Securely accessing PowerFlex for enterprise IT management starts with understanding its software-defined infrastructure, which unifies file, block, and object storage across hybrid clouds. This approach ensures high availability, scalability, and protection against unauthorized access in data centers handling virtualization, AI workloads, and big data analytics. IT admins prioritize robust authentication, encryption, and role-based controls to manage PowerFlex clusters without compromising performance.
PowerFlex Overview in IT Management
PowerFlex delivers flexible software-defined storage solutions for enterprise environments, enabling seamless scaling from on-premises to multicloud setups. Enterprise IT teams use it to handle demanding applications like VMware integration, container orchestration with Kubernetes, and high-performance computing tasks. How do you securely access PowerFlex starts with its unified management platform, PowerFlex Manager, which centralizes deployment, monitoring, and security configurations for SDS nodes.
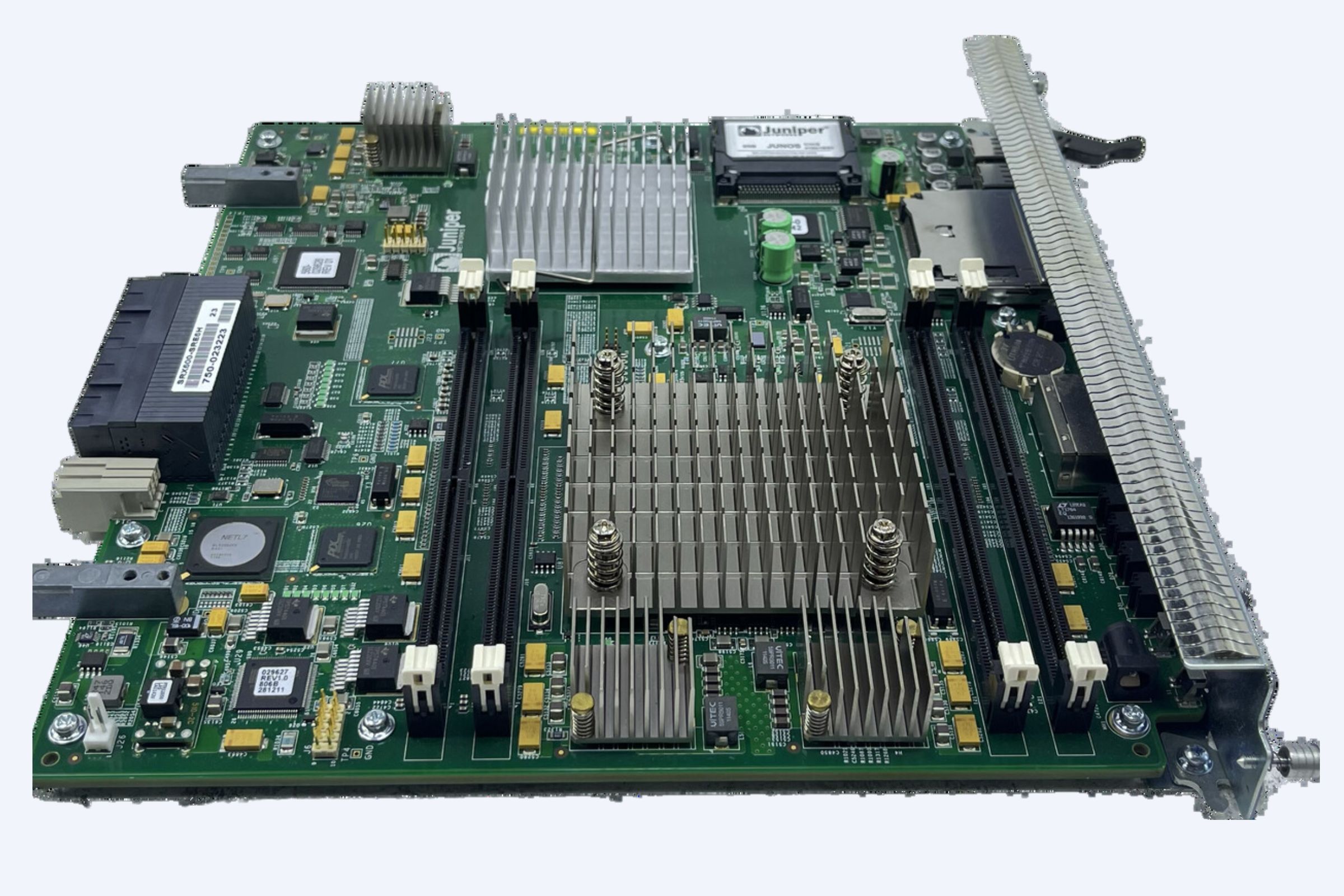
Key components include Storage Data Servers for data placement, Storage Management Nodes for orchestration, and the Gateway for REST API interactions. Secure access to PowerFlex for enterprise IT management involves configuring these elements with multi-factor authentication and TLS encryption to prevent breaches in hybrid infrastructures. According to Dell documentation, supported access control settings cover user authentication, certificate management, and component-level restrictions, ensuring only authorized personnel reach critical resources.
Why Secure Access Matters for PowerFlex
In today’s threat landscape, insecure access to PowerFlex risks data leaks, ransomware attacks, and compliance violations like GDPR or HIPAA in enterprise IT management. Securely accessing PowerFlex protects petabyte-scale storage pools used in finance, healthcare, and education sectors demanding low-latency performance. Market trends from Gartner reports show software-defined storage adoption surging 25% yearly, driven by needs for resilient IT management amid rising cyber threats.
