In today’s threat landscape, ransomware is less a fantasy and more a routine risk for businesses of all sizes. A robust backup and recovery strategy is the core defense, helping you restore operations quickly with minimal impact on revenue and reputation. This article explores the 3-2-1 backup principle, dives into immutable storage, and shows how durable hardware behind your backups is essential for true business continuity. You’ll also see a clear path to engage Wecent for a tailored disaster recovery solution.
3-2-1 Backups: A Timeless Rule for Resilience
What it is and why it matters
The 3-2-1 rule states you should have three copies of data, stored on two different media, with one copy kept offsite. This structure reduces recovery risk from device failure, media corruption, or site disasters. When data is compromised at one location, a healthy offsite copy ensures you can rebound quickly. The principle remains strong because it addresses multiple failure modes that plague traditional backups.
For modern environments, 3-2-1 extends beyond simple file copies to include application-consistent backups, index and metadata protection, and rapid restore capabilities. This enhances ransomware resilience by ensuring critical systems can be restored even when primary and secondary copies are damaged. The approach is widely endorsed as a best practice by data protection professionals.
Practical deployment tips
Map critical assets first: identify mission-critical data and systems whose loss would stall operations, then apply 3-2-1 protections to those assets.
Diversify media types: combine on-premises disks or tapes with cloud or immutable offline storage to minimize correlation in failures.
Automate testing: schedule regular recovery drills to verify data integrity and restore times, ensuring readiness when real incidents occur.
Immutable Storage: Locking Data Where It Belongs
What it is and how it helps
