Cyber Storage Resilience in 2026 means security is built directly into storage hardware, not just wrapped around it with firewalls. New primary‑storage‑centric systems now perform real‑time cyber detection at the primary layer, spotting ransomware‑like patterns before files are even written, enforced through immutable snapshots and zero‑trust‑aware architectures. Hardware‑embedded anomaly monitoring and policy‑driven data protection make this layer an essential bedrock of modern cyber‑resilient infrastructures.
What Is Cyber Storage Resilience in 2026?
Cyber Storage Resilience in 2026 refers to storage‑centric security that protects data both at rest and in motion, not only by backup but by proactive detection and policy enforcement at the primary storage layer. It combines hardware‑based controls, immutable snapshots, and real‑time threat detection so that ransomware and other malicious behavior can be interrupted before large‑scale encryption or exfiltration occurs.
In practice, Cyber Storage Resilience:
-
Embeds security into the storage controller and drive firmware.
-
Uses behavioral analytics (mass file changes, unusual encryption bursts) to flag ransomware‑like activity.
-
Integrates with zero‑trust architectures so that data access is continuously verified and least‑privilege‑enforced even at the storage plane.
This approach shifts the focus from “blocked at the perimeter” to “protected at the data layer,” which is especially critical for enterprise IT, cloud‑style workloads, and data centers that rely on hybrid storage and virtualization.
How Does Primary‑Layer Cyber Detection Work?
Primary‑layer cyber detection runs inside the storage array or controller, analyzing metadata, file access patterns, and entropy changes as data is written or modified on the primary storage device. Instead of waiting for a backup job to scan, it inspects active writes in real time, looking for tell‑tale ransomware signatures such as simultaneous mass encryption, unusual file extensions, or sudden spike in small‑file writes.
Key technical mechanisms include:
-
File‑system‑level anomaly detection (for NAS and object storage).
-
Block‑level entropy analysis (for block‑based storage and databases).
-
Integration with security telemetry from servers, hypervisors, and backup platforms to correlate events.
When such behavior is detected, the storage subsystem can:
-
Lock down the affected volume or folder.
-
Trigger an immutable snapshot.
-
Notify SOC or backup tools for immediate response.
This primary‑layer detection is now a core feature of modern data‑protection platforms such as HPE StoreOnce‑based backup repositories and Dell PowerStore‑centric storage deployments, both of which are widely supported by professional IT equipment suppliers such as WECENT.
Why Is Proactive Detection at the Storage Layer Critical?
Proactive detection at the storage layer is critical because once ransomware reaches the primary data store, traditional firewalls and endpoint tools often cannot prevent bulk encryption or data destruction. By the time a backup job runs, the corrupted state may already be encapsulated, especially if snapshots are not immutable or air‑gapped.
In 2026, proactive detection at the storage layer:
-
Shrinks the window of exposure between infection and intervention.
-
Prevents “infected backups” by triggering clean, undeleted snapshots before corruption spreads.
-
Reduces recovery time objectives (RTO) because the last known‑good state is already locked and policy‑driven.
For organizations using HPE ProLiant‑based servers, Dell PowerEdge systems, or HPE StoreOnce‑centric backup targets, this layer of detection becomes a first line of defense, not a last‑resort backup. Professional IT solution providers such as WECENT now design architectures that couple these storage‑centric detection features with hardened servers, secure switches, and compliant storage arrays to meet sector‑specific compliance and audit requirements.
How Do HPE StoreOnce‑5660 and Dell Systems Enable Cyber Resilience?
HPE StoreOnce 5660 and Dell storage platforms enable cyber resilience by combining immutable repositories, secure‑protocol‑based ingestion, and real‑time ransomware‑oriented detection. The StoreOnce 5660 acts as a cyber‑resilient primary backup target, using Catalyst‑based protocols and Virtual Lock‑style immutability to make data tamper‑proof even from inside the production network, while Dell PowerStore‑family arrays add secure snapshots, air‑gapped vaults, and zero‑trust‑aligned access controls.
For Cyber Storage Resilience at the primary layer, these systems:
-
Offer immutable and append‑only snapshots so that ransomware cannot overwrite or delete previous states.
