Silicon Root of Trust secures enterprise IT from the first line of code by embedding a hardware‑anchored security subsystem directly into the server silicon. Combined with TPM 2.0 and firm‑enforced secure boot, it verifies firmware signatures, binds encryption keys to trusted platform states, and blocks unsigned or tampered boot‑time code—making it much harder for attackers to stage persistent firmware‑level breaches on enterprise‑grade servers and data‑center hardware.
check:How to Choose Your First Enterprise Rack Server: 2026 Buyer’s Guide
What Is a Silicon Root of Trust?
A Silicon Root of Trust is a small, immutable cryptographic subsystem embedded directly into a server’s silicon, usually inside the CPU or management controller. It serves as the first trust anchor for all security operations, ensuring that only authorized code is allowed to run and that secrets such as encryption keys are stored in isolated, tamper‑resistant hardware rather than in software or general‑purpose memory.
This hardware‑level root of trust provides a verifiable starting point for the entire boot chain and underpins secure boot, measured boot, and remote attestation. Because it lives in the silicon, it is much harder to reconfigure or replace than user‑space software or even firmware‑based keys, which makes it a critical defense against supply‑chain compromises and pre‑OS firmware attacks on enterprise servers and storage platforms.
How Does Silicon Root of Trust Protect Server Hardware?
Silicon Root of Trust protects server hardware by enforcing a cryptographic chain of trust from the very first instruction executed on the CPU. When a server powers on, the Root of Trust verifies the signature of the next firmware stage, such as the UEFI BIOS or management‑controller firmware; if that stage is not cryptographically valid, the boot process halts or rolls back rather than executing compromised code.
This approach prevents attackers from injecting malicious payloads into BIOS, UEFI, or out‑of‑band management controllers that might otherwise survive OS reinstallations and disk wipes. For data‑center and cloud operators, embedding the root of trust in silicon also improves supply‑chain security by ensuring that only firmware signed by the original manufacturer can be accepted, reducing the risk of counterfeit or tampered server hardware.
What Role Does TPM 2.0 Play in Enterprise Security?
Trusted Platform Module 2.0 (TPM 2.0) is a standardized hardware security chip that provides cryptographic storage, key management, and platform‑state measurement capabilities for enterprise servers. It securely stores encryption keys, passwords, and certificates so they cannot be read or exported by the operating system or malware, and it can perform cryptographic operations such as encryption, signing, and attestation directly inside the chip.
In enterprise deployments, TPM 2.0 is commonly used to bind full‑disk encryption keys so they are only released when the platform boots in a known‑good state, record hashes of boot‑time components into Platform Configuration Registers, and enable remote attestation, where a server proves its integrity to a cloud controller or security policy engine before joining a cluster. Collectively, these capabilities make TPM 2.0 a key enabler of zero‑trust architectures and hardware‑assisted security for modern data‑center and virtualization environments.
How Can Secure Boot Prevent Firmware Attacks?
Secure Boot prevents firmware attacks by enforcing that only firmware and operating system components with valid cryptographic signatures are allowed to execute during the boot process. Working in tandem with the UEFI BIOS or platform firmware, Secure Boot checks each stage of the boot chain—BOOT ROM, firmware, bootloader, and OS loader—against a trusted key database and blocks any unsigned or tampered component.
This mechanism helps stop bootkits and UEFI rootkits that aim to take control before the OS loads, unauthorized firmware images or BIOS clones that might introduce backdoors, and delivery‑chain attacks that substitute firmware images with malicious variants. In an enterprise environment, Secure Boot should be paired with firmware‑signing policies, rollback protection, and centralized configuration management so that servers always boot from known‑good, signed images and cannot be silently downgraded to a vulnerable firmware version.
How Does Hardware Encryption Work with Silicon Root of Trust?
Hardware encryption works with the Silicon Root of Trust by binding encryption keys to the platform’s measured state so they are only released when the system is verified to be in a trusted configuration. For example, full‑disk encryption keys can be sealed inside the TPM such that they are only unsealed after Secure Boot and measured boot confirm that the firmware, bootloader, and early OS components have not been tampered with.