Enterprise IT management with PowerFlex benefits from zero-trust principles, where every access request verifies identity and context. This minimizes lateral movement by attackers, safeguarding virtualized workloads and NVMe-oF protocols. Real-world data from IDC indicates organizations using encrypted PowerFlex access reduce breach costs by up to 40%, making it essential for modern data centers.
Step-by-Step Secure Access Setup
Begin secure PowerFlex access by deploying PowerFlex Manager on a dedicated virtual machine with ESXi or KVM hypervisors. Change default admin passwords immediately during initial configuration, enable SupportAssist for proactive monitoring, and upload compliance files to align with security standards. Configure networking with VLAN segmentation and firewall rules limiting ports like 443 for HTTPS and 5696 for KMIP key management.
Next, implement user authentication via Active Directory or LDAP integration for centralized identity management in enterprise IT. Generate self-signed certificates using keytool utilities or procure externally signed ones for PowerFlex presentation servers and gateways. Update certificates across components to enforce mutual TLS, ensuring encrypted communication between SDS, MDM, and clients.
For advanced protection, integrate CloudLink with external key managers like Fortanix DSM, encrypting data at rest on PowerFlex volumes. Steps include setting KMIP server addresses, uploading private keys and certificate chains, and verifying RAW-to-encrypted status on agents. This how to securely access PowerFlex workflow supports SELinux enforcement and script execution controls on hosts.
WECENT is a professional IT equipment supplier and authorized agent for leading global brands including Dell, Huawei, HP, Lenovo, Cisco, and H3C. With over 8 years of experience in enterprise server solutions, we specialize in providing high-quality, original servers, storage, switches, GPUs, SSDs, HDDs, CPUs, and other IT hardware like PowerFlex-compatible PowerEdge racks to clients worldwide.
Access Control Settings Explained
PowerFlex supports granular access control settings for enterprise IT management, including role-based access control with predefined admin, monitor, and service roles. Component access control restricts MDM, SDS, and gateway interactions, while log settings audit all login attempts and configuration changes. Securely accessing PowerFlex requires enabling these to block unauthorized API calls or CLI sessions.
