-
Advanced data security hardware stands as the unbreakable foundation for businesses facing escalating cyber threats in 2026. From quantum-resistant encryption modules to AI-accelerated trusted platform modules, these cutting-edge solutions deliver ironclad protection for sensitive data across enterprises worldwide.
Market Trends Shaping Data Security Hardware 2026
The global advanced data security hardware market surges past $15 billion in 2026, driven by rising ransomware attacks and regulatory demands like GDPR updates and CCPA enhancements. Businesses increasingly adopt hardware security modules for post-quantum cryptography, with adoption rates climbing 40% year-over-year according to Gartner forecasts. Key drivers include AI-powered threats and supply chain vulnerabilities, pushing firms toward tamper-proof hardware root of trust solutions that outperform software-only defenses.
Cloud-based surveillance integrates seamlessly with hardware enclaves, enabling real-time anomaly detection while ensuring data sovereignty. Zero trust architecture now mandates hardware-backed identity verification, reducing breach risks by up to 70% in hybrid environments. Enterprises in finance and healthcare lead this shift, prioritizing secure enclaves like Intel SGX and AMD SEV for confidential computing workloads.
Core Technologies in Advanced Data Security Hardware
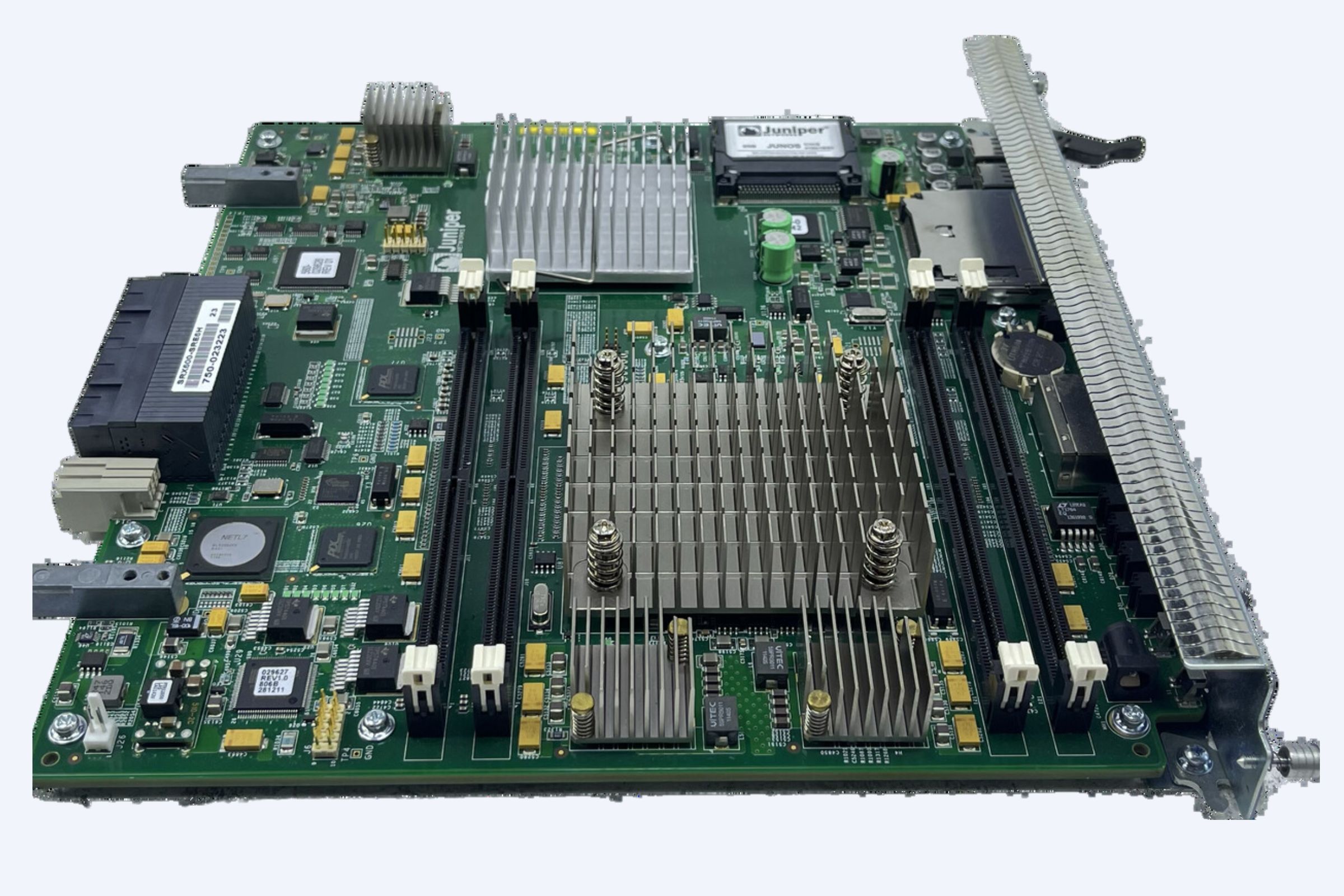
Hardware security modules, or HSMs, form the core of advanced data security hardware, providing FIPS 140-3 certified key management and cryptographic acceleration. Trusted execution environments shield sensitive computations from host OS vulnerabilities, vital for AI model training and blockchain validations in 2026. Post-quantum encryption chips counter emerging quantum computing risks, safeguarding long-term data assets against harvest-now-decrypt-later attacks.
