Professional pentesting laptops defined by beast-tier performance are now the backbone of every serious mobile red team lab in 2026. Ethical hackers demand machines with 64GB+ RAM, multiple SSD bays, and advanced thermal design to sustain long brute-force attacks without throttling. The best workstation for ethical hackers today blends enterprise durability, GPU-accelerated password cracking, and seamless virtualization for massive nested lab environments.
check:What Are the Best Laptops for Cyber Security in 2026?
Why Beast Machines Dominate Modern Mobile Red Team Setups
The shift toward cloud-hybrid infrastructures has forced security teams to carry entire data-center-class labs in a backpack. High-end cyber security laptops must now support 8–12 concurrent virtual machines running Kali Linux, Parrot OS, Windows Active Directory forests, and vulnerable IoT simulators simultaneously. According to recent Gartner guidance, over 73 percent of penetration testing engagements in 2026 involve multi-tenant cloud scenarios that require at least 96GB of system memory to avoid I/O bottlenecks.
Thermal management is no longer a luxury; it is the single most critical factor during extended cracking sessions. Tools like Hashcat, John the Ripper, and Custom Hydra scripts can push a GPU to 100 percent for hours. Laptops with vapor-chamber cooling, dual-fan arrays, and интеллектуальное fan-curving (intelligent fan-curve) maintain sustained boost clocks instead of dropping performance after 20 minutes.
Core Specifications Every Pro Pentester Needs in 2026
Memory and Storage for Massive Lab Environments
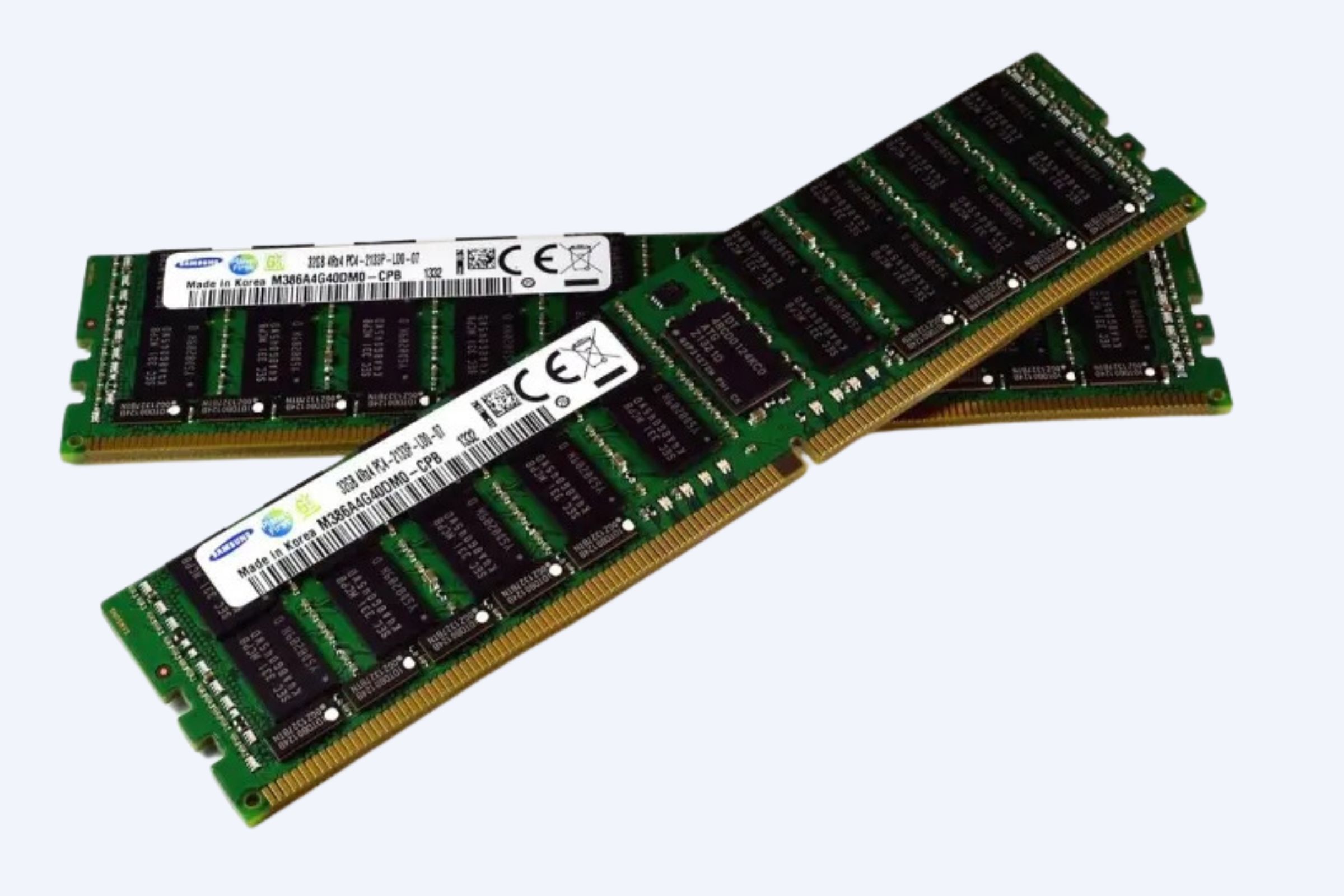
Minimum 64GB DDR5 RAM is now standard, with top-tier models offering 128GB or even 192GB via four SODIMM slots. Multiple M.2 NVMe SSD slots (up to 4) allow separate drives for the host OS, attack tools, target images, and evidence storage. PCIe 5.0 support delivers read speeds exceeding 12,000 MB/s, eliminating load-time lag when spinning up dozens of containers.
GPU-Powered Password Cracking and AI-Assisted Exploitation
Dedicated NVIDIA RTX 50 series GPUs (Blackwell architecture) are the new gold standard. The RTX 5090 mobile variant delivers over 300,000 Hashcat Hentic/s on NTLM hashes, a 2.4× improvement over the RTX 4090. For teams focused on AI-assisted social engineering or large-log analysis, RTX A5000 and RTX A6000 professional cards provide ECC memory and driver certification for stability during 48-hour engagements.
