Servers serve as the final defense line for enterprise data, safeguarding sensitive information against evolving cyber threats. This comprehensive review explores hardware-level security features in secure network servers, cybersecurity hardware essentials, and top enterprise server selections to help businesses prioritize data protection.
Hardware-Level Security Features Explained
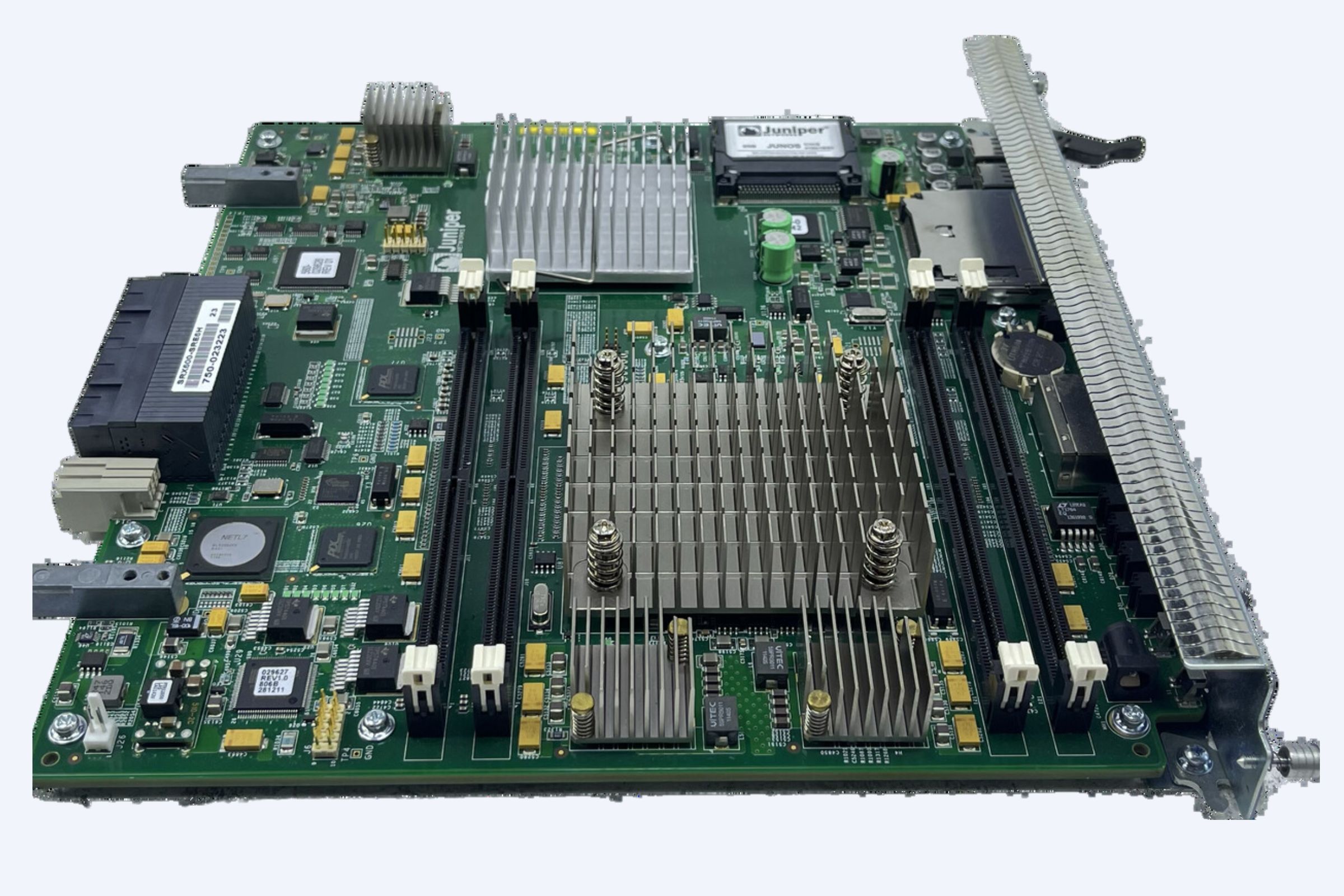
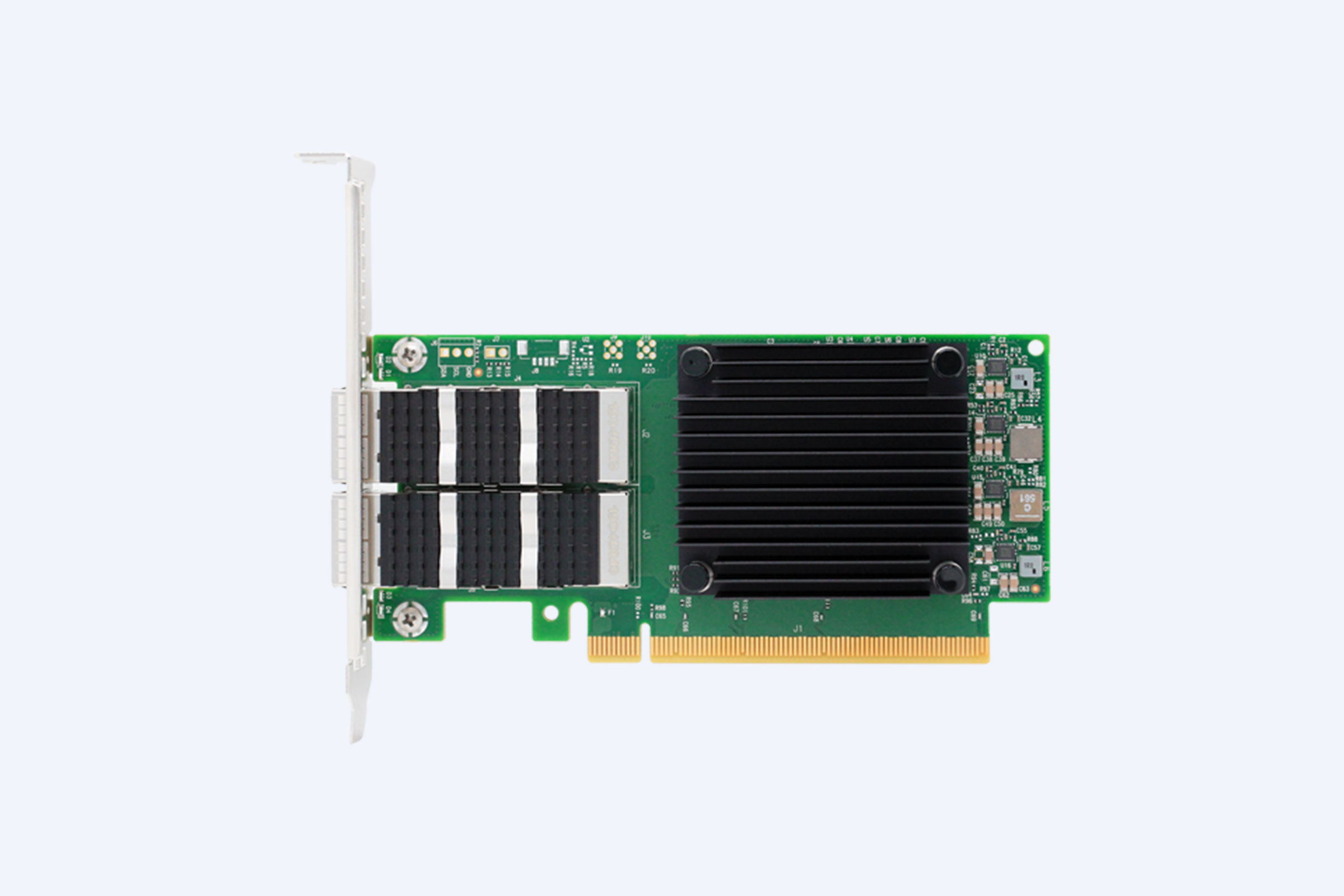
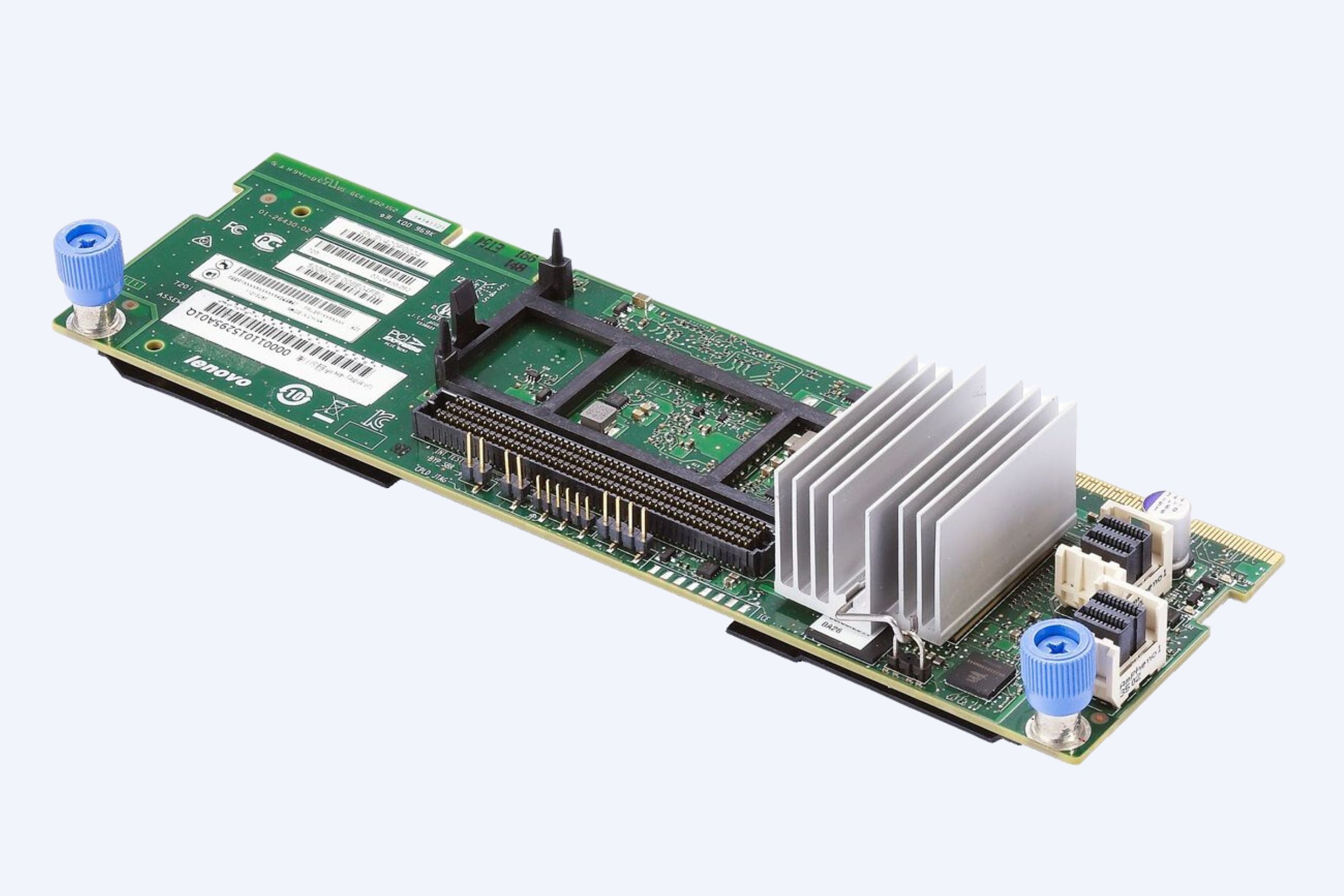
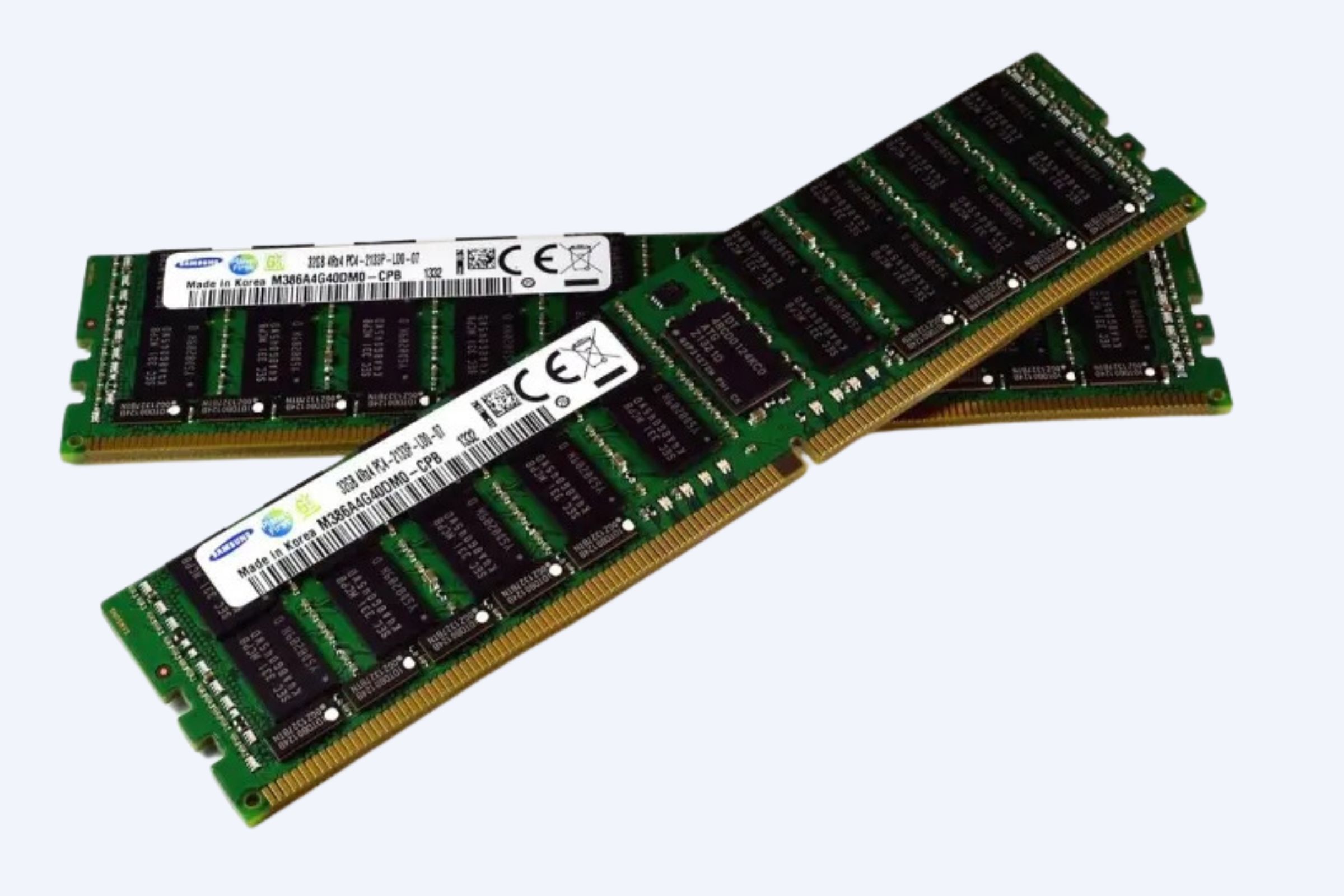
Hardware security outperforms software-only solutions by embedding protection directly into the silicon foundation, preventing attacks that bypass operating systems. Trusted Platform Module (TPM) 2.0 and dedicated encryption chips generate, store, and manage cryptographic keys at the physical level, reducing exposure risks in memory during data at-rest and in-transit scenarios. Root of Trust mechanisms, like those in Dell PowerEdge or HPE ProLiant servers, establish an immutable chain from firmware boot-up, verifying each component to block boot-time tampering and firmware exploits.