This approach reduces the risk that an attacker can steal a drive or snapshot and unlock it offline, because the hardware token will refuse to release the key if the measured PCRs do not match the expected baseline. In large‑scale deployments, hardware‑based encryption also integrates with enterprise‑grade key management systems and cloud‑native security stacks, allowing policy‑based controls over data access, recovery, and key rotation.
Why Is Firmware Attack Prevention Critical for Data Centers?
Firmware attack prevention is critical for data centers because firmware‑level threats can persist across OS reinstalls, disk wipes, and even bare‑metal re‑images, making them extremely difficult to detect and remove with traditional endpoint security tools. Attackers targeting firmware can install rootkits inside the BIOS, UEFI, or management controller to maintain persistent access, log credentials, or manipulate network traffic without triggering typical AV or EDR alerts.
In shared multi‑tenant environments and cloud infrastructures, compromised firmware can also undermine trust in the entire platform, enabling lateral movement, privilege escalation, and supply‑chain attacks that affect many tenants at once. By enforcing silicon‑based roots of trust, firmware‑signing, and hardware‑assisted encryption, data centers can significantly reduce the attack surface below the operating system and strengthen their defense‑in‑depth posture.
How Do You Implement TPM‑Based Security at Scale?
Implementing TPM‑based security at scale requires a combination of standardized policies, automation, and centralized monitoring rather than one‑off configuration on individual servers. At the foundational level, organizations should enable Secure Boot and measured boot across all server models and enforce consistent signing policies, configure TPM 2.0 to capture PCR measurements of firmware, bootloader, and early OS components, and integrate TPM attestation data into SIEM or security orchestration platforms so anomalous boot states can trigger alerts.
Automation tools and configuration management frameworks can then push compliant firmware and BIOS settings, rotate keys, and enforce TPM‑related policies across racks, racks, and regions. In cloud and hybrid environments, this scaled TPM‑based trust is often used to make access decisions, such as node admission into clusters or segmented networks, based on hardware‑verified integrity rather than just IP or identity.
WECENT Expert Views
WECENT’s hardware‑security specialists emphasize that “true server‑level security starts where the silicon does, not in the operating system.” They observe that many enterprises still focus almost exclusively on network and endpoint protections while leaving the firmware and boot‑path layers vulnerable. By selecting server platforms with built‑in Silicon Root of Trust and TPM 2.0, then enforcing signed Secure Boot and hardware‑based encryption, WECENT helps its clients turn generic hardware into hardened, auditable infrastructure that supports modern zero‑trust and compliance requirements.
For organizations deploying Dell PowerEdge, HPE ProLiant, Huawei, Lenovo, and other enterprise‑grade servers through WECENT, this means access to pre‑configured, original‑hardware solutions with documented security features, firmware‑signing policies, and ongoing support. WECENT’s team can help tailor deployment blueprints, define key‑management workflows, and integrate TPM‑based attestation into existing security stacks—ensuring that every server in the data center, from rack to edge, contributes to an end‑to‑end hardware‑anchored security model.
How Do Different Server Brands Handle Silicon Root of Trust?