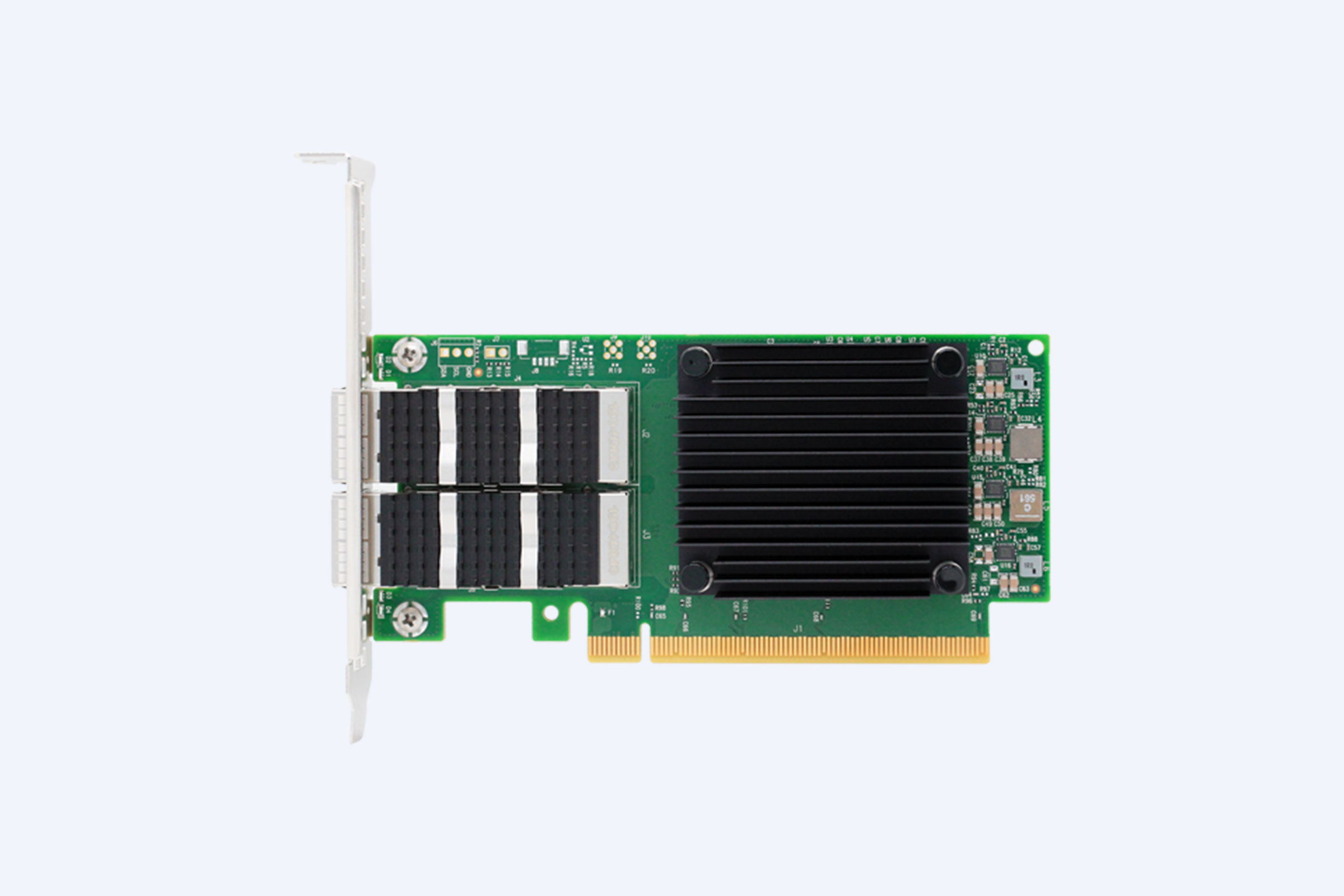
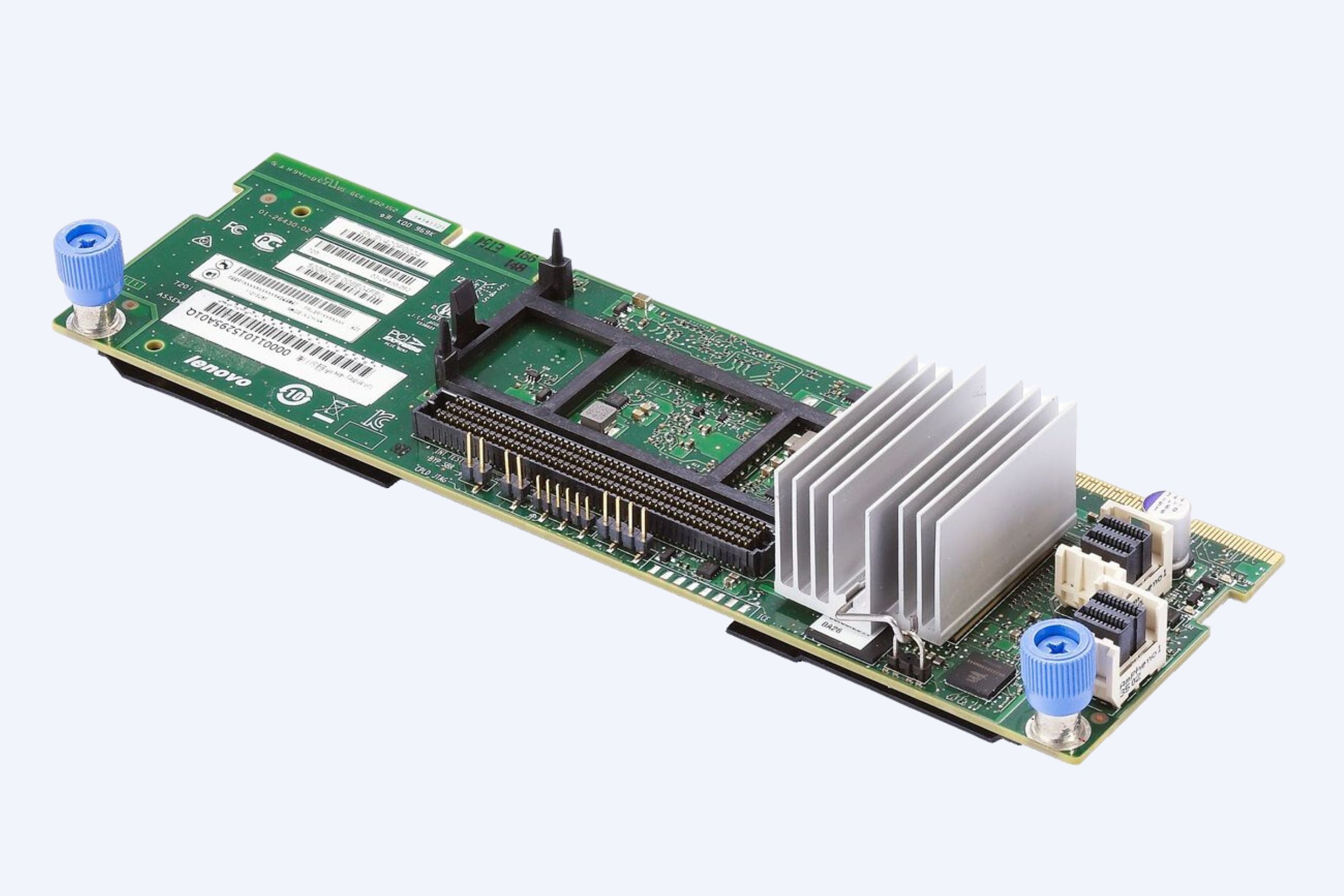
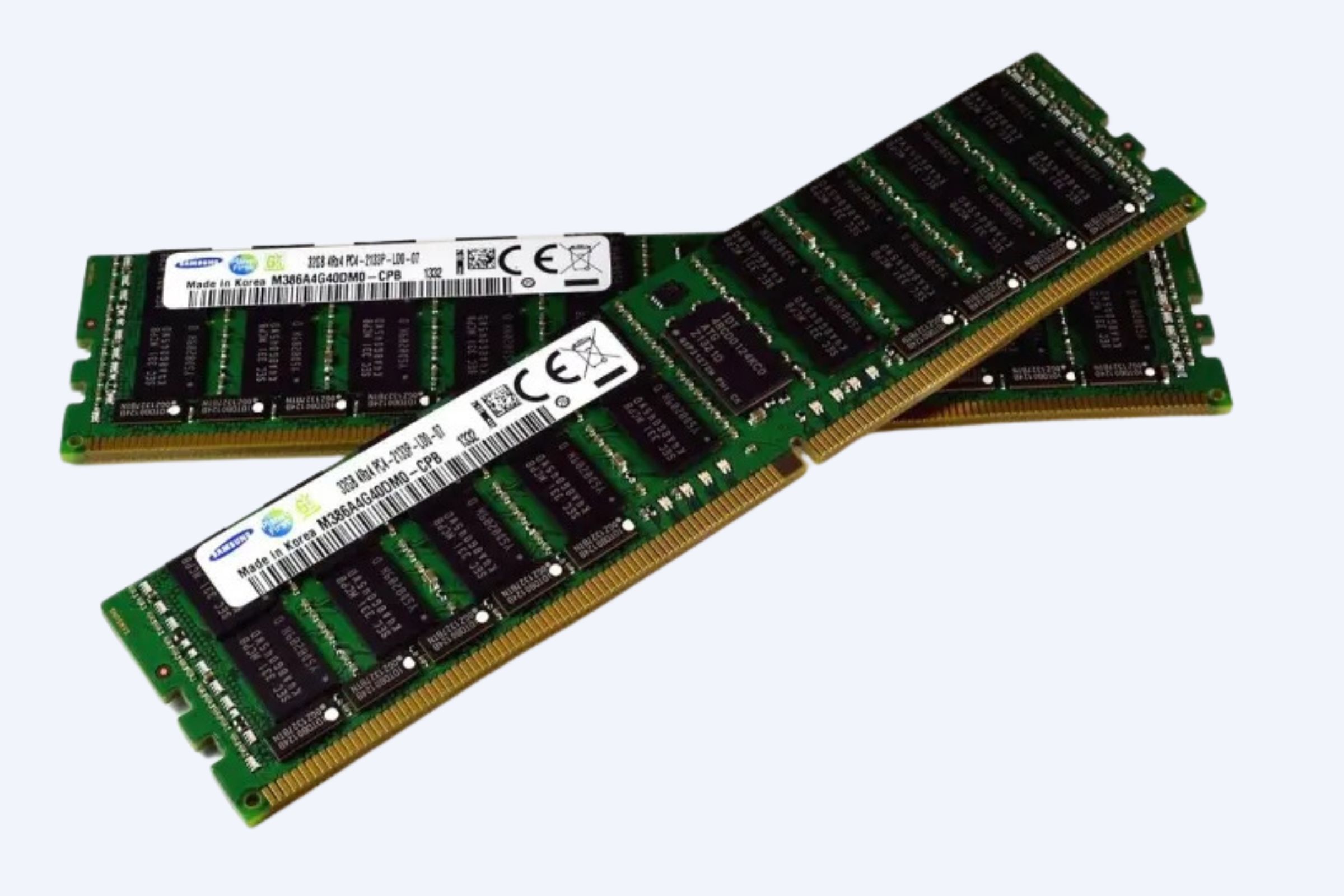
Self-encrypting drives with built-in AES-256 hardware engines automate data-at-rest protection, minimizing latency in high-volume storage arrays. Network interface cards featuring inline encryption offload CPU burdens, enhancing throughput for 400Gbps data centers. These technologies converge in secure multi-party computation hardware, enabling privacy-preserving analytics across distributed business networks.
Top Advanced Data Security Hardware Products 2026
Leading products dominate the advanced data security hardware landscape, each tailored for enterprise-scale deployment.
Product Name Key Advantages Ratings Use Cases Thales Luna Network HSM Quantum-resistant algorithms, cloud scalability, 99.99% uptime 4.9/5 Key management for banking transactions, PKI for IoT fleets Utimaco SecurityServer Tamper-evident design, FIPS 140-3 Level 4, API flexibility 4.8/5 Certificate authority operations, database encryption in healthcare Fortanix HSM as a Service Runtime reconfigurable crypto, zero-trust integration, pay-per-use 4.7/5 AI workload protection, SaaS provider compliance IBM Crypto Express Mainframe-optimized, high TPS crypto ops, z/OS native 4.9/5 Financial clearing houses, government data vaults Nitrokey HSM 2 Open-source firmware, portable USB form, ECC support 4.6/5 SMB VPN gateways, developer code signing These solutions excel in performance benchmarks, with Thales Luna handling millions of transactions per second while maintaining sub-millisecond latencies.