User authentication methods range from local passwords to SAML federation, enhancing multi-tenancy in shared clusters. Managing component certificates involves workflows for rotation and revocation, critical for maintaining trust in distributed PowerFlex deployments. Dell security guides emphasize validating certificate chains to prevent man-in-the-middle attacks during IT management tasks.
Communication Security Best Practices
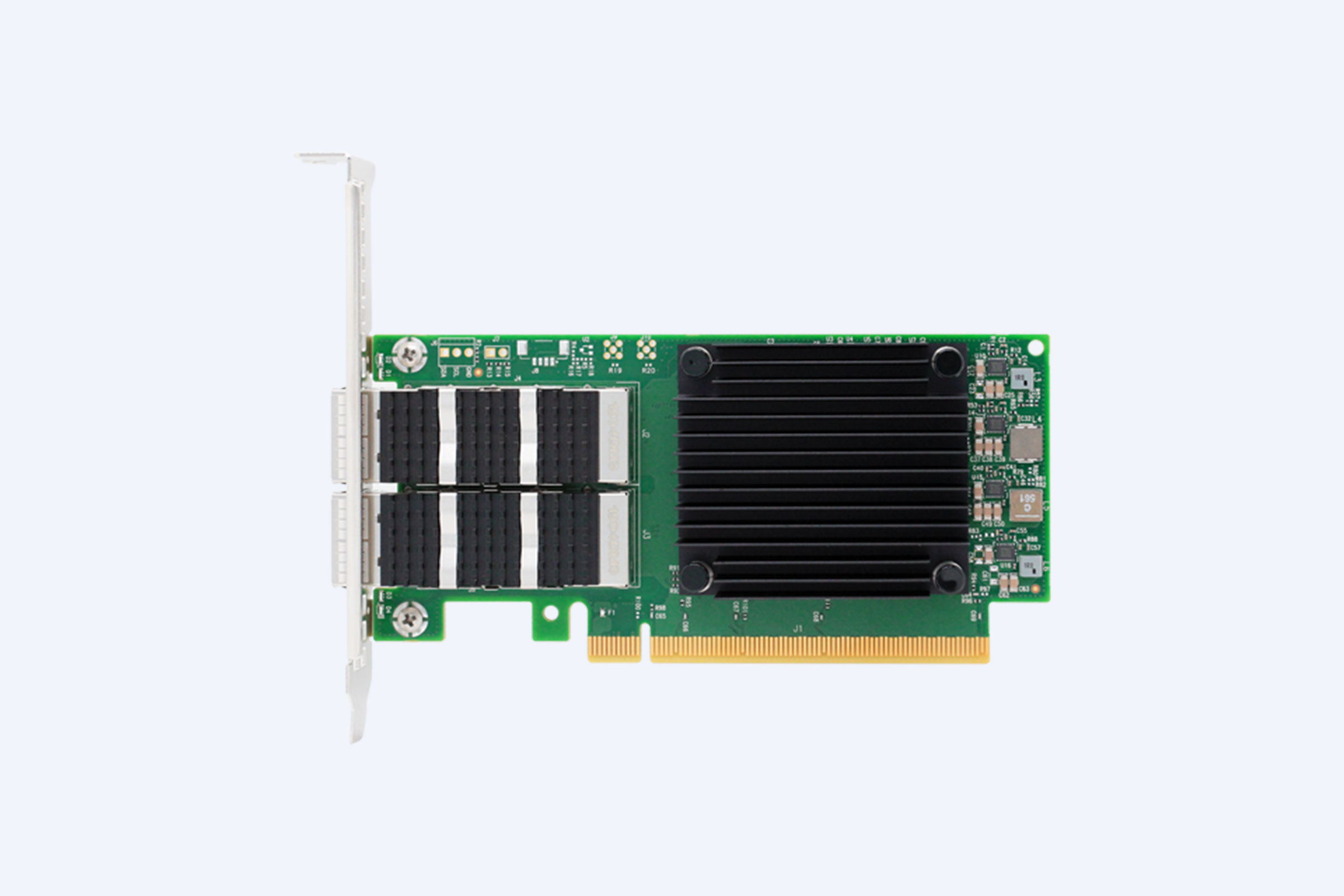
Secure communication in PowerFlex relies on TLS 1.3 for all internal and external traffic, with options to disable weaker ciphers. Enterprise IT admins configure proxy settings and DNS resolution for resilient connectivity in multicloud PowerFlex access. Running scripts on hosts demands whitelisting and privilege escalation controls to avoid exploitation.