-
Integrate with backup and data‑management tools (such as Veeam or PowerProtect ecosystems) to enforce policy‑driven recovery points.
-
Support hardened, STIG‑compliant configurations and strict role‑based access control (RBAC) at the storage operating‑system level.
Enterprises that combine HPE StoreOnce‑based repositories with Dell‑brand primary storage (such as PowerStore or ECS‑based object storage) create a multi‑layer cyber‑resilient stack. WECENT, as an authorized agent for Dell, HPE, and other global brands, can help configure StoreOnce‑5660‑centric backup and Dell‑based storage fabrics that embed these immutability and detection features into a single, vendor‑aligned solution.
What Are Zero‑Trust Storage and Immutable Snapshots?
Zero‑Trust Storage extends the zero‑trust principle—“never trust, always verify”—from the network layer down into the storage plane. It assumes that every access request may be compromised until proven otherwise, enforcing continuous authentication, encryption, and least‑privilege access for every user, service, and application touching the data.
Immutable snapshots, in parallel, are point‑in‑time copies of data that cannot be modified or deleted until a pre‑defined retention period expires. Even if an attacker gains admin‑level privileges, they cannot erase these snapshots if the storage platform is configured with WORM‑style or policy‑driven immutability.
For Cyber Storage Resilience, zero‑trust storage and immutable snapshots work together:
-
All data access is authenticated and audited at the storage controller.
-
Write‑time detection flags suspicious behavior, and a new snapshot is created.
-
The immutable snapshot becomes the clean recovery point, decoupled from the potentially compromised primary volumes.
WECENT designs IT solutions that couple zero‑trust‑ready HPE ProLiant servers and Dell‑based storage arrays with immutability‑aware backup targets, ensuring that recovery‑point architecture aligns with zero‑trust and cyber‑resilience standards.
Immutability and Zero‑Trust Capabilities in Modern Storage
These features are critical for organizations that must meet strict regulatory requirements while also defending against modern ransomware campaigns.
Are Ransomware‑Specific Detection Features Built into Storage?
Yes, ransomware‑specific detection features are now embedded directly into storage software and controllers, not just layered on via third‑party tools. Modern storage platforms analyze file‑system metadata, access patterns, and entropy changes to detect mass‑encryption behavior, file‑type mutation, and suspicious write‑burst patterns that are typical of ransomware payloads.
Storage‑native ransomware detection:
-
Monitors for rapid changes to many files at once, unusual file extensions, and nonsensical file name mutations.
-
Uses machine‑learning‑based models or heuristics to distinguish backup‑style bulk writes from malicious bulk encryption.
-
Integrates with SIEM or SOC workflows to trigger alerts, quarantine, or snapshot creation when known‑pattern behavior is seen.
For example, Dell PowerStore and HPE‑integrated storage platforms expose these detection capabilities as part of their cyber‑resilience stack, often without requiring separate licenses. When businesses work with an IT equipment supplier such as WECENT, they can combine these native ransomware‑detection features with Dell‑brand servers, HPE‑brand storage controllers, and other branded hardware to build a unified, vendor‑aligned defense‑in‑depth architecture.
How Can Enterprises Build Cyber Resilience Using Storage‑Hardware Partnerships?
Enterprises can build cyber resilience by aligning their storage‑hardware strategy with vendors that offer end‑to‑end cyber‑resilient architectures, from servers to storage arrays to backup targets. This includes selecting platforms that support immutable snapshots, secure protocols, and primary‑layer detection, then integrating them through a single‑sourced or partner‑coordinated IT equipment supplier.