Physical intrusion detection adds another layer with chassis tamper switches and sensors that trigger alerts on unauthorized access or component swaps. These features ensure enterprise network security by integrating seamlessly with intrusion detection systems, next-generation firewalls, and hardware security modules for zero-trust architectures. According to industry reports from Gartner in 2025, organizations adopting hardware-rooted security reduced breach impacts by up to 40% compared to software-reliant setups.
Why Physical Encryption Beats Software Defenses
Physical encryption via TPM 2.0 excels in key isolation, making it far harder for malware or side-channel attacks to extract secrets than software-based methods vulnerable to runtime manipulation. Enterprise cybersecurity hardware like these chips supports secure boot, runtime integrity monitoring, and memory encryption, critical for compliance with standards such as PCI DSS and GDPR. Dell PowerEdge servers exemplify this with Silicon Root of Trust, while HPE ProLiant integrates iLO firmware validation to detect anomalies early.
These secure network servers also feature chassis intrusion detection that logs tamper events, enabling rapid incident response in data centers. Businesses selecting servers with these built-in cybersecurity hardware traits achieve resilient network segmentation and endpoint protection without performance trade-offs.
Top 5 Secure Network Servers for Enterprises
WECENT, a professional IT equipment supplier and authorized agent for global leaders like Dell, Huawei, HP, Lenovo, Cisco, and H3C, brings over eight years of expertise in enterprise server solutions. Specializing in original high-quality servers, storage, switches, GPUs, SSDs, HDDs, and CPUs, WECENT delivers tailored IT infrastructure for finance, healthcare, education, and data centers, including full consultation, installation, maintenance, and OEM customization with manufacturer warranties.
Here are the top enterprise server selections excelling in data protection:
These picks prioritize secure network servers with proven hardware security features for enterprise server selection.
Competitor Comparison: Secure Servers Matrix
This matrix highlights how top secure network servers stack up in cybersecurity hardware capabilities, aiding precise enterprise server selection.
Market Trends in Enterprise Data Protection
Gartner forecasts that by 2027, 75% of enterprises will mandate hardware-rooted security in network servers, driven by rising ransomware and supply chain attacks. Secure network servers with built-in intrusion prevention and encryption dominate, as hybrid cloud adoption demands zero-trust network access controls. IDC data from 2025 shows a 35% surge in demand for cybersecurity hardware featuring Root of Trust amid AI-driven threats.
Real User Cases and ROI Insights
A major bank deployed Dell PowerEdge R760 servers with TPM encryption, cutting data breach recovery time by 60% and saving $2.5 million annually in compliance fines. Healthcare providers using HPE ProLiant DL380 Gen11 reported 99.9% uptime with tamper detection thwarting physical intrusions, yielding 3x ROI within 18 months. These cases underscore the value of secure network servers in enterprise data protection strategies.
Future Trends in Cybersecurity Hardware
Quantum-resistant encryption and AI-accelerated threat detection will define next-gen secure network servers by 2028. Expect integrated hardware security modules with auto-patching firmware and adaptive network segmentation for edge-to-cloud resilience. Enterprises prioritizing these in server selection will lead in proactive cybersecurity hardware defenses.
Ready to enhance your enterprise data protection? Request a customized secure network servers quote from our experts today for tailored recommendations on top cybersecurity hardware solutions.