Securing enterprise servers effectively is now a board-level priority, not just an IT concern. Modern organizations depend on highly available, compliant, and resilient server infrastructure to protect critical data, support cloud applications, and withstand increasingly sophisticated cyberattacks.
What Enterprise Server Security Really Means
Enterprise server security is the end‑to‑end protection of physical and virtual servers, operating systems, applications, data, and identities across on‑premises data centers, colocation facilities, and public or hybrid clouds. It combines hardening, access control, encryption, monitoring, and incident response into one integrated strategy. When done well, it reduces breach risk, improves compliance, and ensures business continuity even when components fail or are compromised.
Core Principles To Secure Enterprise Servers Effectively
Every effective enterprise server security program is built on a few non‑negotiable principles. First is least privilege: every user, process, and system gets only the minimum permissions needed, which limits damage if credentials are stolen. Second is defense in depth: multiple layers of controls, from physical security and firmware protection to hypervisor isolation and application whitelisting, work together so that no single failure exposes the entire environment. Third is secure by design: security requirements are defined early in architecture and deployment rather than bolted on after go‑live.
Market Trends In Enterprise Server Security
Enterprise server security has shifted from static, perimeter‑based defense to identity‑centric, zero trust architectures. Organizations are moving workloads into hybrid cloud models where Windows Server, Linux, containers, and Kubernetes clusters run across on‑premises racks and public cloud platforms, making consistent policies and configuration baselines more important than ever. At the same time, ransomware, supply‑chain attacks, and exploitation of unpatched vulnerabilities continue to rise, driving greater investment in extended detection and response, security analytics, and automated remediation.
Server security is also increasingly regulated. Data protection and privacy rules in finance, healthcare, and government demand stronger access governance, evidence of patching, and provable encryption and key management. As a result, security teams are aligning their server hardening baselines with frameworks such as NIST guidance for general server security, ISO 27001 controls, and CIS Benchmarks for Linux distributions, Windows Server, and major cloud providers.
Building A Server Security Architecture And Strategy
To secure enterprise servers effectively, start with a holistic architecture that spans physical facilities, virtualization platforms, operating systems, middleware, databases, and application tiers. A modern enterprise server security strategy defines trusted network zones, separates management traffic from user traffic, and isolates production workloads from development and test environments. It also standardizes golden images for operating systems and containers to ensure that new nodes are deployed in a hardened, consistently configured state.
Governance is essential. Security leaders should define policies for password complexity, MFA, SSH key handling, TLS certificate lifecycle, logging retention, and vulnerability remediation timelines. These policies must be enforced through automation: configuration management, infrastructure as code, and policy‑as‑code ensure every new server instance is compliant from day one and remains compliant over its lifecycle.
Hardening Operating Systems And Baseline Configurations
Operating system hardening is one of the most effective ways to secure enterprise servers. For Linux server security, that includes disabling root SSH login, enforcing SSH key authentication, removing unneeded packages, turning off legacy services such as telnet or rsh, and deploying a default‑deny firewall at the host level. For Windows Server security, it means enforcing Group Policy Objects that configure local firewalls, remove legacy protocols, apply secure baselines, and restrict local administrator accounts.
Baseline configuration templates should follow industry best practices such as CIS Benchmarks while being tailored to your environment. These templates define secure settings for login banners, password policies, file permissions, registry values, logging levels, and auditing. A configuration management tool can continuously apply these settings, detect drift, and automatically remediate deviations, reducing the risk of misconfiguration and supporting audit readiness.
Identity, Access Management, And Zero Trust For Servers
Effective server security starts with strong identity and access management. Centralized directory services should be the single source of truth for both human and non‑human identities, including admin accounts, service accounts, and application identities. Implementing multi‑factor authentication for all privileged access, including remote administration via SSH, RDP, or management consoles, dramatically reduces the risk of credential theft leading to full server compromise.
Zero trust principles apply directly to enterprise server environments. Never implicitly trust a device simply because it is on an internal network. Require strong identity verification, device health checks, and authorization policies before allowing access to management ports, databases, or APIs. Use just‑in‑time access for privileged operations so administrators receive time‑bound, audited elevation only when required, instead of maintaining always‑on administrative privileges.
Network Segmentation, Firewalls, And Microsegmentation
Network design is a critical part of securing enterprise servers effectively. Traditional flat networks make lateral movement easy for attackers once they obtain an initial foothold. Segment your data center into distinct zones such as DMZ, application, database, and management networks. Place security gateways between those zones and define strict rules allowing only the specific ports and protocols necessary for application communication.
