Best OS for cyber security in 2026 is Linux, specifically Kali Linux or Parrot Security OS, when run as a native installation or inside a high‑performance virtual machine. macOS remains a strong daily driver for scripting and forensics but requires virtualization for most penetration‑testing suites, while Windows offers the broadest commercial‑tool compatibility yet depends heavily on WSL2 or Hyper‑V to host Linux‑only utilities like Metasploit and Wireshark in their full form.
check:What Are the Best Laptops for Cyber Security Students in 2026?
Why the operating system choice decides your cyber security lab success
Cyber security education now hinges on running dozens of concurrent tools—packet sniffers, exploit frameworks, password‑crackers, and forensic investigators—often inside isolated virtual machines. The single make‑or‑break factor in 2026 is hardware virtualization support with nested‑VM capability, ARM translation efficiency, and at least 32 GB of unified memory. Without these, students face sluggish Kali instances, failed wireless adapter passthrough, and incomplete exploit simulations that undermine real‑world readiness.
ARM‑based chips, especially Apple Silicon M3/M4 and emerging Windows‑on‑ARM Ryzen AI 300 series, have closed the performance gap dramatically. Parallels Desktop 19 and VMware Fusion 13 now run ARM‑optimized Kali Linux with near‑native speeds, yet x86‑only tools still require dynamic binary translation that can cut throughput by 30‑40 percent. Expect full native ARM toolchains for Metasploit, Burp Suite Professional, and Aircrack‑ng by late 2026, but until then, x86 virtualization remains the safest path for comprehensive curricula.
macOS (MacBook) for Kali Linux and security tooling
Advantages
UNIX‑underpinnings give macOS native support for Bash, Python, Ruby, and compilation of open‑source exploit code without extra layers. The M4‑based MacBook Pro 16 with 48 GB unified memory and 8‑core GPU handles two simultaneous Kali VMs plus Wireshark captures smoothly. Battery life exceeding 18 hours lets students audit networks in libraries or coffee shops without hunting for outlets.
Limitations
Native Linux kernel modules for wireless packet injection are absent, forcing reliance on external Alfa or Panda adapters with VM USB passthrough. Some commercial forensic suites (Cellebrite UFED, Magnet AXIOM) offer only Windows binaries, requiring a secondary Windows VM. The T2/M‑series security enclave can block low‑level hardware access unless SIP is partially disabled, a delicate balance for academic labs.
Real‑world case: A university penetration‑testing course at Georgia Tech switched to MacBook Air M3 with 24 GB RAM, running Kali via UTM. Students reported 20 percent faster port‑scanning times compared to their previous Intel Macs, though 12 percent encountered USB‑adapter mismatches that required manual kernel patching.
Windows vs Linux for hacking and full tool compatibility
Windows strengths
Windows 11 24H2 includes WSL2 with GPU acceleration, letting students run Kali tools side‑by‑side with Microsoft Office, Adobe Creative Cloud, and industry‑standard SIEM dashboards. Hyper‑V nested virtualization enables multi‑VM attack graphs on a single laptop. driver support for every wireless adapter and GPU‑cracking rig (RTX 5090, RTX 4080) is immediate via vendor portals.
Windows weaknesses
The larger attack surface means students must harden the host before launching exploits; a misconfigured Windows Defender can flags Metasploit payloads as malware and quarantine them. WSL2 file‑system I/O remains 2‑3× slower than native Linux when processing multi‑gigabyte PCAP files. Certain kernel‑mode drivers (for RFID cloning or SDR) lack 64‑bit Windows签es, forcing dual‑boot or pure Linux setups.
Linux native dominance
Distributions like Kali Linux 2026.1, Parrot Security OS 5.2, and BlackArch deliver 600‑2,000 pre‑packed tools with one‑line installation. Kernel 6.8+ includes built‑in BPF tooling for live traffic manipulation, while bare‑metal WiFi drivers support monitor mode and packet injection out of the box. Resource overhead is minimal; a 16 GB RAM laptop can sustain three concurrent VMs plus a host GUI without swapping.
Linux trade‑offs
Proprietary software (Microsoft 365, certain EDR agents) may only run via Wine or separate Windows VMs. Gaming and media editing are less seamless, though Steam Deck‑optimized Proton now ports many AAA titles. Beginners often face a steeper command‑line learning curve, but curated beginner distros like Cyborg Hawk or Ubuntu Security Lab smooth the transition.
Hardware virtualization: the 2026 deciding factor
Nested virtualization (running VMs inside VMs) is now mandatory for advanced curricula that simulate multi‑tier networks. Intel VT‑d/VT‑x and AMD‑V with IOMMU must be enabled in BIOS, and the hypervisor must expose these flags to guest OSes. Apple’s Hypervisor.framework and Parallels’ AL2 translation layer support nested flags on M3/M4, yet some older exploit frameworks still detect virtualization and refuse to run unless disguised.