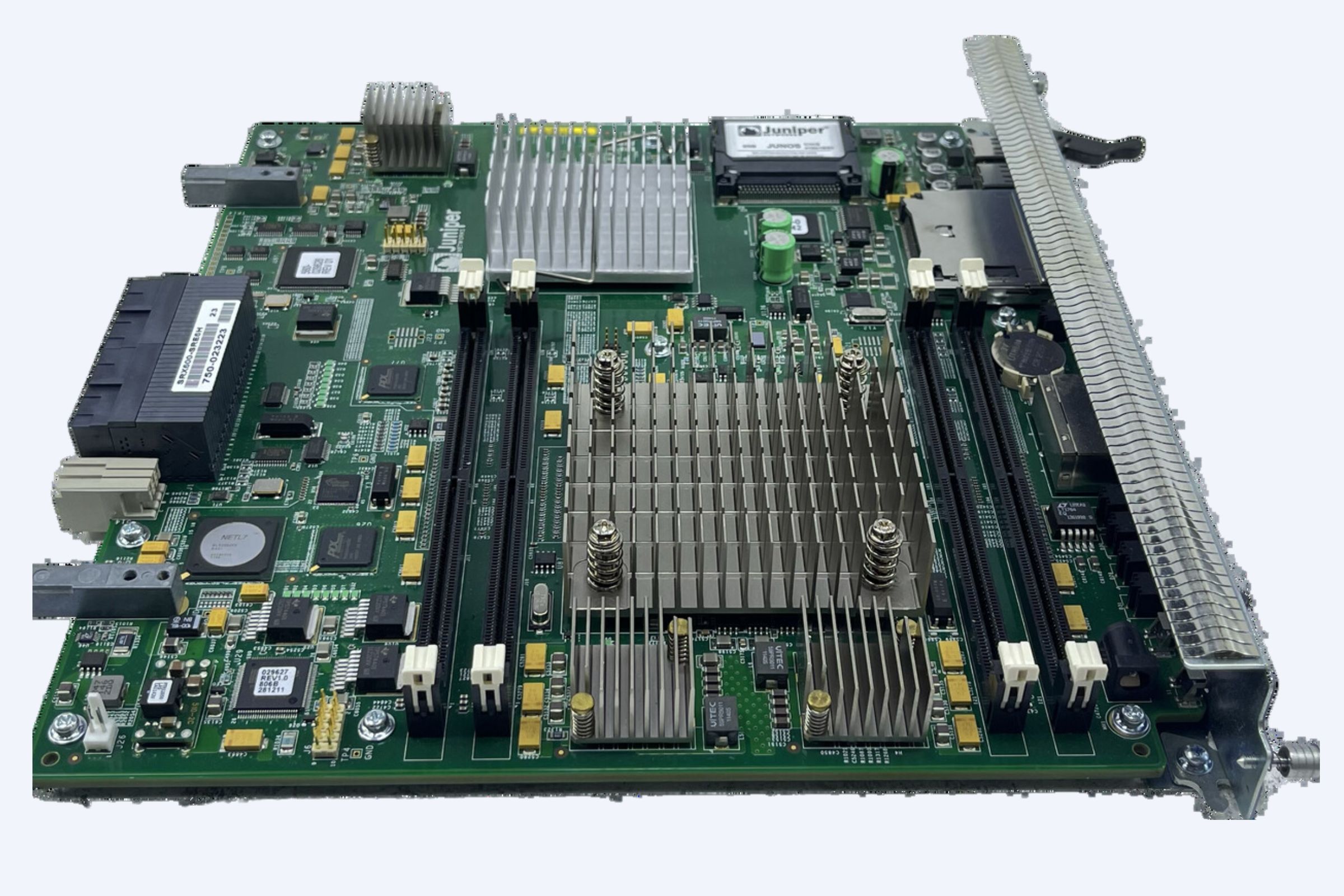
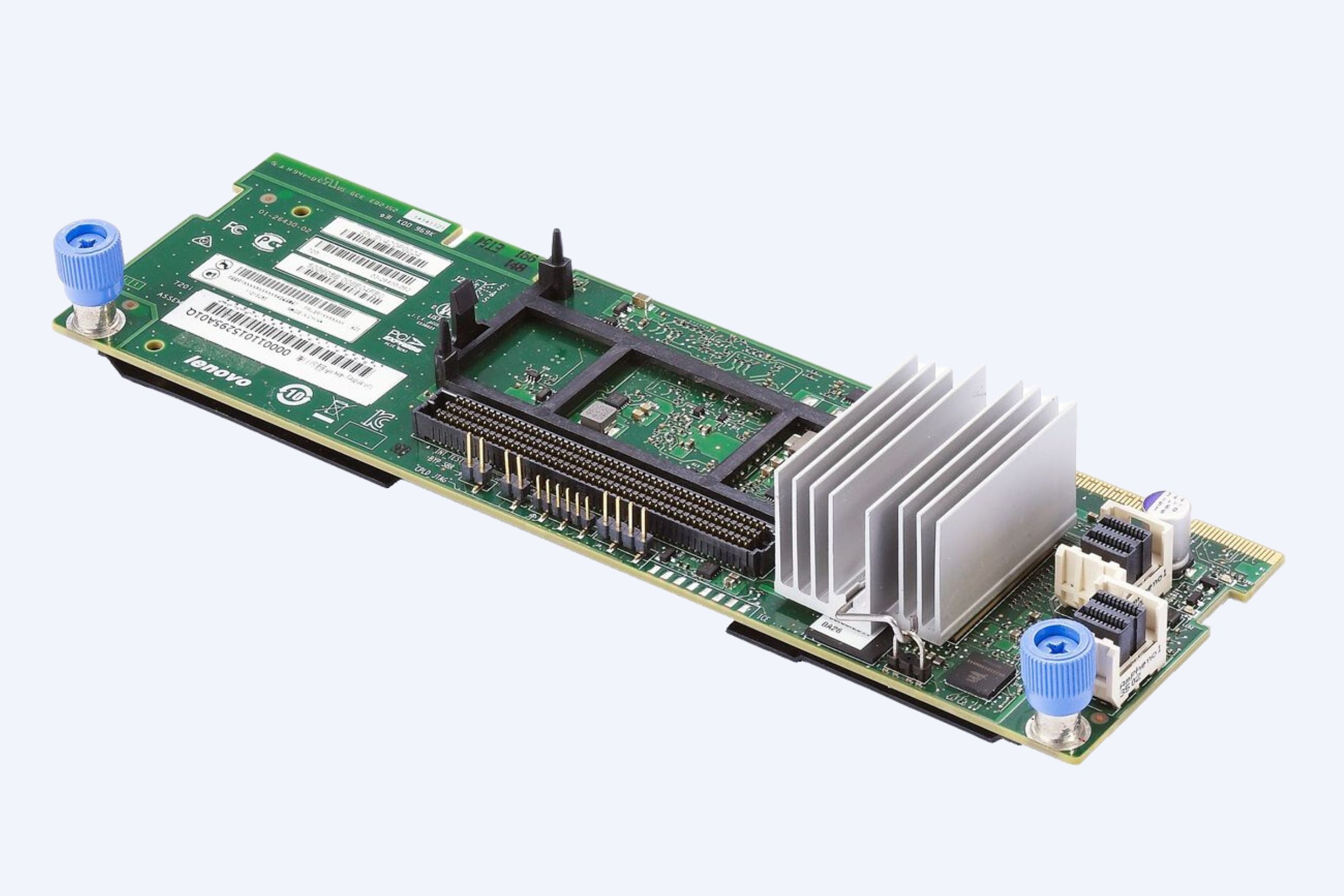
Different enterprise server brands implement Silicon Root of Trust and related features in ways that align with their ecosystem and management stacks, but the core principles remain the same: hardware‑anchored trust, verified boot, and protected key storage. Dell PowerEdge servers integrate silicon‑level security via iDRAC and Secure Boot‑enabled UEFI, with TPM 2.0 used for key sealing and attestation. HPE ProLiant servers leverage HPE Silicon Root of Trust inside the iLO management controller, which creates an immutable fingerprint of firmware and detects changes caused by malicious code. Huawei and Lenovo servers use vendor‑specific management controllers and UEFI firmware with TPM‑based attestation and secure boot, often aligned with industry‑standard specifications such as TCG TPM 2.0.