A resilient approach using storage‑hardware partnerships:
-
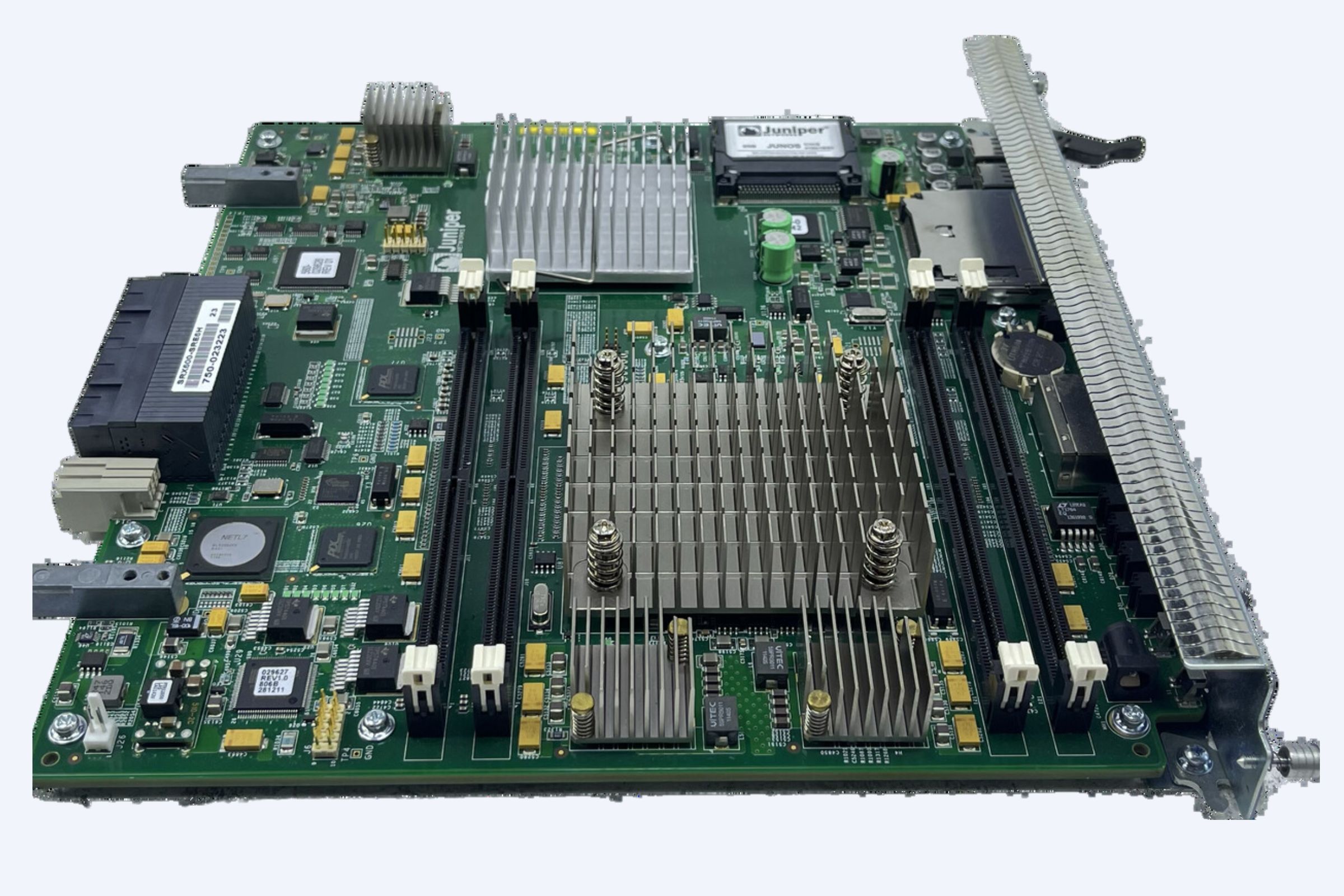
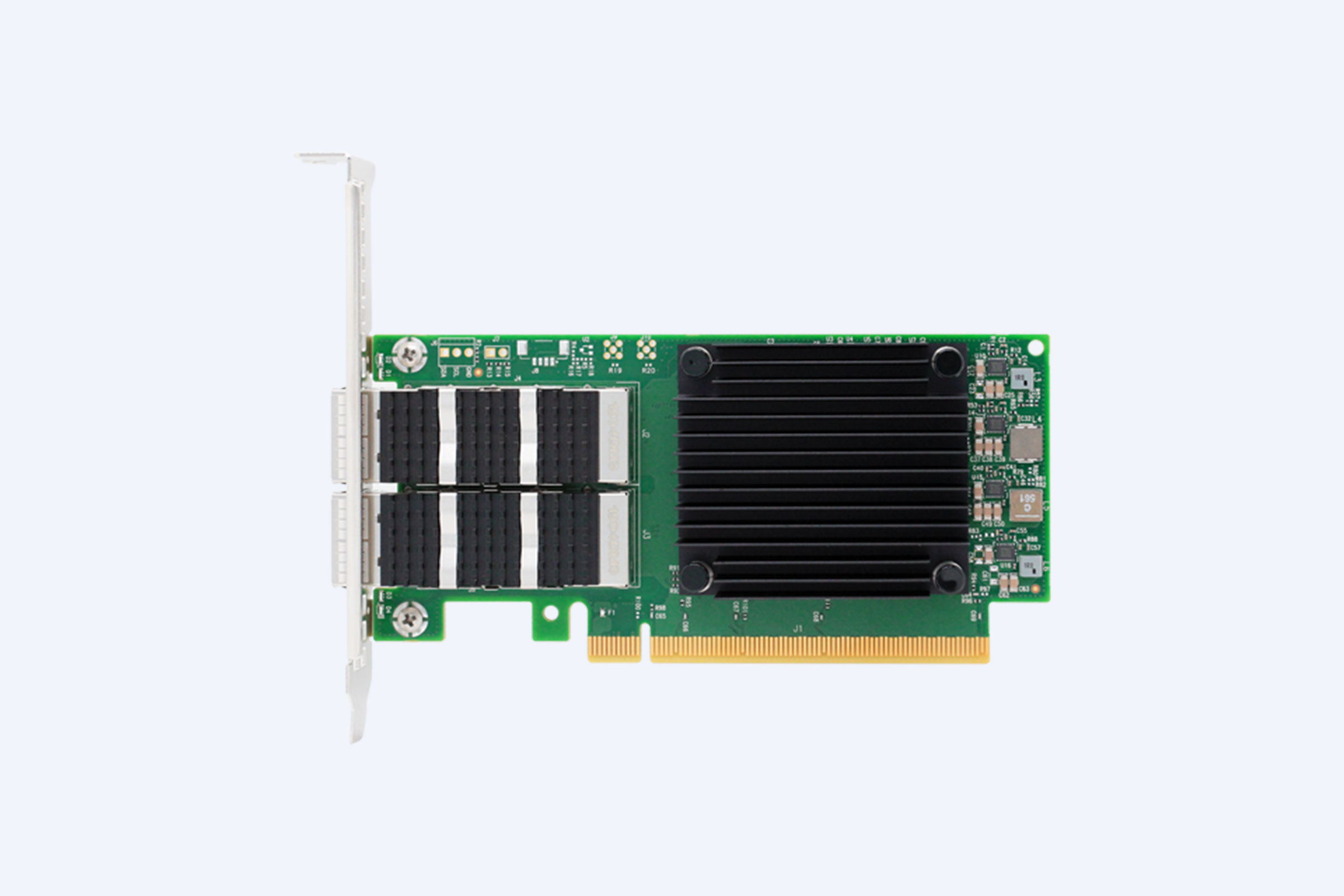
Standardizes on HPE ProLiant servers and StoreOnce‑based repositories or Dell PowerEdge servers with PowerStore‑based storage fabrics.
-
Deploys ai‑gated or logically isolated backup targets configured with WORM‑style immutability.
-
Leverages vendor‑endorsed security baselines and STIG‑style hardening for firmware, OS, and storage controllers.
