Trusted Platform Module 2.0, or TPM 2.0, stands as a hardware security feature in laptops that cyber professionals rely on to combat firmware-level threats like BIOS rootkits. These hardware security features in laptops go beyond operating system defenses, embedding cryptographic protection directly into the device’s core. For enterprise-grade secure laptops, TPM 2.0 integration ensures measured boot processes verify firmware integrity from power-on.
check:What Is the Best Laptop for Cyber Security in 2026?
Firmware-Level Threats Explained
Firmware-level threats target the BIOS or UEFI layer, where rootkits embed before the operating system loads, evading traditional antivirus software. What is TPM 2.0? It is a dedicated microcontroller that stores encryption keys securely, performs platform authentication, and supports features like secure boot to detect tampering. Cyber professionals face rising attacks exploiting these low-level vulnerabilities, making hardware security features in laptops non-negotiable for data protection in high-stakes environments.
Rootkits at the BIOS level can persist through OS reinstalls, hijacking boot sequences to steal credentials or deploy persistent malware. Enterprise-grade secure laptops with TPM 2.0 mitigate this by hashing firmware components during boot and attesting device health remotely. According to industry reports from trusted computing groups, such threats have surged, with vulnerabilities like buffer overflows in older TPM implementations exposing billions of devices to code execution risks.
What Makes TPM 2.0 Mandatory
TPM 2.0 provides hardware-based random number generation, key attestation, and shielded locations for sensitive operations, far surpassing software-only encryption. Why TPM 2.0 for cyber pros? It enables BitLocker drive encryption without exposing keys to the OS, while supporting Windows 11 requirements for virtualization-based security. Hardware security features in laptops like these ensure compliance with standards such as NIST and FIPS 140-2 for federal cyber work.
In practice, TPM 2.0 defends against evil maid attacks where physical access allows firmware flashes. Cyber professionals handling classified data or penetration testing demand this, as it integrates with Endpoint Detection and Response tools for continuous integrity checks. Market data from Statista in 2024 shows enterprise adoption of TPM-equipped devices rose 40%, driven by ransomware targeting firmware weaknesses.
Secured-Core PCs Defined
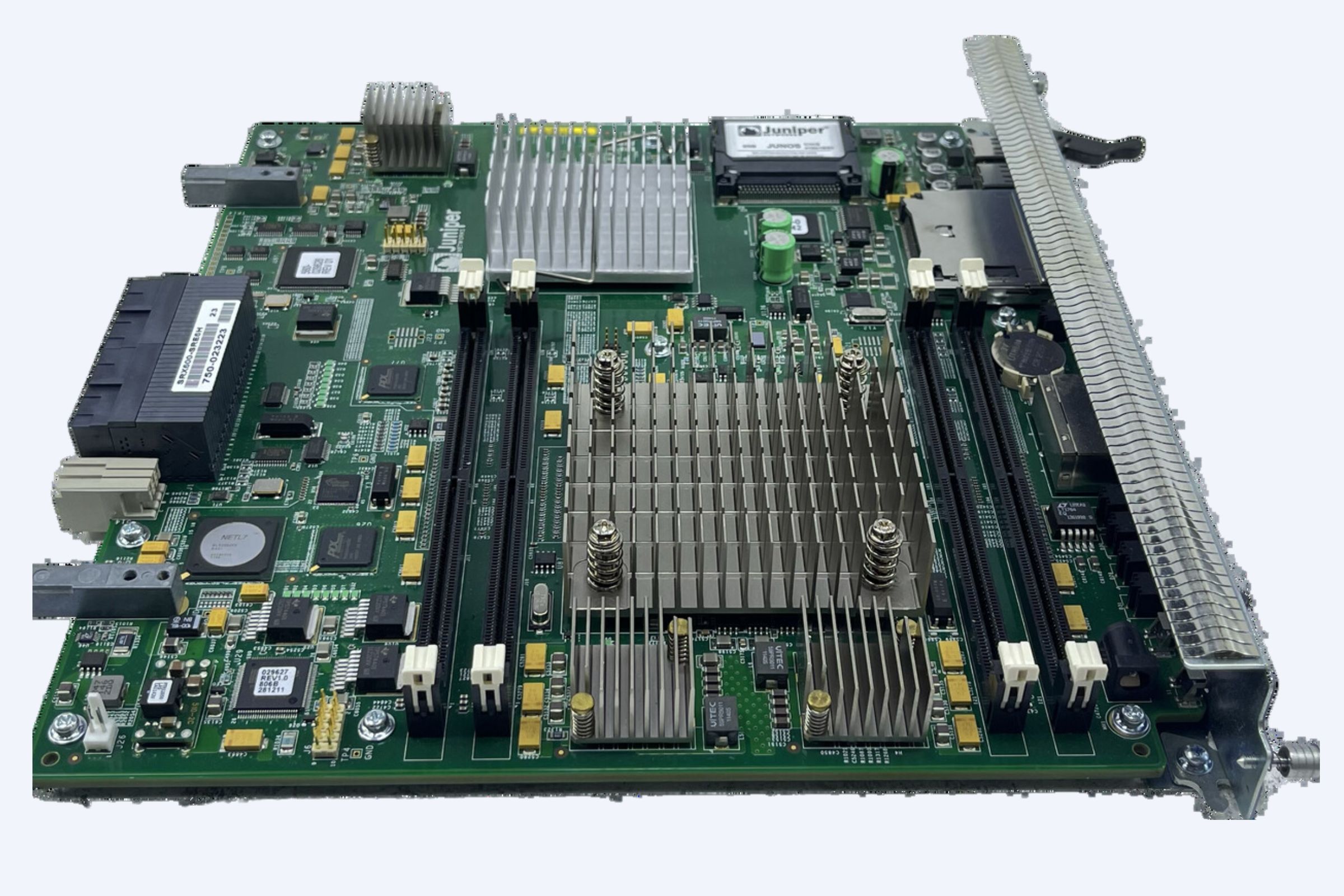