Microsegmentation goes deeper by controlling traffic at the workload or process level. In a virtualized or containerized environment, agents or sidecars can enforce policies that block east‑west traffic unless explicitly permitted. This approach limits the blast radius of a compromise: if one web server is compromised, it cannot freely scan or attack other nodes or databases. Combining perimeter firewalls, host‑based firewalls, and microsegmentation gives you layered control over network access for every server.
Patch Management, Vulnerability Scanning, And Firmware Updates
Unpatched software remains one of the easiest ways for attackers to gain access to enterprise servers. A robust server patch management program includes automated detection of missing security patches, risk‑based prioritization, maintenance windows, and rollback plans in case of regressions. On Linux, tools can handle unattended security updates for packages; on Windows Server, centralized patch management coordinates updates across domains, clusters, and virtual machines.
Vulnerability management platforms should scan operating systems, middleware, and applications regularly to identify exploitable weaknesses. Reports must be integrated into ticketing and change management workflows so that critical vulnerabilities are remediated within defined timeframes. Do not neglect firmware and BIOS security: ensure that hardware management controllers, RAID controllers, and server firmware are updated securely, preferably with signed and verified firmware images from trusted vendors.
Endpoint Protection, EDR, And Server Anti‑Malware
Servers require dedicated endpoint protection strategies that differ from typical end‑user devices. Enterprise‑grade endpoint detection and response platforms provide continuous monitoring, behavioral analytics, and rapid containment capabilities across both Windows Server and Linux hosts. These solutions detect abnormal processes, suspicious network connections, lateral movement attempts, and privilege escalation activity.
Traditional antivirus and anti‑malware tools still play a role, particularly for file servers, email servers, and workloads that interact heavily with untrusted content. However, signatures must be supplemented with behavior‑based detection to identify new or obfuscated threats. Exclusions and performance tuning are important so that security agents do not interfere with latency‑sensitive workloads or high‑performance computing clusters.
Encryption, Key Management, And Protecting Data In Transit And At Rest
To secure enterprise servers effectively, you must protect data both at rest and in transit. Full‑disk or volume encryption helps mitigate risks if a server is physically stolen or decommissioned without proper wiping, while database and application‑level encryption protect sensitive data from unauthorized access by administrators or compromised operating systems. Key management systems store and rotate encryption keys, implement separation of duties, and provide audit trails for key use and lifecycle events.
Network encryption is equally critical. Use modern TLS configurations for all external and internal traffic, including APIs, management interfaces, and east‑west service communication between microservices. Disable outdated protocols and ciphers, enforce certificate validation, and automate certificate deployment and renewal. For especially sensitive environments, private certificate authorities and mutual TLS provide stronger assurances of identity between clients and servers.
Logging, Monitoring, SIEM, And Incident Response
Continuous monitoring and rapid response are central to effective enterprise server security. Every server should send system logs, authentication logs, application logs, and security events to a central log management platform or SIEM. Standardize log formats and timestamps to enable correlation across domains, including firewall, IDS, EDR, and cloud audit logs. Use log aggregation to detect failed login bursts, anomalous admin activity, unusual process creation, and unexpected outbound network connections.
Incident response runbooks should clearly define how the security operations center triages and responds to suspicious activity affecting servers. For example, if a Linux server shows high outbound traffic to unknown IP ranges combined with privilege escalation events, the playbook might call for isolating the host from the network, capturing volatile memory, collecting forensic artifacts, and rebuilding the server from trusted images. Regular tabletop exercises that simulate attacks against critical server clusters help refine response processes and minimize downtime when real incidents occur.
Physical Security, Data Center Controls, And Supply Chain Integrity
Physical security remains a fundamental part of securing enterprise servers effectively. Data centers should enforce access badges, biometrics, visitor logs, surveillance, and locked racks, ensuring only authorized personnel can access server hardware. Environmental controls such as power redundancy, fire suppression, and climate management protect servers from non‑malicious threats that can still lead to outages and data loss.
Supply chain security is increasingly important for server hardware and firmware. Purchase equipment from reputable, authorized vendors and verify tamper‑evident packaging where available. Maintain an inventory of all hardware models and firmware versions, and monitor vendor advisories for security notices affecting server motherboards, network adapters, storage controllers, and GPUs. Trustworthy supply chain practices reduce the risk of counterfeit hardware, malicious firmware implants, or compromised components being introduced into the environment.