Immutable storage prevents data from being altered or deleted for a fixed retention period, even by administrators. This is a key defense against ransomware threats that try to encrypt or erase backups to maximize damage. Immutable safeguards ensure copies survive long enough to be discovered, verified, and restored.
Implementations typically rely on write-once, read-many (WORM) or WORM-like policies in storage systems, combined with strict access controls and auditing. This makes backup data a trustworthy last line of defense that cannot be tampered with during an attack or outage.
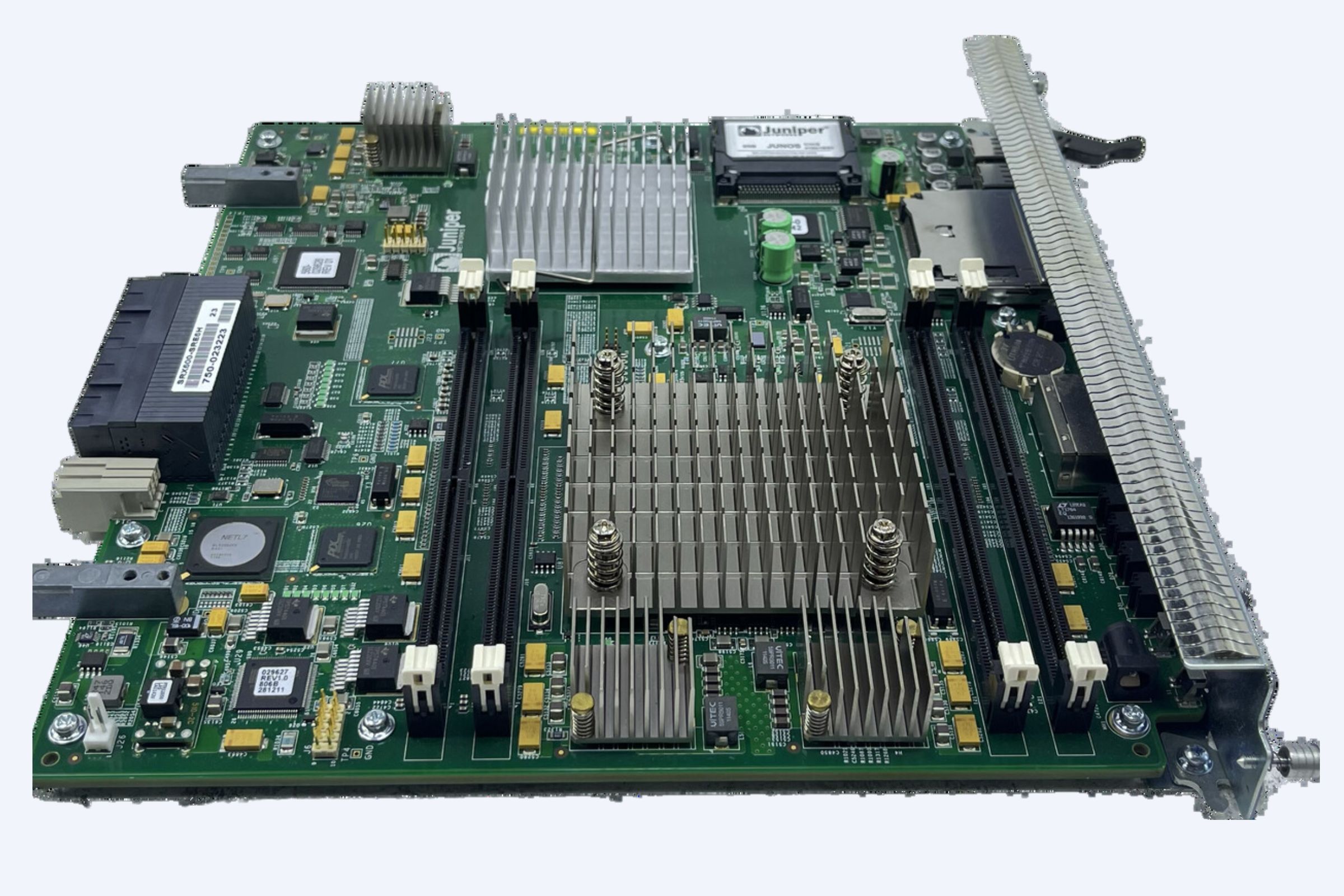
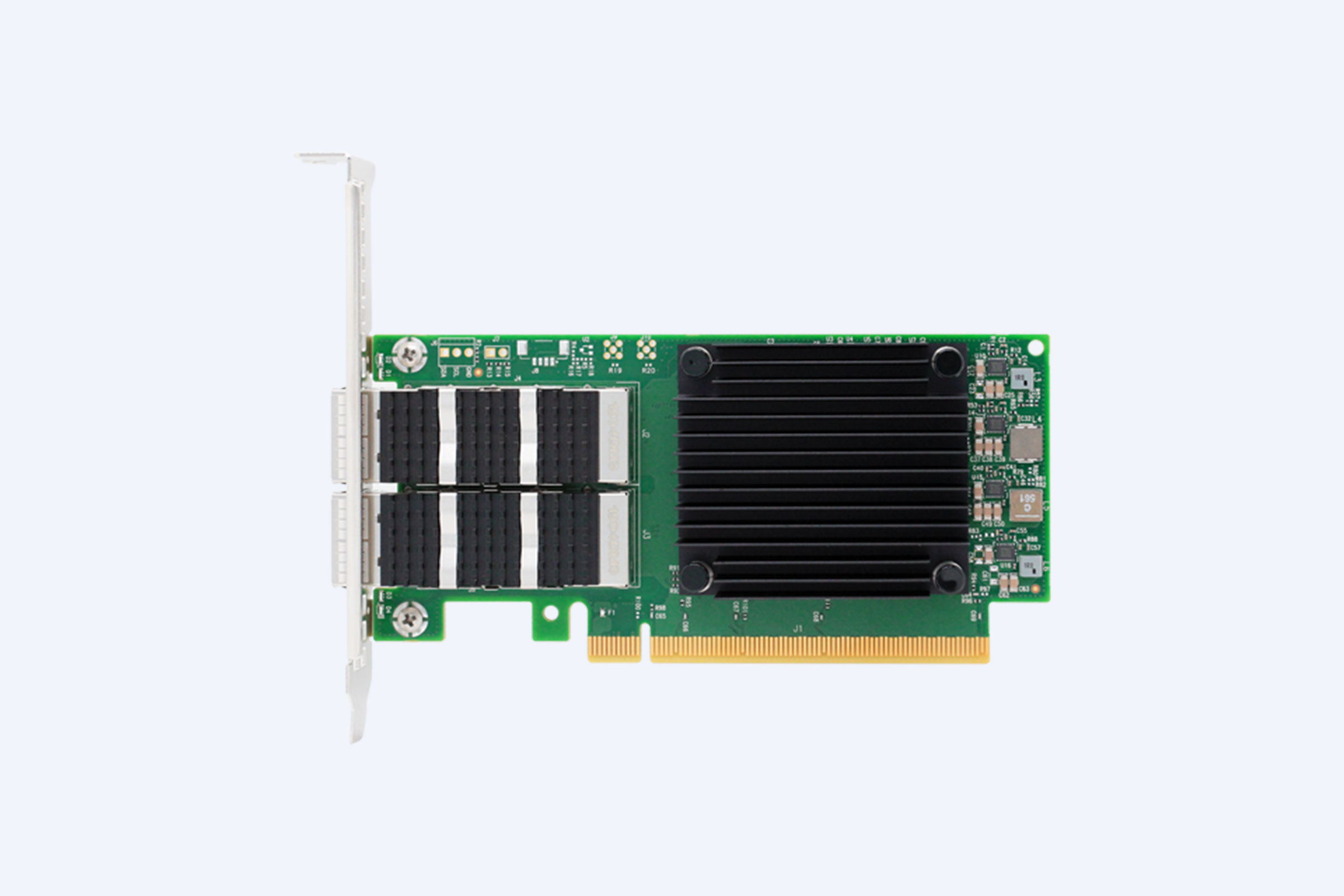
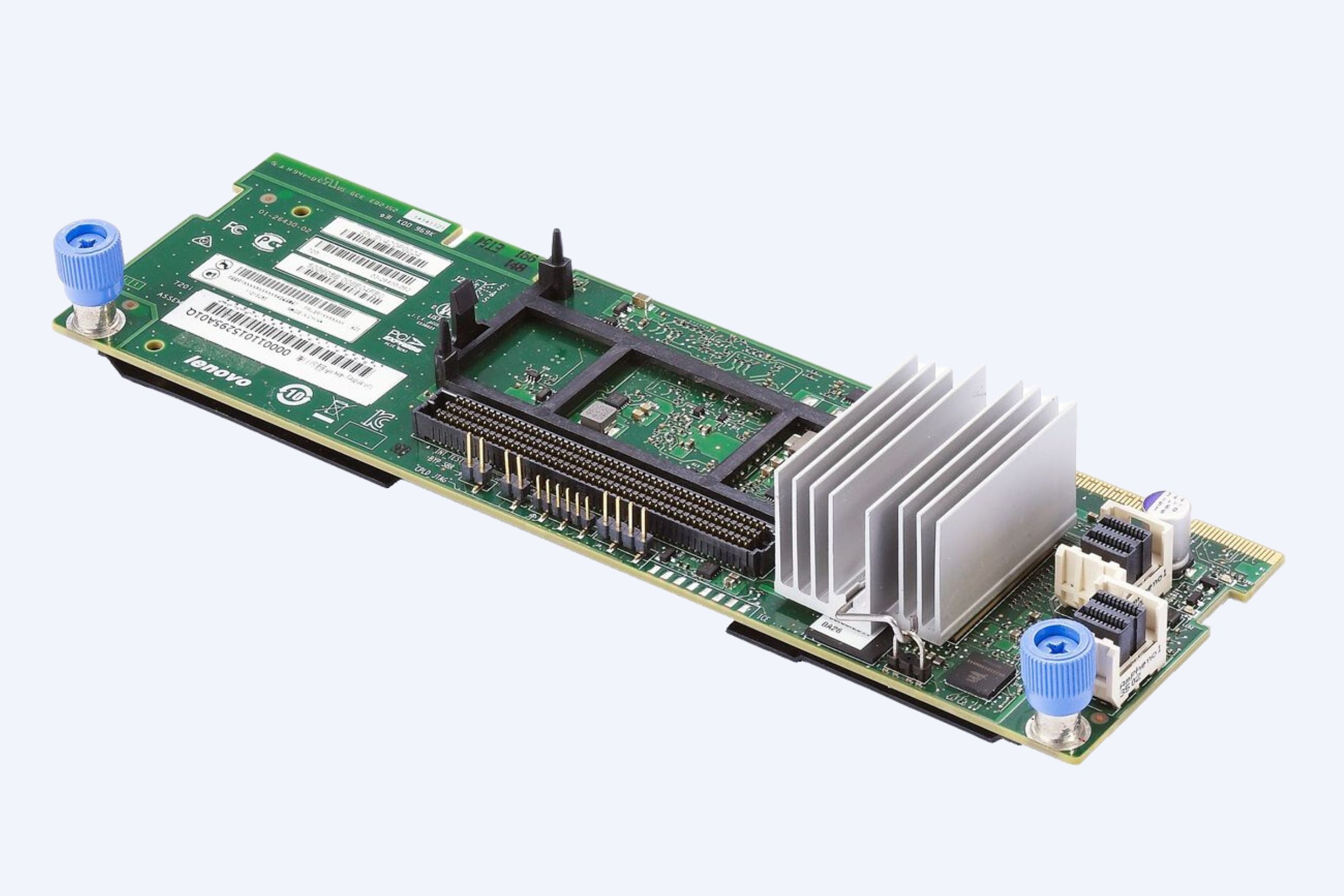
Hardware Reliability and the Backup Stack
Backups aren’t just software; they depend on reliable hardware that can store large datasets without error and withstand power surges, disk failures, or component aging.
High-reliability backup hardware includes enterprise-grade servers, purpose-built storage appliances, and robust network interfaces that sustain data integrity during transfer and at rest. The durability of hardware directly influences RTOs and RPOs during a disaster.