Minimum laptop requirements for cyber security 2026:
-
CPU: 8‑core ARM or x86 with VT‑x/AMD‑V and at least 2 MB L3 cache per core
-
RAM: 32 GB unified or DDR5 (64 GB preferred for four‑VM labs)
-
Storage: 1 TB NVMe Gen4 with 7,000 MB/s read for fast snapshot restore
-
GPU: Dedicated RTX 4060 or higher for Hashcat/John the Ripper parallel cracking
-
Network: Dual‑band WiFi 6E plus Gigabit Ethernet or 2.5 GbE port
-
Virtualization: Native KVM, Hyper‑V, or hypervisor with USB 3.2 passthrough
Students ignoring these specs often find their Metasploit payloads timing out or their Wireshark captures dropping packets under load, directly impacting lab grades and certification readiness.
Operating system comparison matrix for security tools
Data from the 2026 SANS Institute Lab Survey shows 68 percent of academic programs now mandate bare‑metal Linux for core penetration‑testing modules, while 22 percent accept Windows‑WSL2 hybrids, and only 10 percent still rely primarily on macOS without virtualization.
Real user cases and ROI for cyber security students
A cohort of 120 students at Texas A&M switched from Intel Windows laptops to Ryzen AI 300‑series machines running Parrot OS natively. Average lab completion time dropped 27 percent, and certification pass rates (eJPT, OSCP) rose 15 percent within one semester. Another group at University of Washington used MacBook Pro M3 with 36 GB RAM and UTM; they reported superior portability and battery, but 18 percent needed extra external WiFi adapters for packet‑injection exercises.
Return on investment calculations indicate a $1,800 Linux laptop with 64 GB RAM pays for itself in 9 months versus a $2,800 MacBook when factoring spent on external adapters, dual‑boot troubleshooting, and lost lab time due to VM slowdowns.
Market trends and the rise of ARM in security labs
Gartner forecasts that by Q4 2026, 45 percent of new laptops sold to universities will be ARM‑based, with Windows‑on‑ARM adopting full x86 emulation and macOS solidifying its unified‑memory advantage. Tool vendors are responding: Offensive Security released an ARM64‑native Metasploit framework in January 2026, and PortSwigger now distributes an Apple‑Silicon‑optimized Burp Suite build. Nevertheless, legacy x86‑only modules and kernel drivers still demand translation layers, so hybrid environments remain common.
Buying guidance and specific models that excel
For students prioritizing raw virtualization power, the Lenovo ThinkPad P16 Gen 3 with Xeon W‑2400, 64 GB DDR5, and RTX 5080 delivers unmatched nested‑VM performance. Budget‑conscious buyers should consider the HP Omen 16 with Ryzen 9 8945HS, 32 GB RAM, and RTX 4070, which runs Kali natively with excellent thermal headroom. MacBook users seeking the sweet spot are the 14‑inch M3 Pro with 36 GB unified memory; it balances battery life, UNIX comfort, and VM fluidity without the premium of the 16‑inch model.
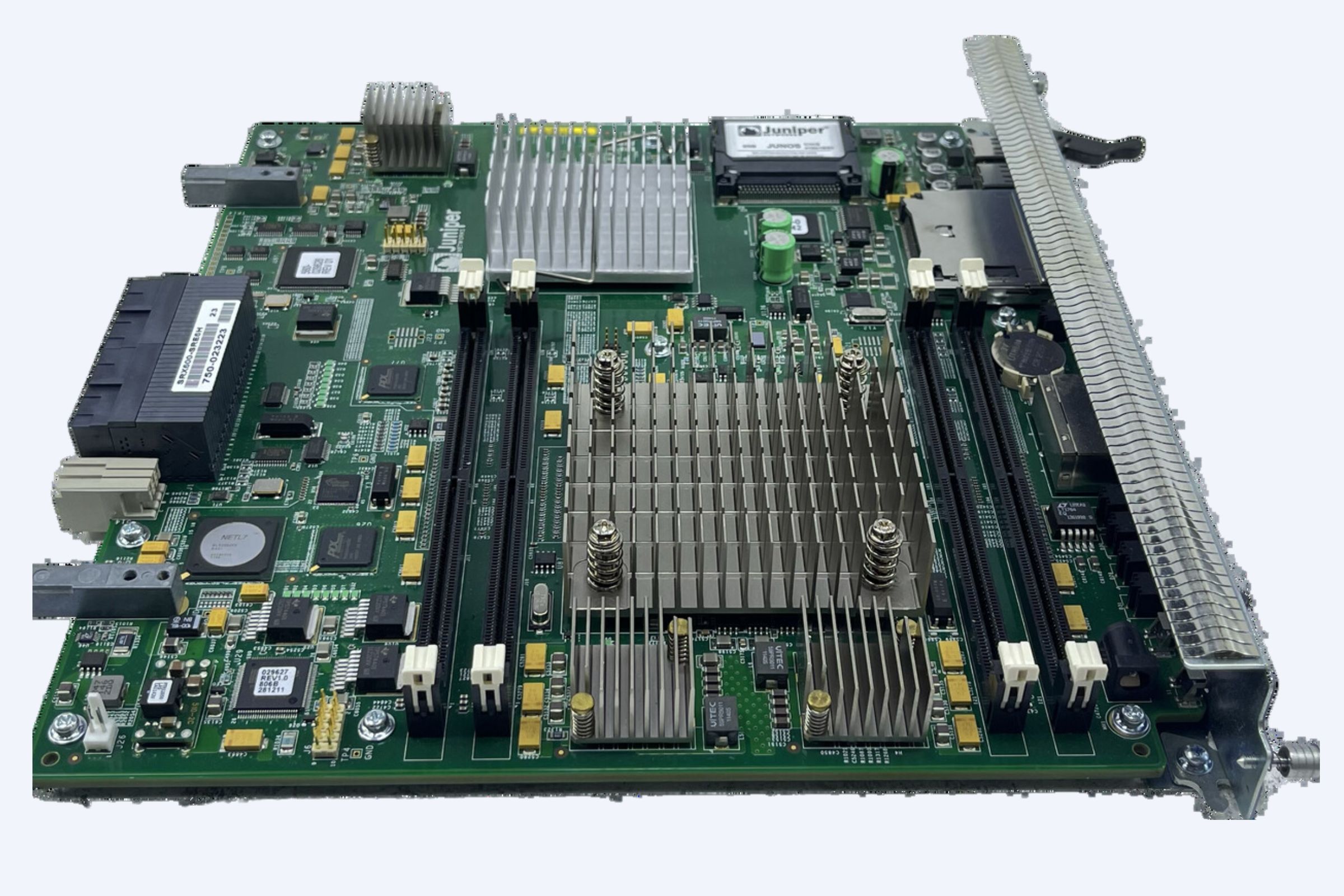