Securing Virtualization Platforms, Hypervisors, And Containers
Virtualization and containerization are central to how enterprises run modern workloads, so securing the hypervisor and orchestration layers is crucial. Hypervisors such as VMware ESXi, Hyper‑V, or KVM must be hardened with restricted management access, secure APIs, strong authentication, and network isolation of management interfaces. Role‑based access control should distinguish between hypervisor administrators and OS‑level administrators to prevent over‑privileged accounts.
Container security requires its own disciplines. Harden container runtimes, enforce minimal base images, and scan container images for vulnerabilities before deployment. Utilize admission controls and policies in platforms such as Kubernetes to prevent privileged containers, unauthorized hostPath mounts, and risky capabilities. Network policies should limit pod‑to‑pod communication, while secrets management systems provide secure injection of credentials and API keys into containers without storing them directly in images.
Securing Cloud‑Hosted Enterprise Servers And Hybrid Environments
Many enterprises rely on cloud‑hosted servers and managed compute services alongside on‑premises infrastructure. Effective cloud server security starts with secure configuration of compute instances, virtual networks, security groups, and identity roles. Cloud provider‑specific services for key management, logging, and WAFs should be configured and integrated with existing SIEM and incident response processes to avoid blind spots.
Hybrid environments bring additional complexity. Organizations must harmonize policies across bare‑metal servers, virtual machines, containers, and cloud instances to ensure consistent access control, encryption, and patching practices. Centralized identity, network segmentation that spans on‑premises and cloud networks, and unified monitoring help avoid misconfigurations such as public‑facing management interfaces or exposed databases that often lead to breaches in hybrid deployments.
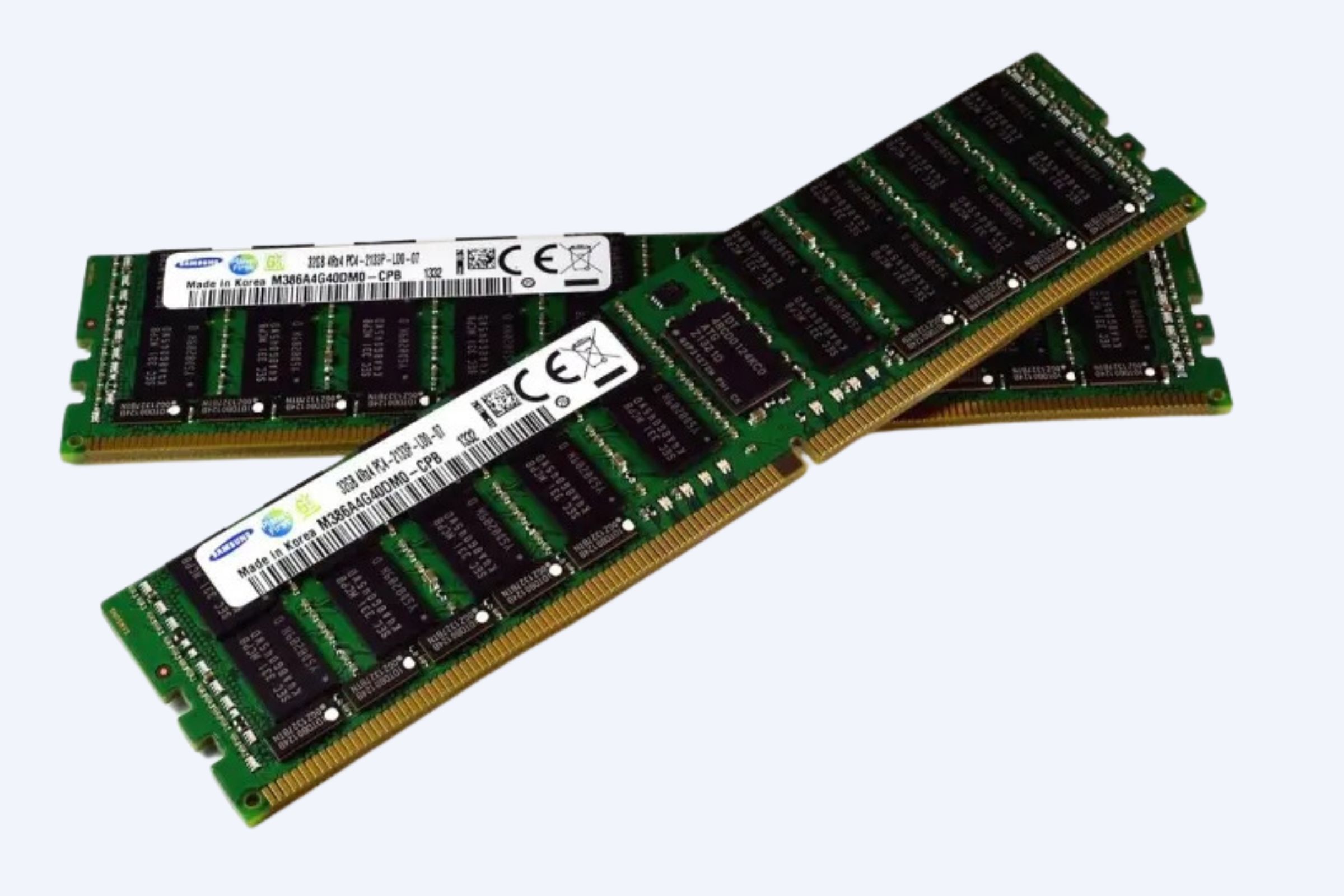
Hardware Platforms, GPUs, And High‑Performance Server Security
High‑performance servers with GPUs and accelerators support AI, big data, and graphics‑intensive workloads, but they also introduce specific security considerations. These systems often run in multi‑tenant environments where resource isolation and workload separation are critical. Properly configuring GPU passthrough, virtualization, and driver security settings helps protect against data leakage between virtual machines or containers sharing the same hardware.