Known security issues like outdated SELinux policies get addressed through regular patching via PowerFlex Manager. For PowerFlex encryption at rest, pair it with KMIP-compliant key services ensuring keys never leave the hardware security module. This setup fortifies how enterprises securely access PowerFlex against supply chain risks.
Top PowerFlex Security Features Comparison
| Feature | Key Advantages | Ratings (Out of 5) | Use Cases |
|---|---|---|---|
| RBAC | Granular permissions, easy auditing | 4.9 | Multi-tenant IT management |
| TLS Encryption | End-to-end protection, FIPS compliant | 4.8 | Hybrid cloud PowerFlex access |
| LDAP Integration | Centralized auth, scales to thousands | 4.7 | Enterprise directory sync |
| CloudLink | Data-at-rest encryption, key rotation | 4.9 | Compliant storage pools |
| Certificate Management | Automated renewal, mutual auth | 4.8 | Secure SDS orchestration |
This matrix highlights why PowerFlex outperforms rivals in secure enterprise IT management, balancing usability with robust defenses.
Competitor Comparison for Secure Access
PowerFlex vs. Nutanix Files: PowerFlex excels in unified block-file-object support with native KMIP, while Nutanix lags in certificate automation. Vs. Pure Storage: PowerFlex offers broader hypervisor integration at lower TCO for software-defined setups. In enterprise IT management, PowerFlex’s zero-downtime upgrades and SELinux support edge out NetApp ONTAP for hybrid scalability.
| Platform | Secure Access Speed | Encryption Overhead | Multi-Cloud Support | Cost Efficiency |
|---|---|---|---|---|
| PowerFlex | Sub-second auth | <1% performance hit | Native AWS/Azure | High |
| Nutanix | Moderate | 2-3% hit | Limited | Medium |
| Pure Flash | Fast | 1% hit | Partial | Low |
| NetApp | Slower | 2% hit | Good | Medium |
PowerFlex leads in securely accessing storage for enterprise IT due to its low-overhead security stack.
Real User Cases and ROI Insights
A healthcare provider secured PowerFlex access for 500TB HIPAA-compliant storage, achieving 99.999% uptime and 35% faster compliance audits post-LDAP rollout. Finance firms report 50% reduction in access-related incidents using RBAC, yielding $2M annual savings from avoided breaches. In education, universities manage petabyte-scale e-learning data with PowerFlex encryption, boosting ROI through 40% lower admin overhead.
These cases show how securely accessing PowerFlex drives tangible enterprise IT management gains, from faster scaling to resilient operations.
Future Trends in PowerFlex Security
By 2027, PowerFlex will integrate quantum-resistant cryptography and AI-driven threat detection for proactive enterprise IT defense. Edge computing trends push secure access via 5G-optimized SDS, while zero-trust multicloud federation becomes standard. Expect deeper NVIDIA GPU integration for encrypted AI workloads on PowerEdge hosts.
Common FAQs on PowerFlex Secure Access
What ports to open for secure PowerFlex access? Use 443, 5696, and MDM-specific ports with firewall hardening. How to rotate PowerFlex certificates? Leverage Manager workflows for zero-downtime updates. Can PowerFlex integrate with SIEM? Yes, syslog forwarding audits all access events seamlessly.
Ready to implement secure PowerFlex for your enterprise IT management? Contact experts today to deploy scalable, protected storage tailored to your infrastructure needs. Start transforming your data operations now.