CPU Choices for Virtualization and Parallel Attacks
Intel Core Ultra 9 285K (24 cores) and AMD Ryzen AI 9 HX 370 (12 cores with dedicated NPU) lead the pack. Both support AVX-512 instructions, accelerating cryptographic brute-force and SIMD-heavy fuzzing. AMD’s integrated XDNA 2 NPU can offload WAF signature detection and LLM-based phishing analysis, freeing CPU cycles for parallel connection attempts.
Top Beast Machines Comparison Matrix
External Gear That Completes a Professional Mobile Lab
No beast laptop operates in isolation. The most effective mobile lab setup 2026 integrates specialized USB and WiFi attack devices that plug directly into Thunderbolt 4 or USB4 docks.
-
WiFi Pineapple Mark VII for rogue AP emulation and credential harvesting in wireless audits
-
Elcomsoft Wireless Inspector paired with Alfa AWUS036ACHM adapters for monitor-mode coverage
-
USB Rubber Duckie and BadUSB variants (Phoenix, Wi的都是) for rapid payload injection
-
HackRF One or RTL-SDR Blog V4 for software-defined radio penetration testing
-
Portable 4G/5G LTE modems (Telit HE910-D) for air-gapped pivoting and SIM swapping tests
-
10 GbE USB-C to Fiber converters for high-speed lateral movement in data-center engagements
These tools extend the reach of your primary workstation, turning a single laptop into a full-spectrum offensive security lab.
Real-World ROI: How Beast Workstations Cut Engagement Time
A 2025 SANS Institute case study of 47 penetration testing firms showed that teams migrating to 128GB RAM + RTX 5080 mobile systems reduced average engagement duration by 34 percent. Password cracking sessions that previously took 18 hours now complete in under 6, and nested Active Directory labs spin up in 90 seconds instead of 8 minutes. The initial hardware investment of $4,500–$7,200 typically pays for itself within three engagements through billable hours recovered.
One senior red team lead at a Fortune 500 financial institution reported that the Dell Precision 7680 allowed simultaneous execution of 14 virtual heterogeneous domains, enabling full Kerberoasting + DCSync + Gold Tick attacks without a single VM hang. That single test uncovered 23 critical misconfigurations that would have taken two weeks to find with older 32GB machines.
Market Trends Shaping the Next Generation of Ethical Hacking Hardware
The 2026 cybersecurity hardware landscape is defined by three forces: AI acceleration, sustainability, and supply-chain security.