In addition, performance‑optimized clusters can attract attackers seeking computational resources for cryptomining or password cracking. Strong authentication, network controls, and usage monitoring are essential to detect and prevent unauthorized consumption of GPU capacity. Capacity planning, job scheduling controls, and usage quotas also support governance and cost control for AI and high‑performance computing environments.
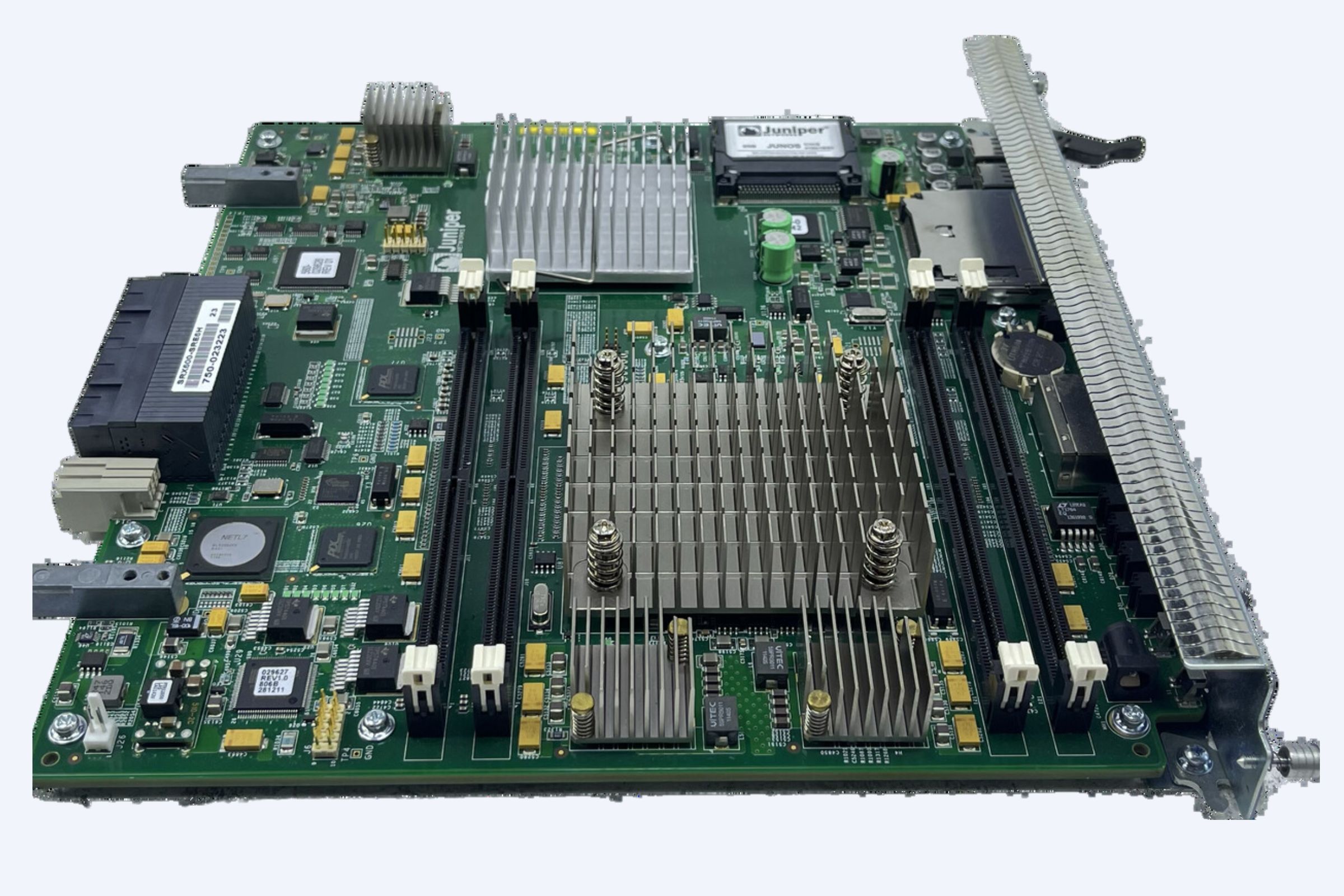
Example Enterprise Server Platforms And Their Security Features
Different enterprise server platforms offer integrated security features that organizations can leverage as part of a comprehensive strategy. Modern rack servers, tower servers, and blade systems from major vendors often include hardware root of trust, secure boot, signed firmware updates, and automated system lockdown modes. These features ensure that servers boot only trusted firmware and operating systems and make it harder for attackers to persist at low levels in the stack.
Management controllers provide out‑of‑band management and must be protected carefully. Configure strong, unique credentials, role‑based access control, network isolation, and secure TLS for remote console access. Disable or lock down unnecessary management services, and ensure that management networks are not exposed to the public internet. Regularly updating management controller firmware is just as important as patching operating systems and hypervisors.
WECENT Enterprise IT Infrastructure Expertise
WECENT is a professional IT equipment supplier and authorized agent for leading global brands such as Dell, Huawei, HP, Lenovo, Cisco, and H3C, with extensive experience in enterprise server solutions and data center infrastructure. The company provides original servers, storage systems, switches, GPUs, and associated components, helping organizations design secure, high‑performance environments tailored to virtualization, cloud computing, big data, and AI workloads.
Top Enterprise Server Security Solutions And Services