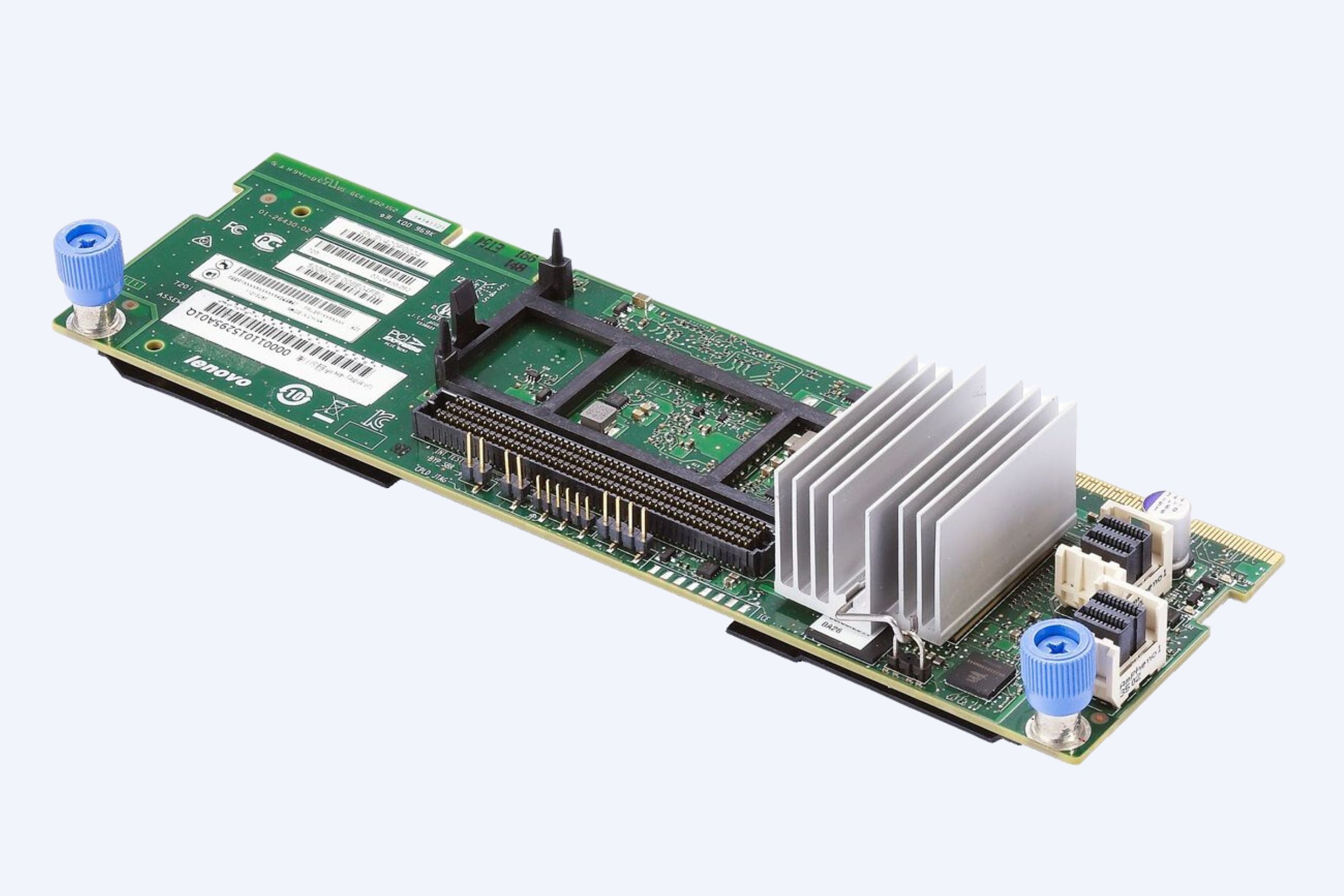
WECENT, as an authorized agent for Dell, HPE, HP, Lenovo, Cisco, and H3C, can help organizations procure and integrate these platforms as part of a holistic Cyber Storage Resilience strategy. This includes OEM‑grade hardware, original‑equipment warranties, and lifecycle support so that every storage‑centric defense feature is fully supported and validated.
Example Storage‑Hardware Partnership Stack for Cyber Resilience
By aligning these components through a trusted IT equipment supplier such as WECENT, enterprises shorten deployment cycles, reduce configuration risk, and ensure full vendor support across the stack.
How Does Zero‑Trust Architecture Integrate with Cyber Storage?
Zero‑Trust Architecture integrates with Cyber Storage by treating every access request to the storage layer as untrusted until explicitly verified. This means that storage‑based services—NAS shares, object buckets, and block‑based LUNs—must be protected by strong authentication, encryption‑in‑transit and‑at‑rest, and least‑privilege authorization.
Key integration points:
-
Storage controllers enforce identity‑enabled access (e.g., directory‑integrated ACLs, SAML‑style federation).
-
Data movement is encrypted end‑to‑end, including between primary storage and backup repositories.
-
Logging and telemetry from storage platforms feed into SIEM or SOC platforms for continuous risk‑scoring and anomaly detection.
