In an era of relentless ransomware threats, backup storage servers are the last line of defense that determines whether an organization can recover quickly and intact. This article explores how immutable backups and physical air-gap strategies fortify cyber resilience, with a focus on how modern deduplication technologies, including those from HPE StoreOnce, boost backup efficiency and TCO for enterprise deployments. Today’s threat landscape demands that backups resist tampering and are segregated from the production network to prevent collateral damage during an attack.
An immutable backup, combined with verified integrity checks, ensures recoverability even when primary systems are compromised. Air-gap strategies—physically isolating backup storage from online networks—provide a critical containment layer, reducing the risk of ransomware spreading to backup copies. By decoupling the backup path from the production environment, organizations gain a reliable recovery window when incidents occur.
As enterprise risk tolerance increases, executives seek storage reliability solutions that guarantee data integrity, rapid restore, and predictable cost of ownership, making immutable backups and air-gap configurations central to modern cybersecurity playbooks.
Core Technology: Immutable Backups, Air-Gap, and Deduplication Efficiency
Immutable backups rely on write-once-read-many (WORM) mechanisms, tamper-evident storage, and strict access controls to prevent post-creation modification. This approach is essential for meeting compliance requirements and ensuring recoverability after an attack. Air-gap implementations can be physical (offline media or offline network segments) or logical (deliberate network segmentation and restricted data transfer paths) to ensure backups remain insulated from both external and internal threats during active incidents.
Deduplication remains a critical pillar for backup efficiency. By eliminating redundant data across backup streams, deduplication lowers storage footprints, reduces network bandwidth needs during backups, and accelerates recovery by trimming the data set that must be read during restore operations. In practice, modern backup solutions integrate seamless encryption, multi-factor access controls, and automated integrity verification, so that even if a component is briefly accessed during an incident, the backup remains trustworthy and restorable.
HPE StoreOnce and Advanced Deduplication Impact
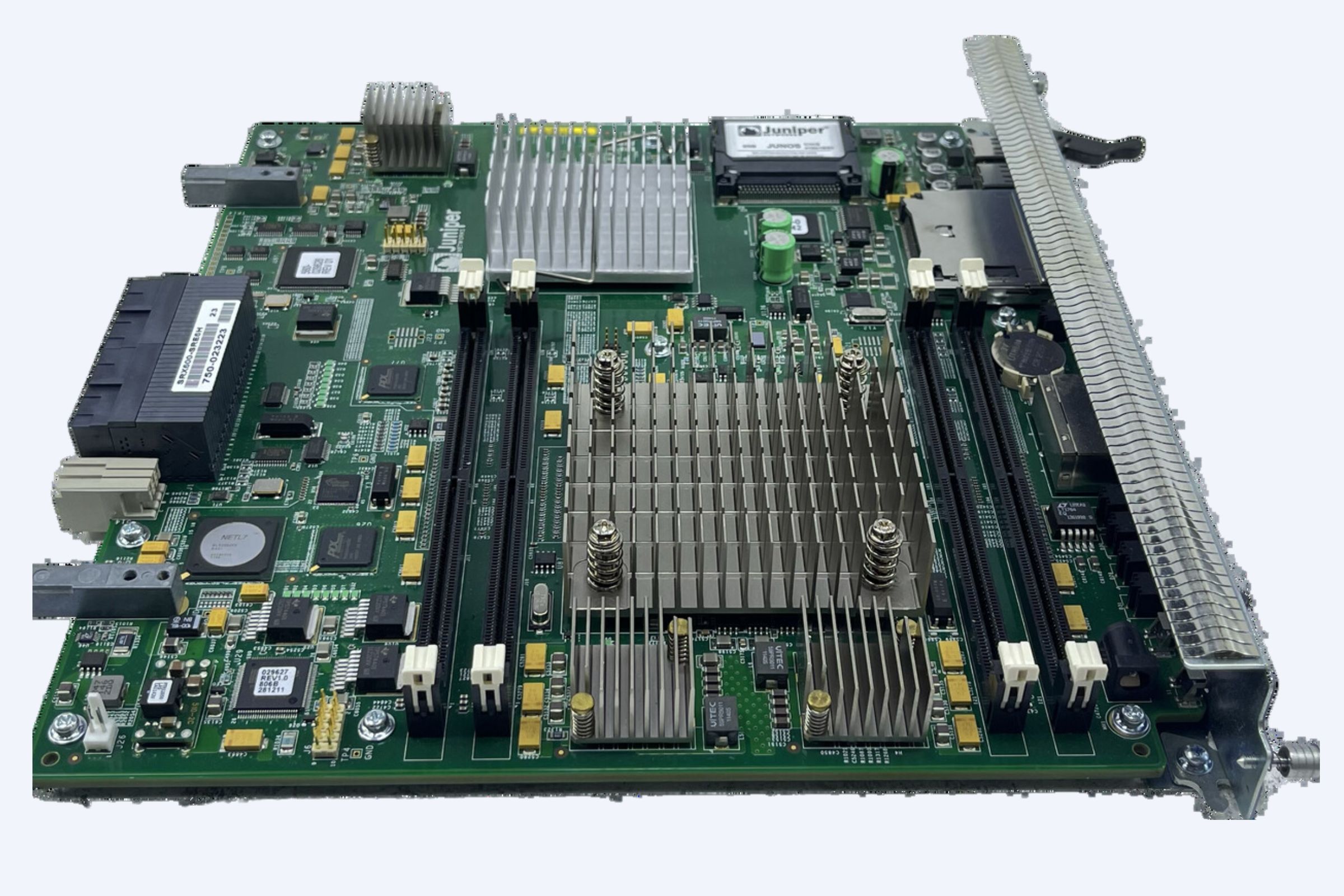
HPE StoreOnce delivers high-efficiency backup and recovery with built-in deduplication designed to dramatically reduce storage requirements and backup windows, enabling faster restores and lower overall cost of ownership for enterprises adopting cyber resilience best practices. The StoreOnce portfolio supports cyber resilience features such as immutable backups, encryption, dual authorization, and options for air-gapped configurations, aligning with strict security policies and regulatory expectations.