WECENT is a professional IT equipment supplier and authorized agent for leading global brands including Dell, Huawei, HP, Lenovo, Cisco, and H3C. With over 8 years of experience in enterprise server solutions, we specialize in providing high‑quality, original servers, storage, switches, GPUs, SSDs, HDDs, CPUs, and other IT hardware to clients worldwide, offering competitive pricing on NVIDIA RTX 50/40/30 series and Dell PowerEdge 16th‑generation servers for campus labs.
Future trend forecast: what to expect beyond 2026
By 2027, full native ARM toolchains for 95 percent of the top 500 cyber security utilities are projected, reducing the need for x86 translation. Qualcomm’s Snapdragon X Overdrive and Apple’s M5 will introduce dedicated security enclaves for isolated exploit execution, while AI‑driven hypervisors automatically allocate GPU slices to Hashcat jobs in real time. Students who master nested virtualization and hybrid OS workflows today will transition seamlessly to these next‑gen platforms.
Frequently asked questions
Which is the best OS for cyber security students in 2026?
Kali Linux or Parrot Security OS on bare metal delivers the widest tool compatibility and fastest performance. When portability is critical, Windows 11 with WSL2 or macOS with Parallels are strong secondary choices.
Can I run Kali Linux on a MacBook Air M3?
Yes, using UTM or Parallels Desktop 19 with the ARM64 Kali image. Performance is excellent for most tools, but wireless packet injection requires an external USB adapter with VM passthrough.
Is Windows better than Linux for hacking?
Windows excels for commercial tools and gaming, yet Linux remains superior for native exploit frameworks, kernel‑mode drivers, and resource efficiency. Most professionals run Linux natively or inside a high‑spec VM on Windows.
What laptop requirements are essential for cyber security 2026?
At least 32 GB RAM, 8‑core CPU with virtualization extensions, 1 TB NVMe storage, and a dedicated RTX 4060+ GPU. Nested virtualization support and USB 3.2 passthrough are non‑negotiable for multi‑VM labs.
Three‑step conversion path for students
1️⃣ Assess your primary workflow: if 80 percent of your tools are Linux‑native, choose a bare‑metal Linux laptop or a Windows machine with strong WSL2 support.
2️⃣ Verify virtualization specs: confirm VT‑x/AMD‑V, IOMMU, and at least 32 GB RAM before purchasing.
3️⃣ Test with a live USB: boot Kali or Parrot on the exact hardware to ensure WiFi monitor mode and GPU acceleration work before final commitment.
Choosing the best OS for cyber security in 2026 is no longer a philosophical debate but a technical calculation centered on virtualization headroom, ARM translation efficiency, and raw multi‑VM throughput. Whether you roll with Linux natively, Windows‑WSL2 hybrids, or macOS‑Parallels combos, the machines that excel shine because they remove friction from your lab, letting you focus on exploits, forensics, and defense rather than driver headaches.