat this layer as a strategic design point, not just a connectivity tier.
Key actions include defining clear VLAN and routing policies at the distribution layer, choosing switches with sufficient port density, Layer 3 capabilities, and security features, and aligning hardware selection with core and access infrastructure. Implementing redundancy through stacking, MLAG, or chassis‑based systems, and integrating automation tools for configuration and monitoring, can further enhance reliability. Partnering with an authorized IT‑equipment supplier and professional IT‑solution provider such as WECENT ensures that distribution‑layer hardware is original, compliant, and well‑supported, enabling enterprises to build a secure, scalable backbone for AI, cloud, and long‑term digital transformation.
Frequently Asked Questions
What is the main purpose of the distribution layer?
The main purpose is to aggregate links from the access layer, enforce routing and security policies, and filter traffic before it reaches the high‑speed core, improving performance, scalability, and security.
Can the core layer perform distribution‑layer functions?
Technically yes, but it is not recommended, as it increases core complexity, reduces scalability, and can degrade performance. The distribution layer should offload these functions from the core.
Should every campus have multiple distribution‑layer switches?
Yes, for redundancy and scalability. Multiple distribution‑layer switches typically form pairs or clusters using routing protocols such as HSRP, VRRP, or MLAG to ensure high availability and consistent policy enforcement.
How does the distribution layer relate to VLANs?
The distribution layer routes between VLANs, applies ACLs that control inter‑VLAN communication, and acts as the default gateway for VLANs, ensuring segmentation and security.
Can small businesses use a distribution‑layer design?
Yes—small and mid‑sized businesses can adopt a simplified version of the three‑tier model using fewer switches but still benefit from VLAN routing, policy enforcement, and protected core uplinks.