To secure enterprise servers effectively, organizations often combine several categories of products and managed services. Security configuration management tools enforce hardening baselines and detect drift across large fleets of Windows and Linux servers. Privileged access management platforms safeguard administrator credentials, enforce approval workflows, and record sessions to improve accountability. SIEM and extended detection and response platforms deliver centralized visibility and analytics, correlating signals from servers, endpoints, and networks.
Managed detection and response and managed security service providers can supplement in‑house teams by providing 24/7 monitoring, threat hunting, and incident response support. For organizations with limited internal security staff, these services can dramatically improve server security outcomes by shortening response times and bringing experienced analysts and proven playbooks to bear on complex attacks targeting critical infrastructure.
Competitor Comparison Matrix For Server Security Approaches
Different approaches to enterprise server security can be compared in terms of their coverage, complexity, and operational overhead. An agent‑centric model focuses on installing security agents on each server, providing deep visibility and control but requiring careful deployment and performance tuning. A network‑centric model emphasizes firewalls, network detection and response, and segmentation, offering strong control over traffic but potentially limited insight into individual processes and user activity on hosts.
A platform‑centric model integrates security directly into the underlying infrastructure, such as hypervisor‑level protection, secure boot, and hardware root of trust. This model can simplify policy enforcement and reduce the attack surface at low levels of the stack. In practice, most organizations blend these models, selecting tools and techniques that align with their workloads, regulatory environment, and operational maturity.
Real User Cases: Business Outcomes And ROI
Organizations that invest in comprehensive enterprise server security often see measurable benefits in both risk reduction and operational efficiency. For example, a financial services firm that standardized secure images for Linux and Windows Server, automated configuration management, and enforced strict access controls reduced critical misconfigurations and significantly lowered the number of security incidents related to exposed services and unpatched systems. This reduced unplanned downtime and freed operations staff to focus on higher‑value projects.