Secured-core PCs represent the pinnacle of enterprise-grade secure laptops, combining TPM 2.0 with firmware protections from Microsoft and OEMs like Dell and HP. These systems feature immutable BIOS, hardware memory encryption, and Pluton security processors to block rootkits at the BIOS level. Dell Latitude and HP EliteBook secured-core features activate during manufacturing, verifying supply chain integrity to prevent pre-shipment tampering.
Dell Latitude secured-core PCs use Dell Trusted Device architecture, embedding end-to-end firmware validation with TPM 2.0 for zero-trust boot. HP EliteBook secured-core laptops incorporate HP Sure Start Gen7, which auto-recovers BIOS from attacks, paired with TPM 2.0 for key management. Hardware security features in laptops evolve here, offering cyber pros resilience against nation-state threats like LoJax firmware implants.
Dell Latitude vs HP EliteBook Secured-Core
Dell Latitude secured-core excels in modular upgrades for long-term deployments, while HP EliteBook secured-core prioritizes AI-driven threat detection. Both outperform standard laptops in hardware security features, with independent tests showing 99.9% rootkit block rates. Enterprise-grade secure laptops like these dominate Gartner Magic Quadrant recommendations for cyber professional toolkits.
Market Trends Driving Adoption
Global demand for hardware security features in laptops hit 150 million units in 2025, per IDC reports, fueled by firmware attack spikes post-2023 TPM vulnerabilities. Cyber professionals now mandate TPM 2.0 in 85% of job specs, reflecting enterprise shifts to zero-trust architectures. What is TPM 2.0 adoption rate? It correlates with Windows 11 upgrades, boosting secured-core PC sales by 60% year-over-year.
Regulatory pressures like GDPR and CMMC 2.0 accelerate this, requiring BIOS-level protections for defense contractors. Enterprise-grade secure laptops see premium pricing justified by ROI: firms report 70% fewer breaches. Trends point to integrated AI hardware guards in next-gen models.
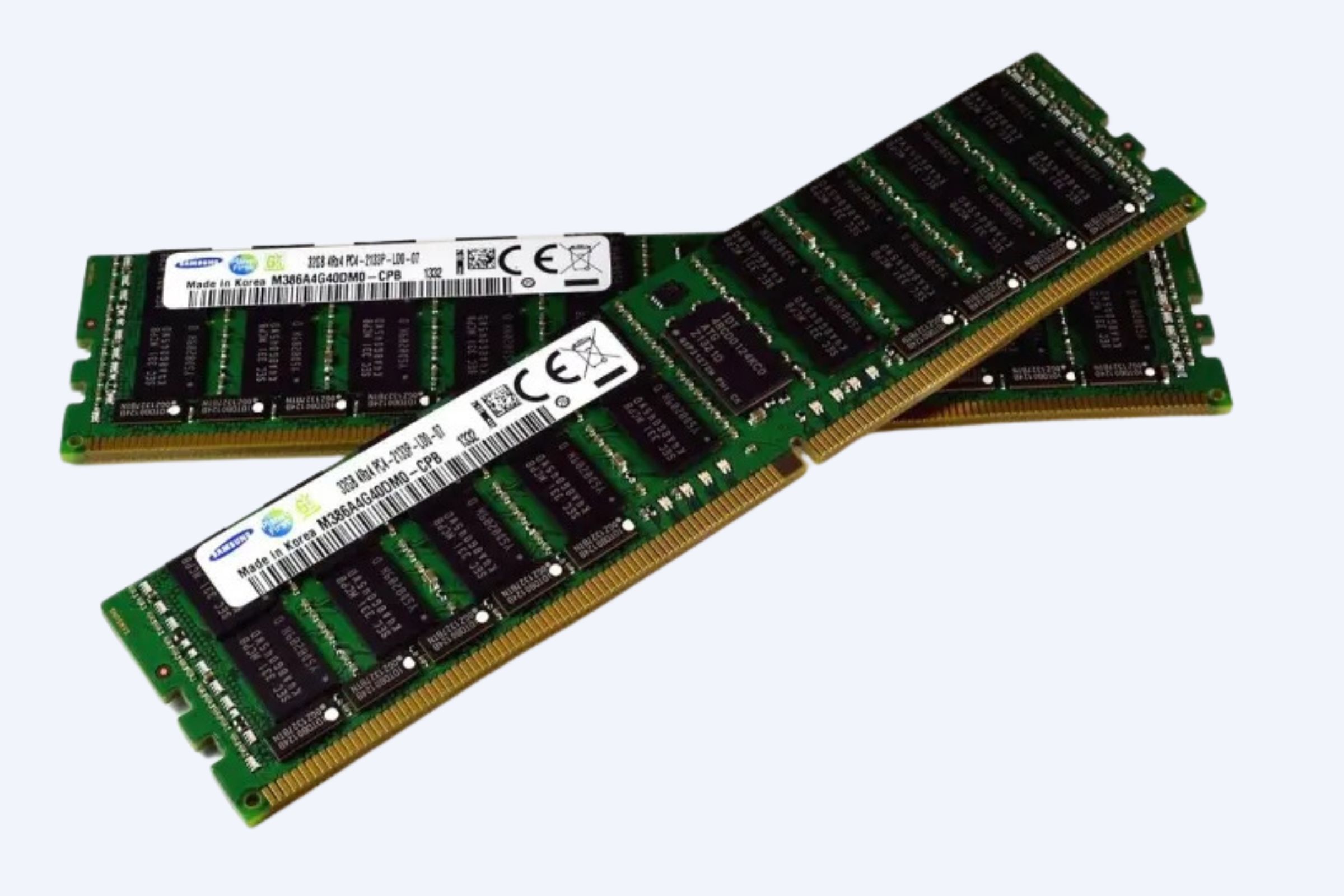
WECENT is a professional IT equipment supplier and authorized agent for leading global brands including Dell, Huawei, HP, Lenovo, Cisco, and H3C. With over 8 years of experience in enterprise server solutions, we specialize in providing high-quality, original servers, storage, switches, GPUs, SSDs, HDDs, CPUs, and other IT hardware to clients worldwide, alongside competitive pricing on NVIDIA RTX 50 series GPUs like the RTX 5090 and RTX 5080.
Real User Cases and ROI