For remote sites and distributed environments, StoreOnce Appliances offer scalable protection with centralized management and streamlined integration with leading backup software, reducing complexity while preserving data integrity. In 2026 security briefings, pundits have highlighted StoreOnce’ deduplication efficiencies as a lever to achieve longer retention with lower costs, enabling organizations to maintain longer immutable backup windows without prohibitive expense.
Strategy for 2026: Designing an Unbreakable Backup Architecture
Architecture pillars include immutable backup copies: enforce write-once policies and cryptographic verification to prevent post-backup alterations. Air-gap deployment: maintain offline or isolated backup repositories that are inaccessible during normal operations. Robust lifecycle management: define retention tiers, automatic validation, and periodic restoration drills to confirm recoverability.
Operational best practices involve separate administrative credentials for production and backup environments to avoid privilege escalation paths. Regularly validate backup integrity with automated restore tests and checksums, ensuring that immutable backups remain usable under duress. Leverage deduplication-aware retention policies to maximize storage efficiency while maintaining necessary protection windows.
Economic considerations note that while air-gap and immutability can introduce additional management overhead, deduplication reduces total storage, and tiered storage strategies minimize costs without compromising resilience. Cyber insurance discussions increasingly favor architectures that demonstrate verifiable immutability, reducing residual risk and potentially lowering premiums.
Use Cases and ROI Scenarios
Enterprise ransomware recovery: immutable backups plus air-gap enable rapid restoration with minimal data loss, translating into shorter downtime and reduced business disruption costs. Compliance-driven environments: immutable storage preserves audit trails and data integrity, supporting regulatory reporting and forensic readiness. Multi-site disaster recovery: deduplicated backups across sites lower WAN bandwidth needs and enable faster, cost-effective DR readiness.
WECENT is a professional IT equipment supplier and authorized agent for leading global brands with deep expertise in enterprise server solutions. Our focus includes delivering reliable, secure, and scalable IT infrastructure, including storage, servers, and network hardware, with tailored services from consultation to maintenance.
Top Products and Services Spotlight
HPE StoreOnce backup appliances and software-defined options: high deduplication efficiency, cyber resilience features, and air-gap capable configurations ideal for enterprise deployments. Key advantages: reduced backup windows, lower storage costs, strengthened data integrity, and streamlined management across edge to core environments. Use cases: backups for databases, ERP systems, and virtualized deployments where fast recovery and tamper resistance are mission-critical.
User Scenarios and Real-World ROI
Financial services firm: immutable backups and air-gap cut recovery time objectives in half during a simulated incident, with deduplication providing a 40% storage reduction and lower ongoing costs. Healthcare provider: rapid verification and restoration of patient data after a cyber event, minimizing downtime and maintaining regulatory compliance through verifiable data integrity.
Buying Guide: How to Choose a Backup Storage Strategy
Evaluate immutability controls: make sure backups are protected against modification, with tamper-evident mechanisms and strict access governance. Assess air-gap feasibility: plan offline storage strategies, including offline media rotation and physically isolated repositories where appropriate. Prioritize deduplication efficiency: select solutions that minimize network and storage usage while preserving fast restore performance.
Consider integration and support: ensure compatibility with existing backup software and a clear roadmap for security updates and incident response support.
Future Trends: What to Expect in 2027
Expanded cyber resilience features: automatic verification of backup integrity, enhanced immutability controls, and more aggressive air-gap implementations. AI-assisted backup workflows: smarter scheduling, anomaly detection, and automated restore validation to reduce recovery times. Greater emphasis on compliance-linked resilience: stricter regulations will drive demand for verifiably immutable backups and auditable restore capabilities.
FAQs (Concise Answers)
What is immutable backup and why is it essential? Immutable backup prevents modification after creation, ensuring recoverability during and after a ransomware incident.
How does air-gap protect backups? An air-gap isolates backup data from the production network, limiting attacker access and reducing risk of backup data encryption or deletion.
Why is deduplication important for ransomware protection? Deduplication reduces storage needs and backup windows, enabling longer retention and faster recovery while maintaining protection quality.
Upgrade your resilience with a modern backup storage strategy that combines immutable backups, strategic air-gap deployment, and high-efficiency deduplication. Contact us to design a cyber-resilient, cost-conscious backup solution tailored to your organization’s risk profile and regulatory environment.