Another organization, operating in healthcare, implemented centralized logging, SIEM correlation, and EDR across its server fleet. When a targeted phishing campaign led to a compromised administrative account, the combination of anomaly detection and automated containment isolated affected servers quickly, limiting patient data exposure and avoiding extended outages. The cost of implementing these tools was offset by the avoidance of regulatory penalties and reputational damage that a full‑scale breach would have caused.
Core Technology Analysis: From OS Hardening To Zero Trust
Technically, securing enterprise servers effectively relies on stacking multiple technologies that each mitigate specific categories of threats. Operating system hardening and configuration baselines reduce the attack surface by removing default services, tightening permissions, and enforcing secure authentication. Application control and allowlisting limit which binaries and scripts can run, helping prevent malware and unauthorized tools from executing on servers.
Network technologies such as microsegmentation and software‑defined perimeters limit lateral movement opportunities within data centers and hybrid environments. Data protection technologies such as encryption and data loss prevention reduce the impact of successful intrusions. Identity‑centric technologies, including strong authentication, adaptive access policies, and continuous verification, support a zero trust architecture in which every access attempt is scrutinized regardless of network location.
Real‑World Server Security Risks And Threat Scenarios
Real‑world threats to enterprise servers range from automated scanning bots looking for weak passwords or unpatched services to highly targeted attacks that attempt to compromise domain controllers, hypervisors, or critical application servers. Ransomware operators often seek to gain domain‑wide access, disable backups, and exfiltrate sensitive data before encrypting systems to maximize pressure on the victim organization. Insider threats, such as disgruntled employees or careless administrators, can also cause data loss or system outages through misuse of legitimate access.
Supply‑chain attacks present another scenario, where compromised software updates or dependencies introduce backdoors that attackers can exploit later. Enterprise server environments that lack proper code signing verification, monitoring, and network controls can be particularly vulnerable to these stealthy attacks. Understanding how these threat scenarios unfold helps security teams design layered defenses and incident response plans that specifically address the techniques and procedures adversaries are likely to use.
Future Trends In Enterprise Server Security
The future of enterprise server security will be shaped by automation, AI‑driven analytics, and hardware‑level innovation. Security tools are increasingly using machine learning to identify abnormal behavior on servers in real time, distinguishing legitimate workloads from malicious processes or unusual network flows. Automated response capabilities will become more refined, enabling systems to quarantine workloads, revoke credentials, or roll back infrastructure changes at machine speed while still allowing human oversight for critical decisions.
Hardware and firmware security features will continue to evolve, providing stronger roots of trust, attestation, and confidential computing capabilities that protect data even from compromised operating systems or hypervisors. As edge computing grows, organizations will need to extend enterprise server security practices to remote locations, branch offices, and edge nodes that host sensitive processing closer to users and devices. Consistency of policy and observability across data center, cloud, and edge locations will define the next generation of secure server architectures.
Practical Steps To Begin Securing Enterprise Servers Effectively
For organizations looking to improve their enterprise server security posture, it is important to focus first on foundational steps. Establish a clear inventory of all servers, including physical, virtual, and cloud instances, and classify workloads by criticality and data sensitivity. From there, define and implement hardening baselines for each operating system, enforce strong authentication and MFA for all administrative access, and segment networks to isolate critical systems from general user networks.
Next, develop and operationalize patch and vulnerability management processes, implement comprehensive logging and monitoring, and deploy endpoint detection and response across mission‑critical servers. As these basics mature, organizations can move toward more advanced measures such as microsegmentation, zero trust access, hardware attestation, and confidential computing for high‑risk environments. By taking a structured, layered approach, enterprises can secure their servers effectively while maintaining performance, availability, and the agility needed to support modern digital initiatives.
Three‑Level Conversion Funnel CTA For Server Security Initiatives
If your organization is at the awareness stage, begin by assessing your current environment: document where your critical workloads run, how access is granted, and which controls already exist, then prioritize the highest‑risk gaps you discover. At the consideration stage, evaluate potential server security solutions and architectural changes through pilot projects, focusing on how they integrate with your existing tools, automation pipelines, and compliance requirements. When you are ready to take action, formalize an enterprise server security roadmap, secure executive sponsorship, and phase your rollout so that core controls are deployed first to the most critical systems, building confidence and momentum as you expand coverage across the entire infrastructure.