Pain Points and How to Address Them
Common misperception: backup is software-only. Reality: without dependable hardware, backup windows extend, restore times blow past SLAs, and data integrity becomes suspect during restore.
If you rely solely on on-site backups, you risk a single point of failure from floods, fires, or cyberattacks. A minimal offsite copy, protected by immutable storage, is essential to recover from catastrophic events.
Many organizations underestimate the value of test-driven recovery. Regular drills reveal gaps in backup coverage, retention policies, and restoration procedures, enabling continuous improvement.
Conversion Path: From Knowledge to Action
Assessment: start with a data risk audit to classify data by criticality and determine appropriate 3-2-1 coverage with immutable storage integration.
Architecture design: choose a hybrid strategy that blends on-prem hardware with offsite or cloud repositories and ensures one immutable copy is geographically separated.
Implementation: deploy scalable backup targets, enable automated failover tests, and configure secure access controls to protect the backups.
Engagement: book a tailored disaster recovery consultation to translate these practices into a concrete, vendor-agnostic plan that aligns with budget and compliance needs.
WECENT: Your Partner in Disaster Recovery Solutions
WECENT provides enterprise-grade hardware and tailored IT infrastructure solutions designed to support resilient backup and recovery programs. With deep partnerships across leading brands and a focus on high-availability, secure hardware, WECENT helps organizations implement durable offsite backups, immutable storage integrations, and scalable recovery architectures. Their team guides clients from initial assessment through installation, maintenance, and ongoing support, ensuring your disaster recovery strategy remains current in a dynamic threat environment.
Three-Level Conversion Funnel: From Awareness to Action
Awareness: understand why the 3-2-1 rule and immutable storage matter for ransomware defense and business continuity.
Consideration: compare on-prem, offsite, and hybrid models, emphasizing hardware reliability and immutable capabilities.
Action: schedule a custom disaster recovery consultation with WECENT to design a solution aligned to your industry, regulatory requirements, and budget.
Real-World ROI and Case Scenarios
Faster restores: with a well-designed 3-2-1 system and immutable storage, recovery time objectives drop dramatically, limiting downtime and revenue loss during incidents.
Reduced data loss: offsite and immutable copies ensure critical data can be recovered with minimal loss, preserving operational integrity and customer trust.
Clear auditability: immutable storage provides tamper-evident security and retention compliance, simplifying regulatory reporting and governance.
Future Trends in Backup and Recovery
Cloud-native backups and air-gapped architectures will coexist with on-prem hardware, giving organizations flexible options to optimize cost and performance.
Ransomware-ready architectures will emphasize rapid detection, automated isolation, and consistent testing to shorten exposure windows.
Hardware acceleration and software-defined storage will enable faster backups, larger datasets, and more granular restore points.
User Scenarios: What You Can Achieve
A financial services firm adopts a 3-2-1 with immutable storage to meet stringent regulatory retention while enabling rapid incident recovery.
A healthcare provider ensures patient data integrity and continuity of care through offsite hardened backups and tested disaster recovery playbooks.
A university IT department establishes a scalable archive that remains tamper-proof and quickly restorable during emergencies.
Three-Level FAQs
What is the 3-2-1 backup rule and why it matters for ransomware protection?
Three copies of data on two media with one offsite copy dramatically reduces single points of failure and accelerates recovery after an incident.
How does immutable storage deter ransomware attackers from tampering with backups?
Immutable storage prevents changes to backup data for a defined period, preserving clean recovery points even under attack.
Why is hardware reliability essential in backup and recovery?
Reliable hardware ensures backups can be created, stored, and restored quickly, minimizing downtime and data loss during incidents.
Buying Guide: How to Choose Your Disaster Recovery Partner
Look for end-to-end capabilities from assessment to ongoing support, including hardware reliability, immutable storage options, and proven recovery workflows.
Prioritize vendors that offer comprehensive testing, clear RTO/RPO targets, and transparent governance around data retention and access control.
Consider a tailored engagement with a partner like WECENT to ensure your architecture aligns with your industry, compliance needs, and budget.
Future Trend Forecast
The next wave of backup and recovery will blend hardware-backed immutability with intelligent automation for automated recovery testing, anomaly detection, and simplified compliance reporting.
Edge and hybrid cloud deployments will expand protection coverage for distributed organizations, improving resilience against localized disruptions and broadening recovery footprints.
Closing Note and CTA
Protecting your business from ransomware starts with a deliberate, hardware-aware backup strategy that embraces the 3-2-1 principle and immutable storage. To translate this into a concrete, risk-adjusted plan, book a disaster recovery consultation with WECENT and start building a resilient, auditable, and fast-recovering IT environment.