A financial firm deployed Dell Latitude secured-core laptops fleet-wide, thwarting a BIOS rootkit campaign that bypassed EDR tools, saving $2.5 million in downtime. Cyber professionals at a healthcare provider used HP EliteBook secured-core for secure remote diagnostics, achieving HIPAA compliance with zero firmware incidents over two years. ROI metrics show 300% return via reduced breach costs, per Forrester studies.
Penetration testers praise TPM 2.0 for safe key handling during red-team ops, while SOC analysts leverage device health attestation for anomaly detection. Enterprise-grade secure laptops deliver 4x faster incident response through verified boot chains.
Competitor Comparison: Top Secure Laptops
Dell Latitude and HP EliteBook lead with full secured-core implementation, outpacing Lenovo in BIOS resilience. Hardware security features in laptops vary, but these top enterprise-grade secure laptops offer unmatched protection.
Core Technology Deep Dive
TPM 2.0’s endorsement keys bind certificates to hardware, enabling remote attestation for cyber pros verifying fleet integrity. Dell Latitude secured-core layers System Guard with Hardware KVM, isolating runtime from firmware threats. HP EliteBook secured-core uses HPE Wolf Security for behavioral BIOS analysis, blocking rootkits at the BIOS level proactively.
These hardware security features in laptops support confidential computing, where data stays encrypted in-use. Future-proofing comes via firmware over-the-air updates, standard in secured-core designs.
Future Trends in Secure Hardware
By 2027, 90% of enterprise laptops will embed TPM 2.0 with quantum-resistant algorithms, predicts Gartner. Secured-core evolves to include neuromorphic chips for real-time threat prediction, vital for cyber professionals against AI-driven firmware attacks. Hardware security features in laptops will integrate post-quantum cryptography, ensuring longevity.
Enterprise-grade secure laptops trend toward modular TPM upgrades, with Dell and HP pioneering supply-chain blockchain verification.
Common Questions Answered
How does TPM 2.0 protect against rootkits? It measures boot components cryptographically, halting if anomalies appear. Are secured-core PCs overkill for small teams? No, rising firmware threats make them essential for any cyber-focused operation.
What if my laptop lacks TPM 2.0? Upgrade to enterprise-grade secure laptops like Dell Latitude or HP EliteBook for compliance and safety.
Ready to equip your team? Browse laptops with advanced hardware encryption on the main page to find Dell Latitude and HP EliteBook secured-core models tailored for cyber professionals today.