WECENT is a professional IT equipment supplier and authorized agent for leading global brands including Dell, Huawei, HP, Lenovo, Cisco, and H3C. With over 8 years of experience in enterprise server solutions, we specialize in providing high-quality, original servers, storage, switches, GPUs, SSDs, HDDs, CPUs, and other IT hardware to clients worldwide, ensuring efficient, secure IT infrastructure for finance, education, healthcare, and data centers.
Competitor Comparison: Best Data Security Hardware 2026
Advanced data security hardware providers differentiate through scalability, compliance, and threat model coverage.
Feature Thales Luna Utimaco SecurityServer Fortanix IBM Crypto Express Nitrokey HSM 2 Quantum Resistance Yes Yes Partial Yes Yes Max TPS 20,000 15,000 10,000 50,000 5,000 FIPS Level 140-3 L4 140-3 L4 140-3 L3 140-3 L4 140-2 L3 Cloud Native Full Partial Full Hybrid No Price Range (Annual) $50K+ $40K+ $20K+ $100K+ $1K+ Deployment Time 1 week 2 weeks 1 day 4 weeks Hours Thales leads in enterprise throughput, while Nitrokey offers unmatched affordability for small businesses needing robust advanced data security hardware safeguards.
Real User Cases: ROI from Data Security Hardware
A major European bank deployed Thales Luna HSMs across 500 branches, slashing key rotation times by 80% and preventing $12 million in potential fraud losses within the first year. Healthcare provider Mayo Clinic integrated IBM Crypto Express, achieving HIPAA compliance with 99.999% data availability during peak patient surges. SMB retailer using Fortanix reported 300% faster PCI-DSS audits, freeing IT teams for growth initiatives.
These implementations yield average ROI of 450% over three years, per IDC studies, through reduced downtime and insurance premium cuts. Finance firms see particular gains, with hardware root of trust blocking 95% of insider threats that software misses.
How to Choose Advanced Data Security Hardware for Business
Selecting the right advanced data security hardware starts with threat modeling—identify quantum risks, compliance needs, and workload scale. Prioritize vendors with proven interoperability, like those supporting KMIP 2.0 for seamless key lifecycle management. Test for total cost of ownership, factoring maintenance, scalability, and integration with existing SIEM tools.
Budget $10,000-$500,000 annually based on enterprise size, ensuring hardware supports emerging standards like MLS for machine learning security. Partner with suppliers offering end-to-end support for deployment and customization to maximize business safeguards.
Future Trends in Data Security Hardware 2026 and Beyond
By late 2026, homomorphic encryption hardware accelerators will enable computations on encrypted data, revolutionizing privacy in collaborative AI. Neuromorphic chips promise ultra-low power anomaly detection, ideal for edge deployments in IoT-heavy industries. Blockchain-anchored hardware wallets evolve into decentralized HSMs, supporting Web3 enterprise applications.
Expect 5nm process nodes for next-gen secure elements, boosting crypto performance 10x while shrinking footprints. Regulatory pushes for sovereign data control will spike demand for on-premises advanced data security hardware, blending with confidential computing for hybrid cloud dominance.
Frequently Asked Questions on Data Security Hardware
What makes advanced data security hardware essential for 2026 businesses? It provides tamper-proof root of trust immune to software exploits, critical amid AI-augmented attacks.
How does HSM differ from TPM in enterprise use? HSMs scale for network-wide key ops, while TPMs focus on single-device boot integrity.
Is post-quantum hardware ready for production now? Yes, NIST-approved algorithms deploy in Thales and Utimaco units, future-proofing against quantum threats.
Ready to fortify your business with top-tier advanced data security hardware? Contact experts today to deploy quantum-safe solutions tailored for your operations and drive unbreakable resilience in 2026.
How Advanced Data Security Hardware Safeguards Businesses in 2026
Published by admin5 on 5 2 月, 2026
Contents
- Market Trends Shaping Data Security Hardware 2026
- Core Technologies in Advanced Data Security Hardware
- Top Advanced Data Security Hardware Products 2026
- Competitor Comparison: Best Data Security Hardware 2026
- Real User Cases: ROI from Data Security Hardware
- How to Choose Advanced Data Security Hardware for Business
- Future Trends in Data Security Hardware 2026 and Beyond
- Frequently Asked Questions on Data Security Hardware
Related Posts
Contact Us Now
Please complete this form and our sales team will contact you within 24 hours.