In 2026, leading storage vendors such as HPE and Dell ship pre‑configured zero‑trust‑aware profiles that can be activated on platforms connected to HPE ProLiant or Dell PowerEdge servers. WECENT can help design and implement these zero‑trust‑aligned storage fabrics, ensuring that the entire data path—from application servers to backup vaults—is governed by verifiable, continuously checked policies.
Why Should Enterprises Choose an Authorized IT Equipment Supplier?
Enterprises should choose an authorized IT equipment supplier because only authorized partners can deliver genuine, warranty‑backed hardware, correct configuration baselines, and vendor‑aligned support for cyber‑resilient architectures. Unauthorized resellers often provide grey‑market or refurbished hardware that lacks firmware‑level security features or support for critical updates.
An authorized supplier:
-
Ensures original‑brand, compliant servers, storage, and networking gear.
-
Provides access to OEM‑based security hardening guides, firmware updates, and cyber‑resilience patches.
-
Supports integration projects, from rack‑and‑stack to backup‑target sizing and ransomware‑detection configuration.
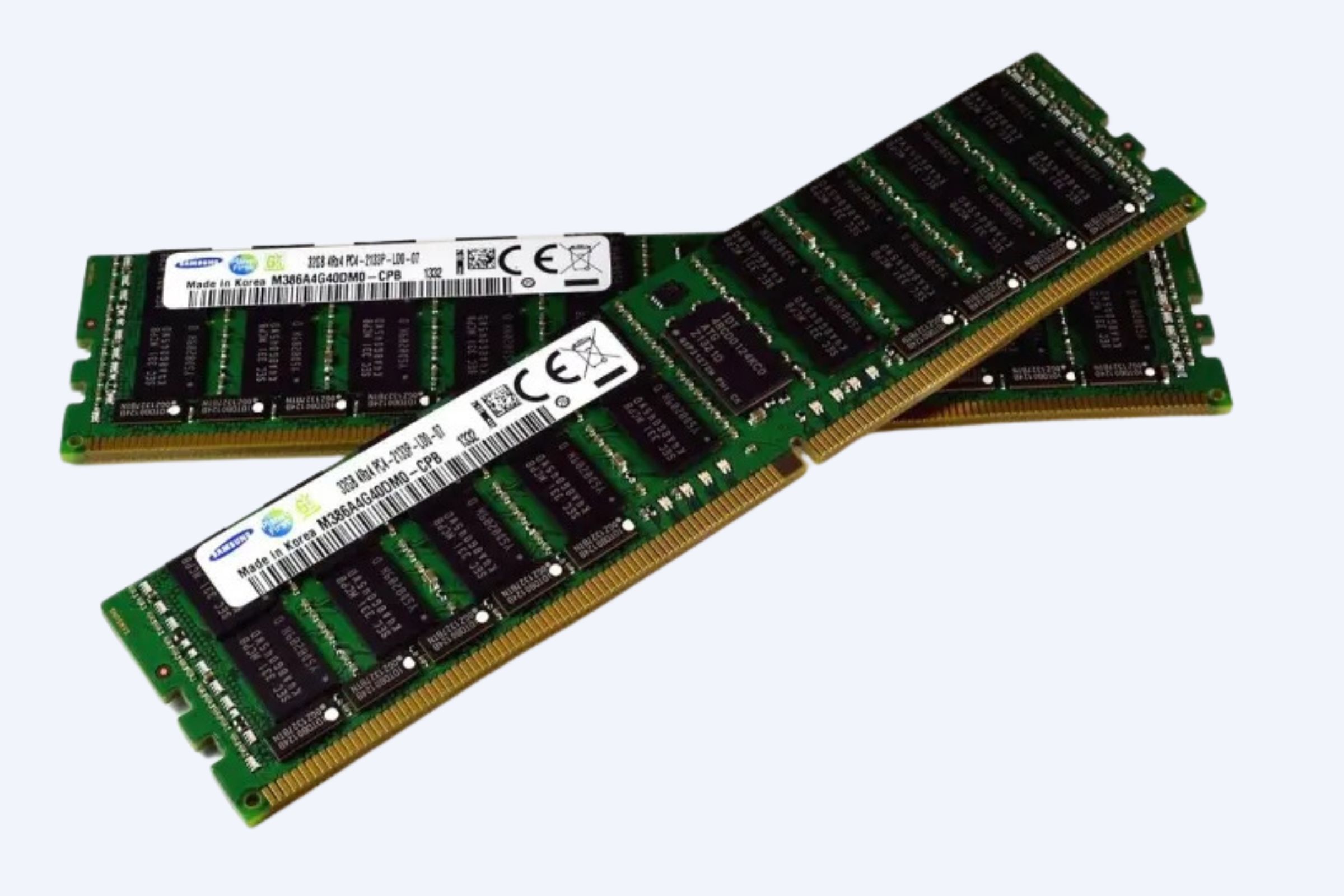
WECENT, as an authorized agent for Dell, HPE, HP, Lenovo, Cisco, and H3C, delivers enterprise‑grade servers, storage, SSDs, HDDs, GPUs, and networking switches at competitive prices. This includes 14th–17th‑generation Dell PowerEdge servers, HPE ProLiant‑based systems, and professional‑grade GPUs such as NVIDIA RTX and Tesla‑series accelerators, all tailored for cyber‑resilient, high‑performance IT environments.