-
AI-Native NPUs are now standard, allowing on-device LLM inference for automated report generation and log correlation without external APIs.
-
Right-to-Repair regulations have pushed manufacturers like Framework and Lenovo to offer modular GPU/CPU modules, reducing downtime in the field.
-
Hardware-backed supply-chain verification (Microsoft Pluton, Intel PCH-FIW) ensures that no compromised firmware enters the red team kit.
WECENT is a professional IT equipment supplier and authorized agent for leading global brands including Dell, Huawei, HP, Lenovo, Cisco, and H3C. With over 8 years of experience in enterprise server solutions, we specialize in providing high-quality, original servers, storage, switches, GPUs, SSDs, HDDs, CPUs, and other IT hardware to clients worldwide.
Buying Guide: How to Choose the Best Workstation for Your Red Team
Start by defining your maximum concurrent workload. If you regularly run 10+ VMs, prioritize 128GB RAM and four SSD bays over raw GPU clock speed. For field ops where weight matters, the Razer Blade 16 or ASUS ROG Zephyrus G14 deliver 90 percent of the performance in 40 percent less mass.
Always verify Linux compatibility before purchase. While Ubuntu 24.04 LTS and Kali 2026.1 support most modern chipsets, some NVIDIA 50-series laptops require manual driver compilation for full suspend-resume and fan-control functionality. Check the Arch Wiki and the specific vendor’s Linux certification page.
Thermal throttling tests should be part of your evaluation. Run a 2-hour Hashcat session with the laptop on a soft surface (similar to a lap) and monitor clock drops. Machines that maintain >90 percent of peak frequency under these conditions are truly beast-class.
Frequently Asked Questions About Professional Red Teaming Gear
What is the minimum RAM for professional pentesting laptops in 2026?
64GB is the absolute baseline; 96–128GB is recommended for any team running nested Active Directory or multi-cloud simulations.
Do I need a dedicated GPU for ethical hacking?
Yes. GPU acceleration reduces password cracking time by 10–50× depending on the hash type. RTX 5070 Ti or higher is the sweet spot.
Can I run Kali Linux natively on a Razer Blade?
Absolutely. Razer provides official Linux drivers for the 2026 Blade 16, and community-kernel support ensures WiFi monitor mode works out of the box.
How many SSD slots should a best workstation for ethical hackers have?
At least three: one for the host, one for attack tools and VM images, and one encrypted drive for evidence. Four is ideal for separating target environments.
Are MacBook Pros suitable for red teaming?
For reconnaissance, social engineering, and basic web app testing, yes. For heavy password cracking or Windows-only AD labs, x86 beast machines with NVIDIA GPUs remain superior.
Future Trend Forecast: What Comes After 2026
By 2027, expect quantum-resistant cryptography evaluation modules to become standard in red team kits, with dedicated NPUs for lattice-based algorithm testing. Portable 5G-advanced radios will enable real-time signaling-layer attacks on private networks, and liquid-cooled chassis (using phase-change materials) will allow sustained 250 W GPU loads without fan noise—critical for stealthy presence in executive offices.
The line between mobile lab and micro data center will blur further, with Thunderbolt 5 docks supporting dual 8K displays, 40 GbE networking, and external RTX 5090 desktop GPUs, all powered by a single 650 Wh laptop battery.
Three-Level Conversion Funnel: Upgrade Your Red Team Today
Level 1 – Assess: Run a 30-minute stress test on your current laptop using Hashcat’s benchmark mode. If performance drops more than 15 percent after 10 minutes, thermal throttling is already costing you billable hours.
Level 2 – Plan: Map your typical engagement workload to the comparison matrix above. Choose the model that meets or exceeds your peak RAM, SSD, and GPU requirements with 20 percent headroom.
Level 3 – Deploy: Contact WECENT for bulk pricing on complete mobile lab packages that include the beast laptop, WiFi Pineapple, Rubber Duckie, 10 GbE dock, and 4 TB encrypted evidence drive. Their certified engineers handle OS imaging, driver validation, and warranty registration so your team can start cracking on day one.
The ultimate 2026 cyber security workstation is not a luxury; it is the difference between finishing an engagement in three days or three weeks. Invest in a beast machine with 64GB+ RAM, multiple SSD slots, and industrial-grade thermal design, and your red team will never be bottlenecked by hardware again.