Although the branding and tooling differ, any enterprise‑class server purchased through WECENT can be configured to enforce a hardware‑anchored chain of trust, measured boot, and hardware‑based encryption, giving organizations a consistent security posture across multiple vendors. WECENT’s broad portfolio of enterprise‑grade servers and hardware ensures that customers can align their security strategy with the specific capabilities of each platform.
Key Hardware‑Security Features in Enterprise Servers
Modern enterprise servers typically offer a set of hardware‑security features that work together under the umbrella of a Silicon Root of Trust. These include Secure Boot and measured boot enforced by UEFI firmware, TPM 2.0 for cryptographic operations, key storage, and platform‑state measurement, secure firmware update mechanisms with rollback protection and signature checks, and in some CPU models, hardware‑based memory encryption and secure enclaves.
These capabilities are increasingly important not only for on‑prem data centers but also for edge computing, cloud‑adjacent infrastructure, and AI‑/GPU‑focused workloads where large‑scale servers or GPU‑accelerated racks need to be provisioned and attested quickly and securely. WECENT’s extensive portfolio of Dell, HPE, Huawei, Lenovo, and other enterprise servers gives customers the flexibility to choose platforms that match their security policy, compliance, and performance requirements.
Practical Steps to Harden Servers with Silicon Root of Trust
To harden servers with Silicon Root of Trust and TPM‑based security, organizations should select enterprise‑grade server hardware that includes TPM 2.0 and silicon‑anchored security features, standardize on Secure Boot and measured boot across all server models and firmware versions, configure TPM policies to capture and monitor PCR values for boot‑time components, integrate hardware‑based encryption for data‑at‑rest with keys bound to TPM‑measured states, and monitor firmware‑update logs while enforcing signed, time‑stamped firmware rolls.
Partnering with an experienced IT equipment supplier and authorized agent such as WECENT can streamline this process, from hardware selection and configuration to deployment and ongoing support. WECENT’s deep experience with enterprise‑grade servers and storage ensures that customers can deploy hardened, TPM‑enabled infrastructure that meets regulatory, audit, and operational requirements.
Tables: Hardware‑Security Capabilities Across Server Types
The following table illustrates how core hardware‑security capabilities map to common enterprise server products available through WECENT.
A second table summarizes how key security mechanisms map to defense objectives:
Frequently Asked Questions
What is the main advantage of Silicon Root of Trust over software‑based security?
Silicon Root of Trust protects the earliest stages of the boot process in hardware, making it much harder for attackers to tamper with firmware or inject malicious code before the OS loads. Software‑based security cannot inspect the very first instructions that run on the CPU, leaving a critical blind spot that hardware‑anchored roots of trust help close.
How do TPM 2.0 and Secure Boot work together?
TPM 2.0 records hashes of boot components into protected registers, while Secure Boot verifies that each stage of the boot chain is signed by a trusted authority. Together, they create a hardware‑based chain of trust: Secure Boot prevents unauthorized code from running, and the TPM can prove that the system booted in a known‑good state.
Can I use Silicon Root of Trust on older server hardware?
Most silicon‑level roots of trust are built into modern CPUs and server management controllers, so older hardware may lack native support or require firmware and firmware‑module upgrades. For organizations upgrading legacy racks, WECENT can assess existing infrastructure and recommend compatible, TPM‑enabled server platforms that meet current security standards.
Does hardware encryption slow down server performance?
Modern hardware‑based encryption controls, such as AES‑NI‑accelerated encryption and TPM‑backed key storage, add minimal overhead compared to pure‑software encryption. In many cases, the performance impact is barely noticeable, while the security benefits—from protection against stolen drives to compliance with data‑protection regulations—are substantial.
How can WECENT help my organization implement these security features?
WECENT provides end‑to‑end support for selecting, configuring, and integrating enterprise servers with Silicon Root of Trust, TPM 2.0, and Secure Boot. As an authorized agent and IT equipment supplier for Dell, HPE, Huawei, Lenovo, and others, WECENT can deliver hardened, original‑hardware servers, pre‑aligned configurations, and ongoing technical guidance tailored to your security and compliance requirements.