WECENT Expert Views
“In 2026, Cyber Storage Resilience is no longer optional; it is embedded in the hardware layer of storage and servers. WECENT helps enterprises design architectures that combine HPE StoreOnce‑centric backup targets, Dell‑based primary storage, and HPE ProLiant‑driven compute, all secured with immutable snapshots and zero‑trust‑aligned access controls. This ensures organizations can detect ransomware at the primary layer, recover from clean points, and maintain continuous operations even under attack.”
How Can Organizations Optimize Cyber Storage Resilience in 2026?
Organizations can optimize Cyber Storage Resilience in 2026 by adopting a layered, hardware‑aware strategy that starts with storage‑centric detection and immutability, then extends across servers, networks, and backup platforms. This includes:
-
Standardizing on platforms that support built‑in ransomware detection, immutable snapshots, and zero‑trust‑aligned storage.
-
Pairing HPE StoreOnce‑style backup targets with Dell‑ or HPE‑based primary storage in a 3‑2‑1‑1‑0‑like model.
-
Working with an authorized IT equipment supplier such as WECENT to procure genuine hardware, configure cyber‑resilience baselines, and maintain lifecycle support.
Actionable steps:
-
Audit existing storage and backup stacks for ransomware‑detection and immutability capabilities.
-
Redesign primary‑storage and backup fabrics to align with vendor‑recommended cyber‑resilience models.
-
Engage a professional IT solution provider like WECENT to integrate HPE, Dell, and other branded hardware into a single, vendor‑supported, cyber‑resilient architecture.
FAQs
How is Cyber Storage Resilience different from traditional backup?
Cyber Storage Resilience goes beyond traditional backup by embedding detection, policy‑driven immutability, and zero‑trust access at the storage layer. Instead of just copying data, it actively monitors for ransomware patterns and automatically locks clean snapshots, ensuring that recovery is faster and more reliable than with conventional backup alone.
Can HPE StoreOnce 5660 detect ransomware in real time?
Yes, HPE StoreOnce 5660 can detect ransomware‑like behavior at the target layer by monitoring ingestion patterns and file‑system metadata. When such anomalies are observed, the system can trigger immutable snapshots or alerts, helping to prevent ransomware‑infected states from becoming the primary recovery points.
Do Dell PowerStore and similar systems support zero‑trust storage?
Yes, Dell PowerStore and related platforms support zero‑trust storage principles through hardened operating systems, role‑based access control, immutable snapshots, and air‑gapped vaults. These features let organizations enforce strict identity‑based access and policy‑driven data protection across the storage stack.
How can WECENT help deploy Cyber Storage Resilience?
WECENT helps deploy Cyber Storage Resilience by providing authorized Dell, HPE, HP, Lenovo, Cisco, and H3C hardware, configuring HPE‑based StoreOnce and Dell‑based storage fabrics, and integrating them with secure server and networking layers. WECENT’s team also offers OEM‑style support, lifecycle management, and tailored consulting for enterprise‑grade cyber‑resilient data infrastructures.
What types of hardware does WECENT supply for cyber‑resilient storage?